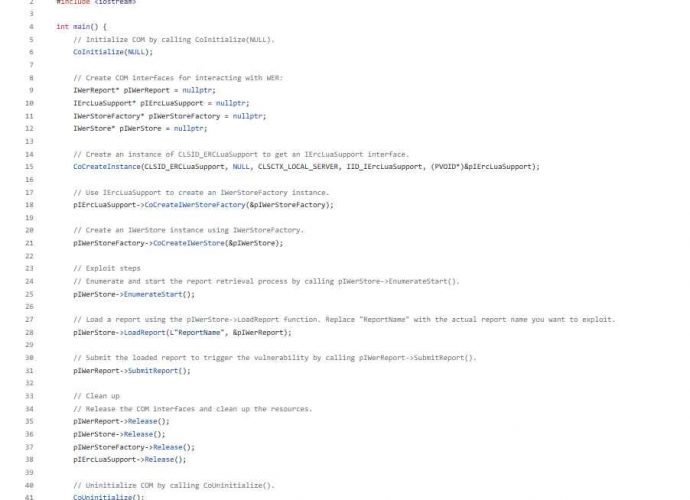
Hacking Cisco Routers firmware and replacing it with a malicious firmware using this flaw
A notorious threat actor with presumed ties to the Chinese government, known as “BlackTech”, has reportedly been exploiting Cisco routers to infiltrate major corporations in the United States and Japan,Read More →