At the recent ShmooCon conference a researcher presented a LastPass phishing attack that could allow hackers to steal your password.
We discussed several times the importance of password managers such as LastPass, but sometimes hackers could exploit them to launch their attacks.
The security researcher Sean Cassidy has presented on Saturday at the ShmooCon hacker conference in Washington a new phishing attack scheme that could allow an attacker to access all passwords stored by a user of the popular LastPass password manager. Cassidy called LostPass his LastPass phishing attack.
“LostPass works because LastPass displays messages in the browser that attackers can fake. Users can’t tell the difference between a fake LostPass message and the real thing because there is no difference. It’s pixel-for-pixel the same notification and login screen” wrote Cassidy in a blog post.
The LastPass phishing technique could allow an attacker to take over user accounts even if protected by the two-factor authentication.
Cassidy explained that this particular attack is feasible because LastPass is vulnerable to a cross-site request forgery that allows any site to send the application a logout notification.
Cassidy demonstrated how users can be tricked into submitting both their LastPass master password and their 2nd-factor authentication code, the attack method relies on a malicious server and exploits bogus pop-up notifications to fool the victims.
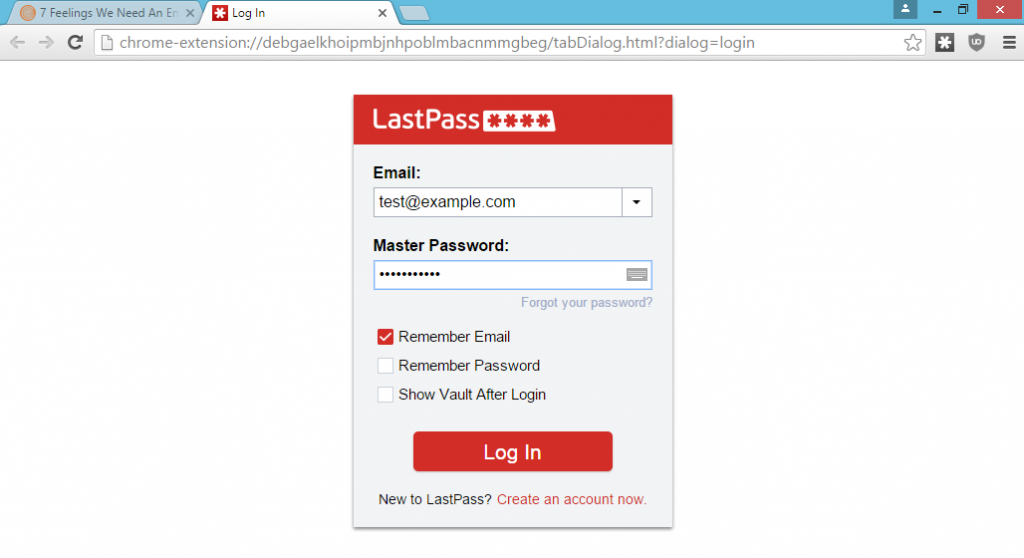
The LastPass phishing attack starts when the user visits a bogus website running javascript code that generates in the victim’s browser a notification informing him he has been logged out of LastPass application. The message appears as legitimate and redirects victims to a fake LastPass login screen.
The fake login page requests the user entering his master password and the 2-factor authentication code, if the victim has enabled it.
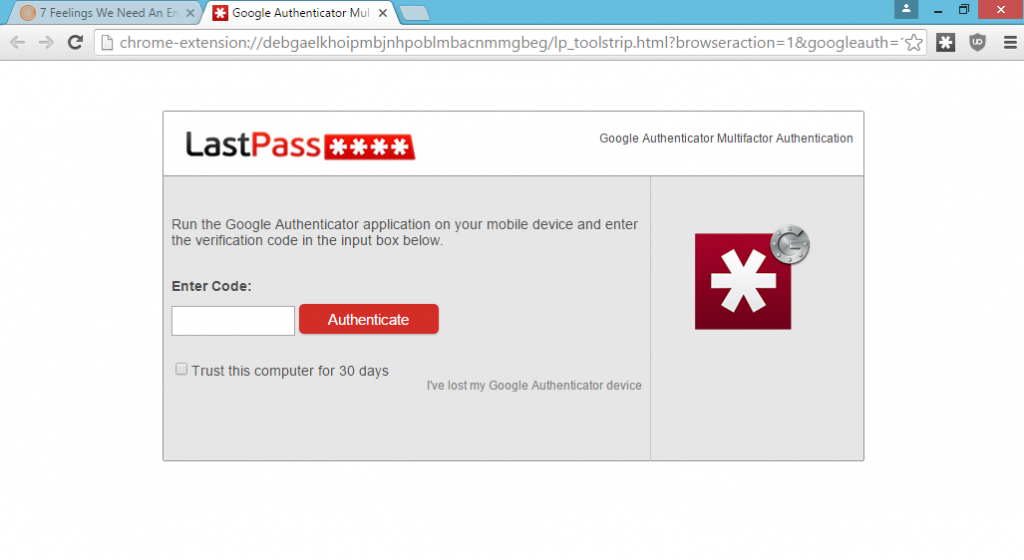
When the victim submits the information requested they are sent to a web server controlled by the attacker.
The attacker can use the information to access LastPass’ API and use the credentials to download and decrypt the victim’s password.
Cassidy explained that LastPass, differently from other password managers like KeePass, encourages users to keep an encrypted backup of their password vault on its servers, this choice allows users to sync with multiple devices, but also enlarge their surface of attack. An attacker that is able to access the user’s LastPass login credentials can get a copy of the password file.
Similar attacks against LastPass users are not a novelty, in 2015 the experts Garcia and Vigo developed a technique called “Even the LastPass Will be Stolen, Deal with It!.”
“My work comes at LastPass from a different angle: you don’t have access to a LastPass user’s machine. Instead, you trick the user into giving you their credentials.” Cassidy explained.
The researcher reported the issue to LastPass in November, and its experts acknowledged the flaw in December.
LastPass has already released an update that mitigates this kind of phishing scheme avoiding users from being logged out and implemented a security alert to warn users when they’ve entered their master password into a fake LastPass form.
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











