It is a good habit to keep your eyes open and monitor the updates to your favorite tools. Information security professionals recommend do it ‘religiously’ and comb the internet for the updates every once in a while.
You definitely used Sysinternals tools, including the Process Explorer, and the Rootkit Revealer. You might have heard, or used GMER. This is the same for the RKU and for the Kernel Detective.
At least three of these tools were amazingly popular in the first decade of this century as they allowed poking around things that other tools could only dream of. They were really ahead of a curve as they allowed accessing the system in a nearly forensically-sound manner, unhook kernel and user mode hooks, scan the whole memory for badness and overall, really help to deal with a lot of nasty code from those days.
Most of the aforementioned tools are kaput.
Enter Process Hacker, a much better tool than Process Explorer.
While the official build is 2.39 and is 2 years old, there is a ‘nightly’ build you can always try to play with:
https://wj32.org/processhacker/nightly.php
The last build is 3.0.1424 and is from 18/April/2018.
Now, XueTR/PCHunter.
The information security expert has recently found out that the author released a new version in March 2018. The current version is 1.53 and according to the blog post it was tested with Win10 (16299).
Now, before we begin, please note that the free version of PcHunter works on 32- and 64- bit Windows 10, and can’t be used commercially.

With that out of the way, we can explore the main interface. When you execute the main 64-bit .exe (PCHunter64.exe) you will be presented with a UI:
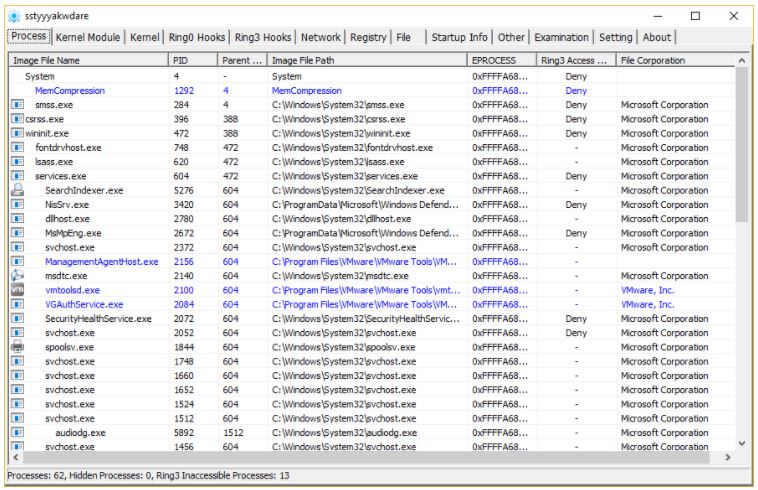
The interface is similar to GMER/RKU and to Kernel Detective, information security researchers said. There is a bunch of tabs we can browse through and which explore the Windows 10 internals in details:
- List of processes
- Kernel Modules
- Kernel ‘Stuff’
- Notify routines
- Filter
- DPC Timer
- Worker thread
- Hal
- Wdf
- File System
- System Debug
- Object Hijack
- Direct IO
- GDT
- Ring0 Hooks (including IRP+inline)
- SSDT
- ShadowSSDT
- FSD
- Keyboard
- I804prt
- Mouse
- Partmgr
- Disk
- Atapi
- Acpi
- Scsi
- Kernel Hook
- Object Type
- IDT
- Ring3 Hooks
- Message Hooks
- Process Hook
- KernelCallbackTable
- Network
- Port
- Tcpip
- Nsiproxy
- Tdx
- Ndis Handler
- IE Plugin
- IE Shell
- SPI
- Hosts file
- Registry (browser)
- File (system browser)
- Startup Info
- Startup
- Services
- Scheduled task
- Other
- File Association
- IFEO (Image File Execution Options)
- IME/TIP
- Firewall Rule
- User Name
- Other (additional tools)
- Examination (forensic-like report)
- Setting
- About

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











