Experts believe a state-sponsored hacker was behind the attack, which affected 2.2 million people.
The recent attack that resulted in 2.2 million users installing infected versions of a popular Windows system optimization tool might have been the work of a sophisticated cyberespionage group with a history of software supply chain compromises.
Researchers from two security companies have established links between the malicious code surreptitiously added to the program’s installer and malware previously used by a prolific group of Chinese hackers that once broke into Google’s corporate infrastructure.
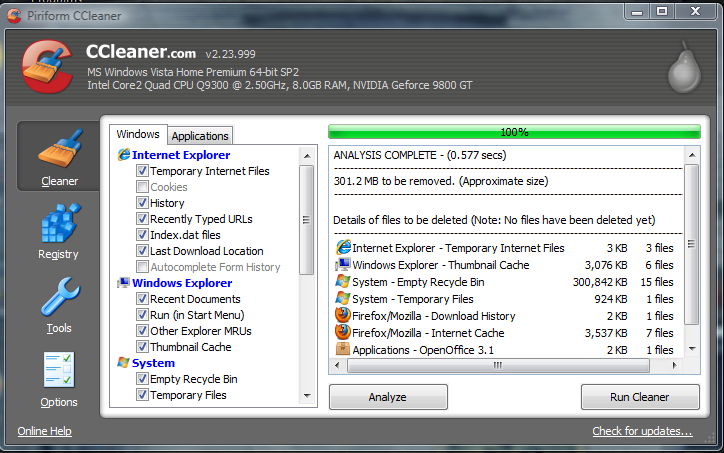
On Monday, it was revealed that the official and digitally signed installers for two versions of CCleaner—a utility for removing temporary files and invalid registry entries on Windows computers—contained a backdoor program capable of installing additional malware. These malware-laden programs were distributed between August 15 and September 12.
The fact that the malicious code was added to CCleaner before it was compiled suggests that hackers gained access to the development infrastructure of Piriform, the company that makes the tool. Piriform was acquired in July by antivirus maker Avast.
As far as the malicious code found in CCleaner is concerned, there is overlap with APT17/Aurora, Costin Raiu, director of the Global Research and Analysis Team at antivirus vendor Kaspersky Lab, who analyzed the malware, told me.
APT17, also known as DeputyDog, is a cyberespionage group that has been operating for over a decade. Over the years, the group has hacked into government entities, non-government organizations, law firms and companies from various industries, including defense, information technology and mining. The group was also behind Operation Aurora, a high-profile attack in 2009 that affected Google and over 30 other companies.
The backdoor included in the 32-bit versions of CCleaner v5.33.6162 and CCleaner Cloud v1.07.3191 was designed to gather identifying information about the infected computers and send it to a hard-coded IP address. If the server was unreachable, the malware would generate random-looking domain names based on a special algorithm and attempt to contact those.
Attackers often use a lightweight malware program for the first stage of an infection in order to perform reconnaissance and gather information from the infected systems in order to identify potentially interesting targets for which they will then deliver more specialized malware. Information such as process lists can help identify which security products are running and must be evaded while computer and domain names can reveal the organizations the affected systems belong to.
The backdoor program included with CCleaner also attempted to download and execute additional malware from the command-and-control server. Cisco Systems’ Talos group confirmed in a new report Wednesday that at least 20 victim machines belonging to high-profile technology companies were served such secondary payloads.
Jay Rosenberg, a researcher with security firm Intezer also confirmed that the CCleaner backdoor has code that’s identical to that used in APT17’s past malware tools. Intezer’s technology is specifically designed to find code similarities in malware.
“The code in question is a unique implementation of base64 [encoding] only previously seen in APT17 and not in any public repository, which makes a strong case about attribution to the same threat actor,” Rosenberg wrote in a blog post.
Raiu also pointed out that while the code overlaps with APT17, the command-and-control infrastructure used matches that of a newer attack group. However, there is a connection between these the two groups, as they’re both tied to a larger cyberespionage organization known in the security industry as Axiom.
Axiom was documented in 2015 by threat analytics firm Novetta in partnership with other security vendors. It is a sort of umbrella group responsible for many cyberespionage campaigns over many years and which Novetta believes are coordinated by China’s intelligence apparatus.
“FireEye found infrastructure overlap with a nation state threat actor,” Christopher Glyer, the chief security architect at security firm FireEye, said in a public discussion on Twitter about the CCleaner incident. “CCleaner is used in lots of orgs (even if primarily consumer focused). Supply chain compromise is a perfect vector for a nation state to use,” he said in another message.
FireEye did not immediately respond to a request for more information, but Glyer raises a good point: If this was a cyberespionage operation—and evidence found so far suggests it was—then the primary targets were likely CCleaner’s business users.
Source:https://motherboard.vice.com/en_us/article/7xkxba/researchers-link-ccleaner-hack-to-cyberespionage-group

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











