McAfee patches flaws in its Linux security solution. Remote code execution flaws found in McAfee VirusScan Enterprise for Linux could allow an attacker to obtain root privileges, and a security researcher says that it’s all possible by simply tricking the app to use malicious update servers.
Andrew Fasano from MIT Lincoln Laboratory said in a post that he first discovered the vulnerabilities in McAfee’s solution nearly six months ago, but the security company patched them only earlier this month.
“At a first glance, Intel’s McAfee VirusScan Enterprise for Linux has all the best characteristics that vulnerability researchers love: it runs as root, it claims to make your machine more secure, it’s not particularly popular, and it looks like it hasn’t been updated in a long time,” he explained.
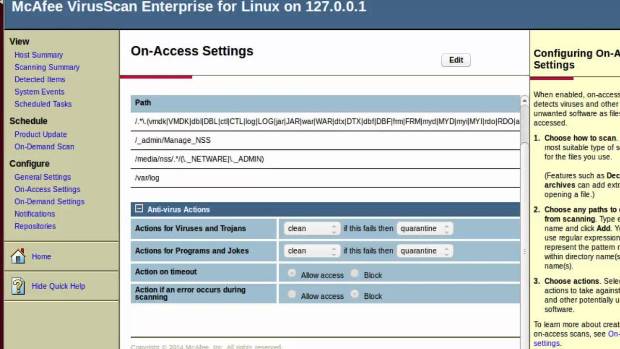
In his post, Fasano explains that once the app connects to the compromised update servers, McAfee VirusScan Enterprise for Linux allows the deployment of a script that can be launched on the target machine with root privileges.
10 different vulnerabilities, 4 of which lead to privilege escalation
There are 10 different vulnerabilities in McAfee’s Linux security solution, but the researcher says that only 4 of them are required to successfully breach a Linux system.
The first two flaws, which are known as CVE-2016-8016 and CVE-2016-8017 (Remote Unauthenticated File Existence Test and Remote Unauthenticated File Read with Constraints) make it possible for hackers to compromise the authentication token used by McAfee’s VirusScan Enterprise and run malicious update servers on Linux machines.
The script that would eventually help obtain root privileges is deployed with the help of CVE-2016-8021 (Web Interface Allows Arbitrary File Write to Known Location). When combined with CVE-2016-8020 (Authenticated Remote Code Execution & Privilege Escalation), an attacker can obtain a privilege escalation flaw, the researcher notes.
“Using CSRF or XSS, it would be possible to use these vulnerabilities to remotely privesc to root,” he explains.
All these vulnerabilities have already been confirmed in version 1.9.2 to 2.0.2, so all Linux systems are recommended to update to the latest release that McAfee shipped this month.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.