The Android Security Bulletin for March 2017 contains a bugfix for a unique security flaw exploitable via the headphones audio connector that could be leveraged to leak data from the device, break ASLR, reset phones to factory settings, or even access the Android HBOOT bootloader.
Discovered by Roee Hay and Sagi Kedmi, two researchers from Aleph Security, the issue derives from research presented at the Black Hat security conference in 2013, when security experts showed how to use multiplexed wired interfaces to connect and interact with Android smartphones.
Their research focused on accessing devices via USB ports without using the actual USB software interface. In section 5 of their research, the team only briefly touched on the concept of accessing devices via the audio jack connector, using a modified UART cable.
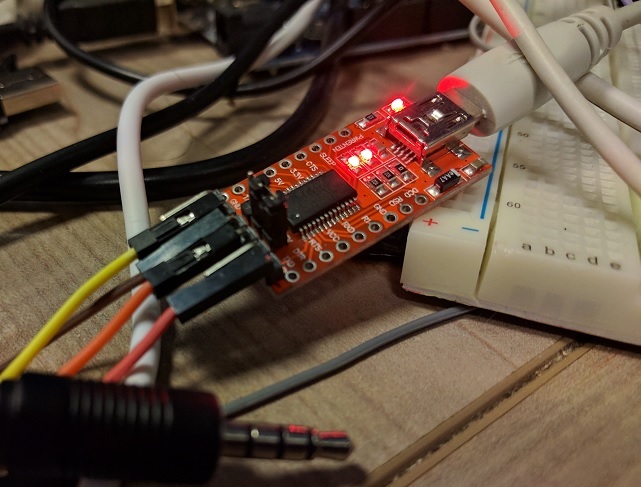
Now, the Aleph team has expanded on their work, and using a similarly modified UART cable that was connected to an audio jack, they say they successfully accessed the FIQ (Fast Interrupt Request) Debugger on a Nexus 9 device.
According to researchers, this FIQ Debugger does not need a reboot to become active and is available and responsive to commands even if the Android OS is already up and running. This simplifies exploitation compared to similar multiplexed wired attacks.
Furthermore, the debugger responds to a wealth of commands, allowing the attacker to:
- access a help menu (in case he needs help hacking your phone)
- dump the process list
- dump the registers
- leak the Stack Canary value (of the Zygote core process)
- view arbitrary CPU contexts with memory addresses (and break ASLR)
- access the sysrq interface (which provides additional commands not available in the FIQ Debugger)
- access the Nexus 9 HBOOT bootloader
- access I2C buses and interact with the phone’s internal System-on-Chips (SoCs)
- trigger a factory reset
Tracked as CVE-2017-0510, Google evaluated the vulnerability as “Critical,” it’s highest severity level. The reason for a critical level classification is because attackers can corrupt the phone’s OS, which may need users to reflash (reinstall) their operating system.
While the March 2017 Android Security Bulletin is scarce on details, Hay says “Google patched the vulnerability by reducing the capabilities of the FIQ Debugger.”
In unrelated Android security news, Google has also pulled the Android OS images for Nexus 6 devices this week, after the March security update, released on Monday, broke Android’s SafetyNet API, a crucial security feature. Nexus 6 device owners will have to wait for the March security updates a while longer.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











