Attackers could have had full control over DT’s Web server. Independent Egyptian security researcher Ebrahim Hegazy has found another vulnerability, and this one affected the Web servers of Deutsche Telekom, Germany’s biggest telecommunications provider.
Hegazy discovered the bug on the telekom.de website, on one of the subdomains that displayed a generic landing page. The subdomain umfragen.telekom.de translates to suggestions.telekom.de, and seems to be an abandoned Web page left behind from previous site iterations.
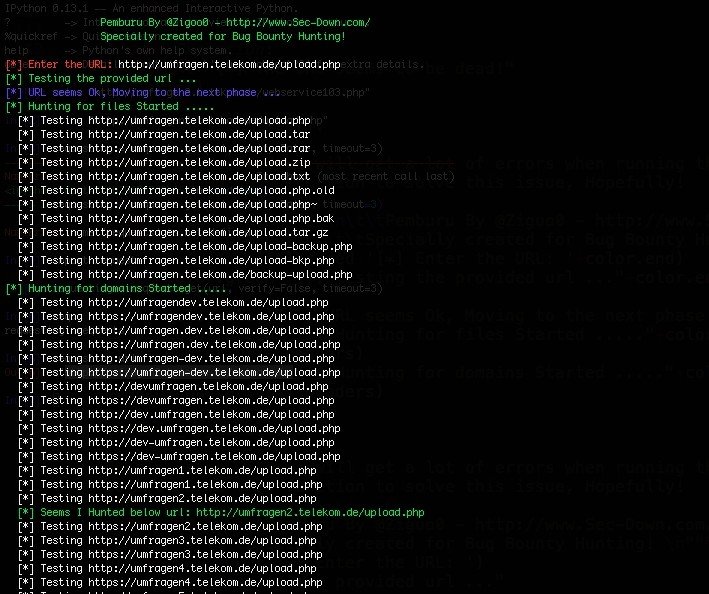
The researcher used a tool specifically designed to find security bugs
Having brute-forced the URL, Hegazy came across an upload.php file. Using a tool he specifically built for pen testing, called Pemburu, Hegazy managed to find the URL to which the upload.php file sent user-submitted data.
His tool went through a large set of URL variations and eventually discovered that the file sent data to umfragen2.telekom.de/upload.php.
Accessing this file directly allowed Hegazy to take a closer look at the code. Here he came across a mechanism that acquired user input from the HTTP POST request without sanitizing it in any way and then attached the data as parameters to the PHP system()function.
This particular function is modeled after the system function in C and allows PHP developers to execute shell commands from inside their PHP app and retrieve the results. Generally, it’s considered a good practice not to use this function on any front-facing Web server.
Attackers could have gained full control of the Deutsche Telekom server
From here on out, Hegazy created a malformed HTTP POST request and executed a test command on Deutsche Telekom’s server. Hegazy used the exploit to create a file named zigoo0.php, but more malicious and dangerous bash commands could have been executed as well.
This is the most basic example of an RCE (remote code execution) vulnerability, one that allows attackers to gain full control of a Web server just by pinging its ports and open connections with malicious requests.
With his test successful, he informed the telco’s security team, who in less than two days fixed the issue. Mr. Hegazy told Softpedia that his research was carried out as part of the company’s bug bounty program and received a €2,000 / $2,150 reward.
If you’d like to get your hands on his Pemburu pen testing tool, the code is available on GitHub. This tool was created a few weeks ago, when he found another RCE bug, this onein Magento’s installation package.
Hegazy is a constant presence here, on Softpedia’s Security News section, having previously reported on the bugs he discovered in products and services like Microsoft, Twitter, Yahoo, PayPal, and many other more.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.