Cerber ransomware distributed as a Raas service. The latest addition to the ransomware spectrum is a new threat called Cerber that encrypts users files, and then provides a TTS (text-to-speech) feature that reads out the ransom note.
First signs of Cerber infections appeared last week, and according to security firm SenseCy, the ransomware is the product of a team of Russian coders that are advertising it as a RaaS service via underground hacking forums in Russia.
RaaS stands for Ransomware-as-a-Service and is a new business model for ransomware operators in which they provide ready-coded ransomware and allow other criminals to distribute it via spam and spear-phishing campaigns. The original coders take a small percentage, but only when the victim pays the ransom.
It is unknown if current crooks spreading the recent wave of Cerber ransomware are using malvertising or spam campaigns.
Cerber intentionally avoids Russian-speaking countries
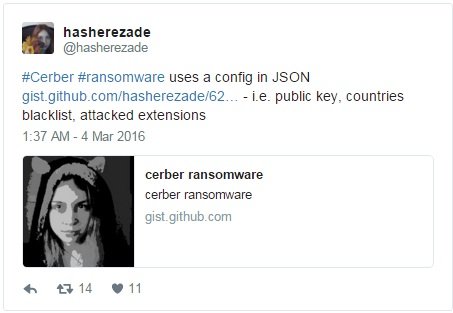
Security researchers that took a look over the Cerber code said it was specifically built to avoid infections of users living in former Soviet countries.
Another kink in Cerber’s operations is the fact that the ransomware, before encrypting files, shows an error prompt through which it fools the user into restarting the computer. The ransomware forces the PC to restart in “Safe Mode with Networking” and then forcibly restarts the computer again in normal mode.
After this forced restart, Cerber starts encrypting files with an AES algorithm. The ransomware targets 380 file types and during the encryption process scrambles the file’s name and adds the .cerber extension at the end. Currently, the Cerber ransomware is undecryptable.
Cerber’s ransom note speaks to you
Once the encryption process finished, the ransomware drops three notes in text, HTML, and VBS format in each folder where it encrypted data. The VBS ransom note, if opened, will recite the ransom note to the user.
The ransom note asks for 1.24 Bitcoin ($520 / €475), a sum which doubles after the first week. As usual, users need to pay the ransom in Bitcoin over a Dark Web URL (.onion domain).
The ransomware was discovered by two independent security researchers@BiebsMalwareGuy and @MeegulWorth, and was analyzed by researchers from Bleeping Computer and Malwarebytes.

Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











