ENUM4LINUX:- Enum4linux is used to extract information from Windows and samba hosts, ethical hacking specialists clarifie. The tool is written in Perl and wrapped in samba tools smbclient, rpclient, net and nslookup.
This tool is used by many ethical hackers.
FEATURES OF ENUM4LINUX:-
- Share enumeration
- Password policy retrieval
- Identifying the remote operating system.
- Detecting if host is in workgroup or a domain
- User listing on hosts
- Listing of group membership information
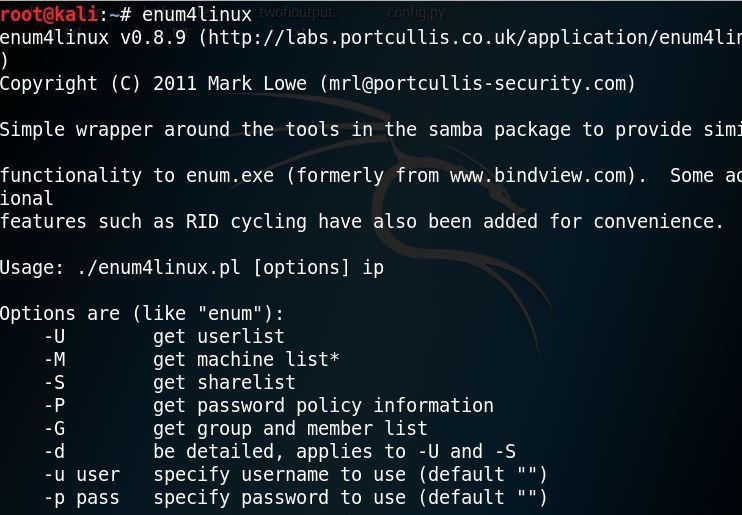
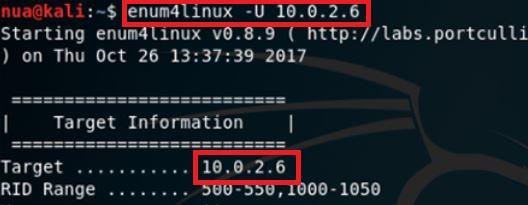
For launching enum4linux:-
- Type enum4linux in linux terminal as shown below.
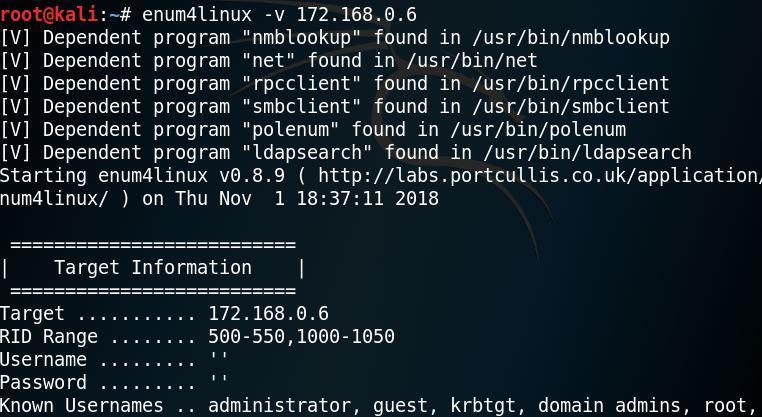
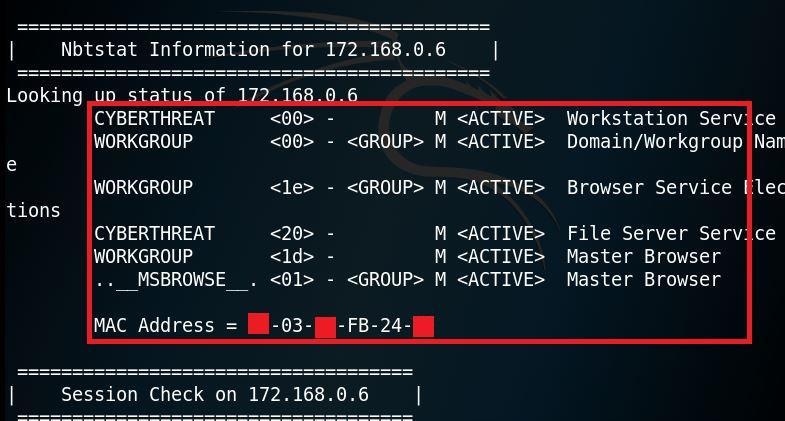
FOR RUNNING IN VERBOSE MODE:-
- Type enum4linux -v 172.168.0.6
=============OUTPUT SNIP==============
- As shown above after executing verbose query for the targeted address. The query has gather information like USER Name, MAC address.
