Sysadmins should disable OLE object execution. Malware coders have found a macro-like infection method that abuses the Microsoft Object Linking and Embedding (OLE) system to trick users into running malicious scripts.
The Microsoft Object Linking and Embedding (OLE) system is a proprietary Microsoft technology used in some of the company’s software products, which allows users to embed, or link to, various types of content inside the said software.
Users usually employ OLE to embed Flash content, graphs, images, and more. One of the objects users can embed is VBScript and JavaScript code.
Malware campaign leverages Office docs with malicious OLE objects
Microsoft says that in late May, its security products started picking up malicious documents attached to spam email that leveraged OLE objects.
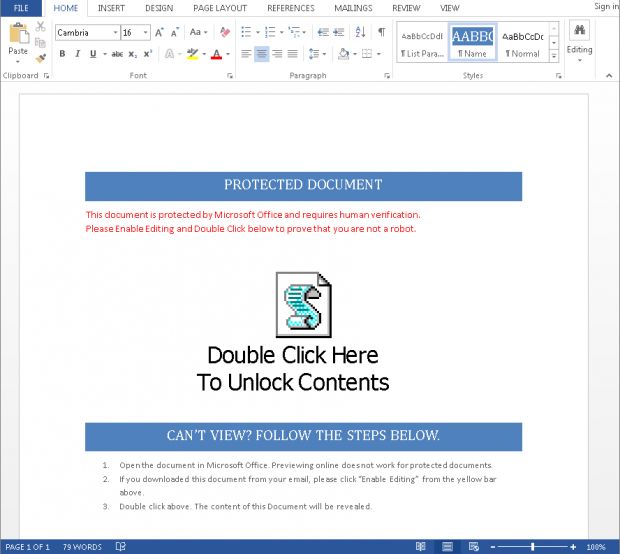
Users that downloaded and opened the Office docs were greeted with a familiar message, seen with many macro malware campaigns.
The crooks were telling users that the file required “human verification” and that he needed to double-click the big icon at the center of the document. Sounds like a macro malware hook, right?
When users double-clicked the icon, as instructed, a popup would appear asking the user if he wanted to run the object, which in this case could have been either a JavaScript or a VBScript file.
Both scripting languages are very well supported in Windows and have access to powerful system-level commands.
Scripts were downloading the Vibrio and Donvibs trojans, then Cerber
For this particular campaign, the malicious scripts downloaded an encrypted binary. The scripts also managed to bypass network-based protections designed to detect malicious data formats.
The scripts then saved the encrypted binary on disk, decrypted its content, and executed it, effectively installing either the Vibrio or the Donvibs trojans.
These two are malware droppers, designed for the sole purpose of gaining an initial foothold and then downloading more potent malware after they gained boot persistence on the target’s machine. Microsoft says that in this case, the final payload was the Cerber ransomware.
Some similarities to macros, some differences as well
Overall, this is a novel approach for tricking users into running malicious code on their PCs. Just like macros, the OLE method relies on social engineering, since a user still needs to click and approve the execution of malicious code, just like users have to enable macro support in Office docs.
Unlike macro malware, the OLE trick has novelty on its side, and most users won’t know that by allowing the JS and VBScripts to run, they are exposing themselves to malware infections.
“It’s important to note that user interaction and consent is still required to execute the malicious payload. If the user doesn’t enable the object or click on the object – then the code will not run and an infection will not occur,” Alden Pornasdoro of the Microsoft Malware Protection Center explains.
“Education is therefore an important part of mitigation – as with spam emails, suspicious websites, and unverified apps. Don’t click the link, enable the content, or run the program unless you absolutely trust it and can verify its source,” he also added.
Despite having newness on its side, Microsoft says that crooks gave up on this approach as time went by, with the number of malicious documents employing this technique dropping by the first week of June.

How to prevent malicious OLE embeds in Office files
Microsoft has also published instructions on how to avoid getting contaminated with malware via malicious OLE objects.
The company recommends that administrators find and edit the following registry key to all their workstations: HKCU\Software\Microsoft\Office\< Office Version >\< Office application >\Security\PackagerPrompt.
The value of < Office Version > can be 16.0 (Office 2016) ; 15.0 (Office 2013) ; 14.0 (Office 2010) ; or 12.0 (Office 2007). The value of < Office application > is the Office application name, usually Word, Excel, and the rest.
The values of the registry key should be “2”, Microsoft says. The value “2” means “No prompt, Object does not execute.” The value of “1” means “Prompt from Office when user clicks, object executes,” while “0” stands for “No prompt from Office when user clicks, object executes.”
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











