A Pennsylvania judge has sentenced Adam Flanagan, 42, of Bala Cynwyd, PA to one year and one day in prison for hacking and damaging the IT networks of several water utility providers across the US East Coast. The sentence was passed down last week for crimes committed in the spring of 2014.
According to court documents obtained by Bleeping Computer, Flanagan worked between November 2007 and November 2013 for an unnamed company that produced smart water, electric, and gas readers.
Flanagan’s role with the company was as an engineer tasked with setting up Tower Gateway Basestations (TGB) for the manufacturer’s customers, which were mainly water utility networks. In modern water grids, TGBs collect data from smart meters installed at people’s homes and relay the information to the water provider’s main systems, where it is logged, monitored for incidents, and processed for billing.
Flanagan disabled water reader base stations
Things turned sour when Flanagan’s employer fired him on November 16, 2013, for undisclosed reasons. This didn’t sit well with Flanagan, who used his knowledge of the TGB stations he installed to access these devices and disable their ability to communicate with their respective water utility providers’ upstream equipment. The former employee also changed passwords to offensive words on some TGBs.
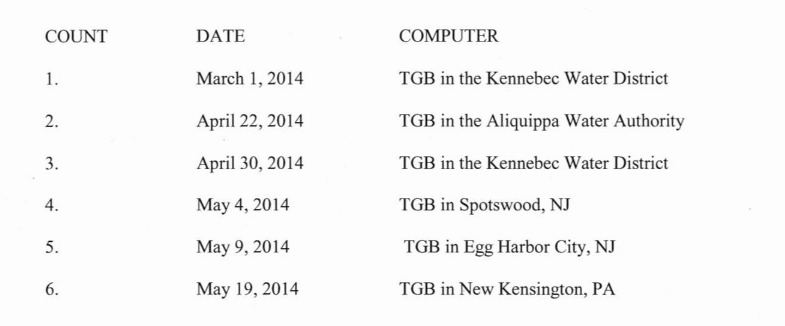
According to court documents, the FBI tracked down Flanagan’s actions to six incidents in five cities across the US East Coast: Aliquippa (Pennsylvania), Egg Harbor (New Jersey), Kennebec (Maine), New Kensington (Pennsylvania), and Spotswood (New Jersey).
Flanagan’s attacks resulted in water utility providers not being able to collect user equipment readings remotely. This incurred damage to the utility providers, who had to send out employees at customer premises to collect monthly readings.
Flanagan faced up to 90 years in prison, $3 million fine
After tracing the attacks back to Flanagan, US authorities filed charges on November 22, 2016, and arrested the suspect and seized his computer a day later.
At the time of his arrest, Flanagan faced a maximum sentence of 90 years in prison, plus a $3 million fine. He pleaded guilty on March 7, 2017, before receiving his sentence on June 14, 2017.
Flanagan is not the first employee to sabotage his employer, nor will he be the last. Similar cases include incidents like:
⬩ A former sysadmin who decided to delete his company’s servers and change former colleagues’ passwords on the day he was fired.
⬩ Or, a former IT employee who altered his former employer’s equipment settings, bringing a paper mill’s production to a halt.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











