The security researcher Kafeine confirmed that the authors of the Angler EK have integrated the exploit for a recently patched Microsoft Silverlight vulnerability.
Ransomware is becoming one of the most dreaded cyber threats for netizens, security experts noticed a surge in the number of cyber attacks aimed to spread malware like Cryptowall and TeslaCrypt. Exploit kits like the Nuclear EK and the Angler EK are the privileged vectors to serve this specific family of malware, cyber criminals constantly improve their code in order to compromise the largest possible number of victims.
The security expert Kafeine has recently discovered that the authors of the Angler EK have added the code of a Silverlight exploit leveraging on the CVE-2016-0034 vulnerability.
The flaw was fixed by Microsoft in January with the MS16-006 critical bulletin, an attacker can exploit it for remote code execution. The Silverlight flaw discovered by the experts in Kaspersky Lab as a result of an investigation on the Hacking Team arsenal disclosed in July 2015.
According to Microsoft, the remote code execution vulnerability can be exploited by an attacker that set up a website to host a specially crafted Silverlight application.
When Microsoft users will visit the bogus website, the exploit will allow an attacker to obtain the same permissions as the victim.
On February 18, 2016, Kafeine noticed that the author behind Angler had added code for the Silverlight exploit, according to the expert the integration was completed on February 22.
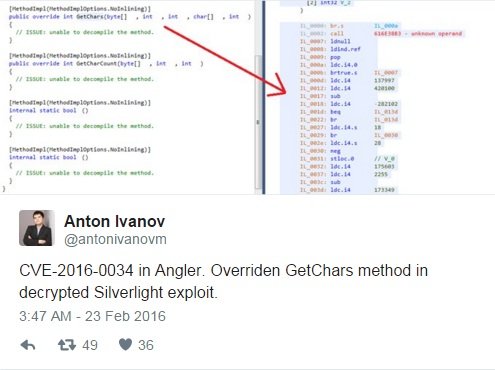
Anton Ivanov, a senior malware researcher at Kaspersky confirmed that an exploit for the Silverlight exploit has been integrated to the Angler EK.
Kafeine explained that the CVE-2016-003 exploit has been used to spread a variant of the TeslaCrypt ransomware, the attacks works only with Silverlight version previous the current one, Silverlight 5.1.41212.0.

The experts at Ars Technica who analyzed the HAcking Team’s leaked emails noticed communications between a Russian developer named Vitaliy Toropov and the staff of the Hacking Team.
The man sold an Adobe Flash Player exploit to the Hacking Team for $45,000 in 2013 and also offered a Silverlight exploit.
“Now your discount on the next buy is -5k and -10k is for a third bug. I recommend you the fresh 0day for iOS 7/OS X Safari or my old Silverlight exploit which was written 2.5 years ago and has all chances to survive further in next years as well. ” Toropov wrote to Hacking Team member Giancarlo Russo.
Experts at Kaspersky started analyzing Toropov’s exploits, including a Silverlight Microsoft Silverlight Invalid Typecast / Memory Disclosure that was dated back 2013 and that he had published.
Kaspersky issued a YARA rule to detect the exploit in the wild, and on November 25th, the company detected the Toropov’s exploit on a user’s machine. Later another sample of the exploit was uploaded from Laos to a multiscanner service.
“After implementing the detection, we waited, hoping that an APT group would use it. Since Vitaliy Toropov was offering it to Hacking Team, we also assumed that he sold it to other buyers, and what good is a zero-day if you don’t use it? Unfortunately, for several months, nothing happened. We had already forgotten about this until late November 2015.” Kaspersky researchers wrote in a blog post. “On November 25th, one of our generic detections for Toropov’s 2013 Silverlight exploit triggered for one of our users. Hours later, a sample was also uploaded to a multiscanner service from Lao People’s Democratic Republic (Laos).”
The analysis of the exploit revealed that the exploit was compiled on July 21, 2015, after the Hacking Team data was leaked online. Kaspersky immediately reported the existence of the exploit to Microsoft.
It’s unclear if this Silverlight exploit is the same offered by Toropov in 2013,
“One of the biggest questions we have is whether this is Vitaliy Toropov’s Silverlight zero-day which he tried to sell to Hacking Team. Or is it a different one? Several things make us think it’s one of his exploits, such as the custom error strings. Of course, there is no way to be sure and there might be several Silverlight exploits out there. One thing is for sure though – the world is a bit safer with the discovery and patching of this one.” wrote Kaspersky researchers.
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