Note:- the mac has marked due to security reasons.
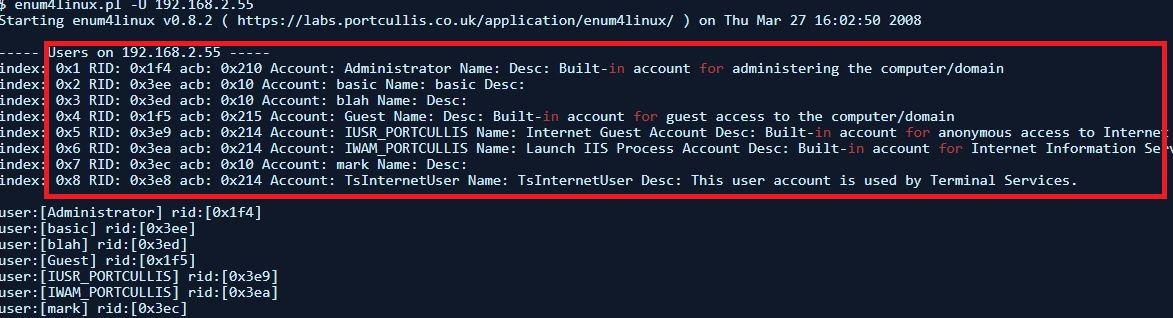
DO EVERYTHING OPTION:-
- For obtaining the list of usernames, on Windows 2000 the RestrictAnonymous registry settings must be 0 for this query to work.
- For changing windows registry value go to location HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA
And edit RestrictAnonymous = 0
- Type enum4linux -u 192.168.2.55 as shown below:
- It fetches the complete list of usernames it this server allows.
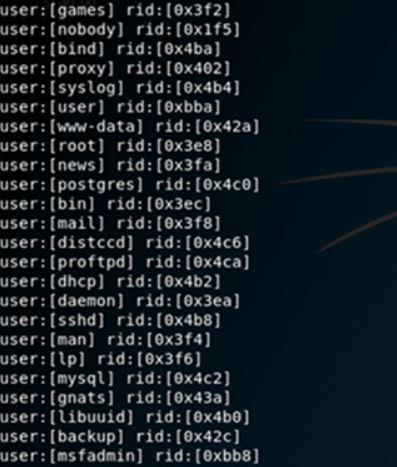
REMOTE SYSTEM USERS:-
- Testing through different IP:
==========OUTPUT SNIP=============
- As shown above enumerating users list via RID cycling. RID cycling attack that try to enumerate the users account through null sessions. RID extracts users from windows hosts (or samba hosts). The users list can be used in other hacking activities.
NOTE: what is Relative Identifier (RID) ?
C:\Users\iics>wmic useraccount get name,sid Name SID abc S-1-5-21-2657294712-1178242540-1465888351-1676 C:\Users\iics> 1676 is RID
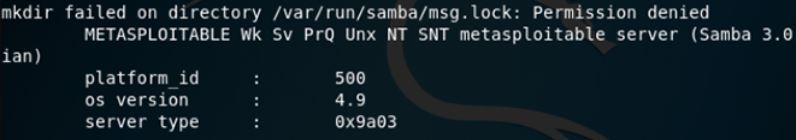
GETTING THE OS INFO:
- Type enum4linux -o 192.168.0.6
=============OUTPUT SNIP=============
- After executing OS info query you can get the OS Information which further can be in other brute force attacks.
According to past researches done by ethical hacking researcher of International Institute of Cyber Security enum4linux can be used in knowing the users list after which that list can be used in other penetration activities.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.