A HomeKit vulnerability in the current version of iOS 11.2 has been demonstrated to 9to5Mac that allows unauthorized control of accessories including smart locks and garage door openers. Our understanding is Apple has rolled out a server-side fix that now prevent unauthorized access from occurring while limiting some functionality, and an update to iOS 11.2 coming next week will restore that full functionality.
The vulnerability, which we won’t describe in detail and was difficult to reproduce, allowed unauthorized control of HomeKit-connected accessories including smart lights, thermostats, and plugs.
The most serious ramification of this vulnerability prior to the fix is unauthorized remote control of smart locks and connected garage door openers, the former of which was demonstrated to 9to5Mac.
The issue was not with smart home products individually but instead with the HomeKit framework itself that connects products from various companies.
Users need to take no action today to resolve the issue as the fix that is rolling out is server-side. The future update to iOS coming next week will resolve any broken functionality.
The vulnerability required at least one iPhone or iPad on iOS 11.2, the latest version of Apple’s mobile operating system, connected to the HomeKit user’s iCloud account; earlier versions of iOS were not affected.
We also understand that Apple was informed about this and related vulnerabilities in late October, and some but not all issues were fixed as part of iOS 11.2 and watchOS 4.2 which were released this week. Other issues in this category were fixed server-side from Apple so end users needed to take no action.
Apple shared this statement with 9to5Mac regarding the issue:
“The issue affecting HomeKit users running iOS 11.2 has been fixed. The fix temporarily disables remote access to shared users, which will be restored in a software update early next week.”

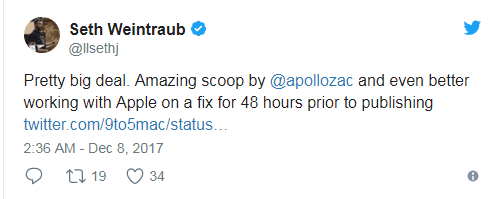
We believe this vulnerability being brought to our attention has resulted in the solution being readied sooner than it otherwise would have been, and our readers deserve to know that the vulnerability existed. The severity of this vulnerability also imposes a responsibility on 9to5Mac as a publication to share what we know with our audience if we’re going to continue covering HomeKit and smart home products.
Does this vulnerability shipping mean you shouldn’t trust HomeKit or smart home products going forward? The reality is bugs in software happen. They always have and pending any breakthrough in software development methods, they likely always will. The same is true for physical hardware which can be flawed and need to be recalled. The difference is software can be fixed over-the-air without a full recall.
Trusting HomeKit and smart home products with your security, however, will have to be a personal decision now just like it always has. Personally, once this vulnerability has been patched, I believe I’ll be comfortable with trusting HomeKit security solutions to remain protected, but you can always use an old fashioned lock and key or install security cameras as a double measure.

I would also like to know — just like with the root security issue that affected the Mac last week — that the development process that led to this vulnerability shipping and the issue remaining live for weeks without users knowing is audited and changes are made if possible.
The bottom line is if a HomeKit connected lock or garage door opener knowingly can’t secure your home, customers shouldn’t be given the opportunity to test the risks associated with any known vulnerabilities.
Our hope in publicizing this specific vulnerability is that we may have a meaningful impact in improving the quality assurance and security audit processes so that HomeKit can be a better solution in the future and live up to its reputation as being the most secure smart home framework.
Source:https://9to5mac.com/2017/12/07/homekit-vulnerability/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.