Legitimate code-signing certificates provide secret cover for attack groups. There are lots of ways to ensure the success of an advanced hacking operation. For a gang called Suckfly, one of the keys is having plenty of stolen code-signing certificates on hand to give its custom malware the appearance of legitimacy.
Since 2014, the group has used no fewer than nine separate signing certificates from nine separate companies to digitally sign its hacking wares, according to a blog post published Tuesday by security firm Symantec. Company researchers first came upon the group last year when they identified a brute-force server message-block scanner that was signed with a certificate belonging to a South Korean mobile software developer. When the researchers searched for other executable files that used the same credential, they eventually uncovered three more custom tools from the same group of black-hat hackers.
After tracing the hacking group’s traffic to IP addresses in Chengdu, China, Symantec researchers ultimately identified a much larger collection of custom-developed backdoors and hacking tools that were signed by nine different certificates from nine different companies. Curiously, all nine of the compromised companies are located within a few miles of each other in Seoul. While the physical proximity is suspicious, the researchers ultimately speculated the certificate thefts weren’t the result of any physical attack and were most likely the result of the owners being infected with malware that had the ability to search for and extract signing certificates.
It’s by no means the first time advanced malware outfits have used stolen certificates. The Stuxnet worm that disrupted Iran’s nuclear program six years ago was signed with legitimate certificates from companies located in Taiwan. Malware dubbed Winnti that came to light in 2013 targeting more than 30 online video game companies also used stolen certificates, as did an advanced persistent threat group known as Hidden Lynx that was exposed the same year. Black Vine, a separate APT group responsible for the devastating 2014 breach of health insurer Anthem, is yet another example. Sometimes, software developers inadvertently publish their signing keys, as was the case in September with modem manufacturer D-Link.
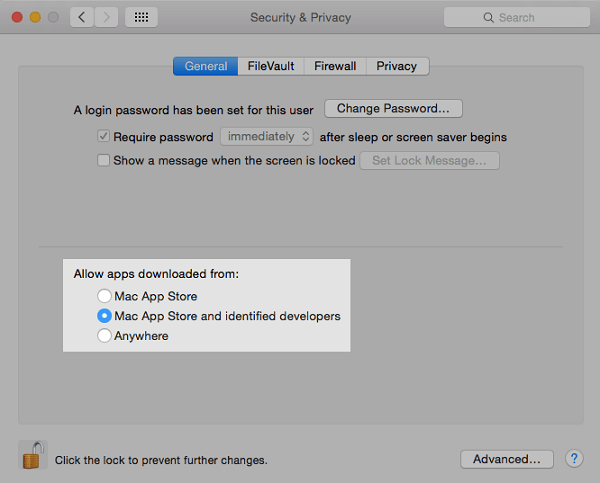
The certificate-theft attacks come as operating systems increasingly make code signing a requirement for installing apps.
“Signing malware with code-signing certificates is becoming more common, as seen in this investigation and the other attacks we have discussed,” Symantec researcher Jon DiMaggio wrote in Tuesday’s blog post. “Attackers are taking the time and effort to steal certificates because it is becoming necessary to gain a foothold on a targeted computer. Attempts to sign malware with code-signing certificates have become more common as the Internet and security systems have moved towards a more trust and reputation oriented model. This means that untrusted software may not be allowed to run unless it is signed.”
Digitally signed certificates allow Suckfly exploits to work seamlessly without calling attention to themselves. One of the group’s booby-trapped webpages, for example, was able to exploit a 2014 vulnerability in a Microsoft Windows component known as Object Linking and Embedding when it was viewed with Internet Explorer. The file the exploit delivered was a self-extracting executable that ultimately installed malware Symantec dubs Nidiran.
“Our investigation shines a light on an often unknown and seedier secret life of code-signing certificates, which is completely unknown to their owners,” DiMaggio concluded. “The implications of this study shows that certificate owners need to keep a careful eye on them to prevent them from falling into the wrong hands. It is important to give certificates the protection they need so they can’t be used maliciously.”
Source:https://arstechnica.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.