TOR EXIT RELAY SCANNER:- As we all know tor is used for anonymous communication in anonymity network. Exitmap modules implement tasks that are run over of subset of all exit relays. It’s fast and modular python-based scanner for tor exit relays. Exitmap is useful to monitor the accuracy of all exit relays. As per ethical hacking researcher of International Institute of Cyber Security if you have a programming experience than this modules can perform TCP-based networking task, fetching a web page, uploading a file, connecting to an SSH server, or joining an IRC channel.
This tool is used by many ethical hackers.
First install TOR browser in kali linux and type apt-get install tor in linux terminal.
If the tor is already configured, then skip the above step and download exitmap.
- Type git clone https://github.com/NullHypothesis/exitmap.git for downloading exitmap.
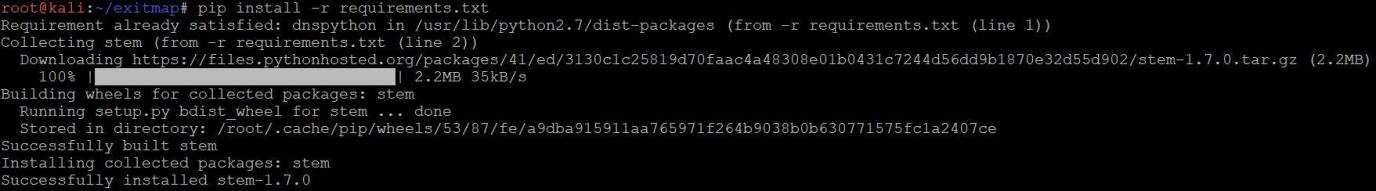
- As we were in /root directory, exitmap is cloned/downloaded in the same directory. After download, navigate to /root/exitmap/bin and type
pip install -r requirements.txt as shown below:
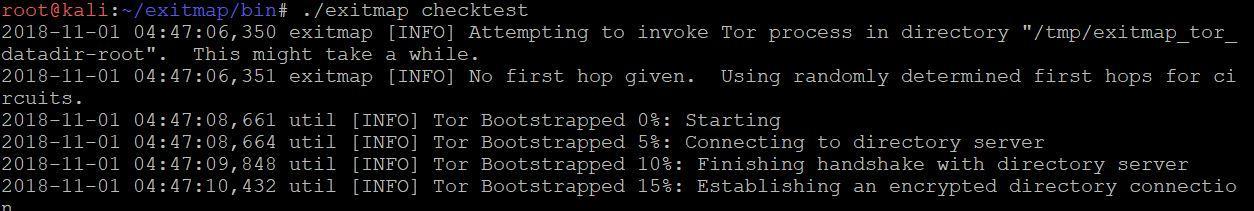
- After installing requirements.txt in above step type ./exitmap checktest command in exitmap bin folder.
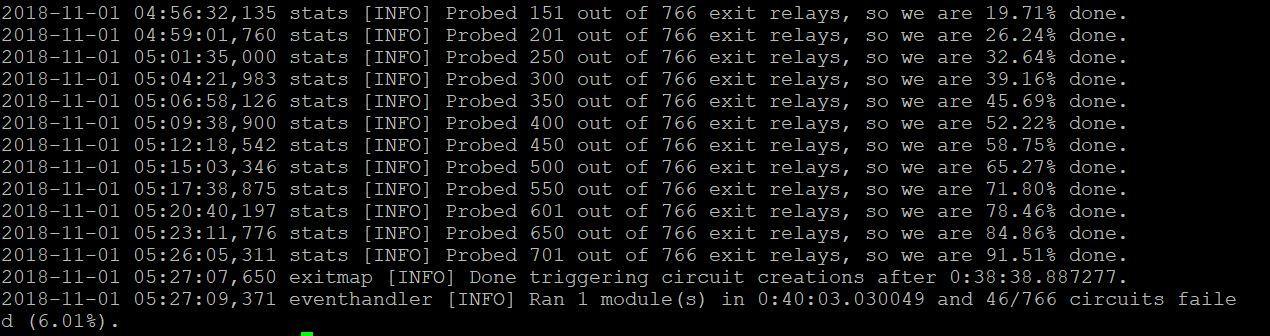
====== OUTPUT SNIP ========
- Output show how TOR bootstraps and the output of the checktest module, and the scan summary.
TEST USING THE FINGERPRINT:-
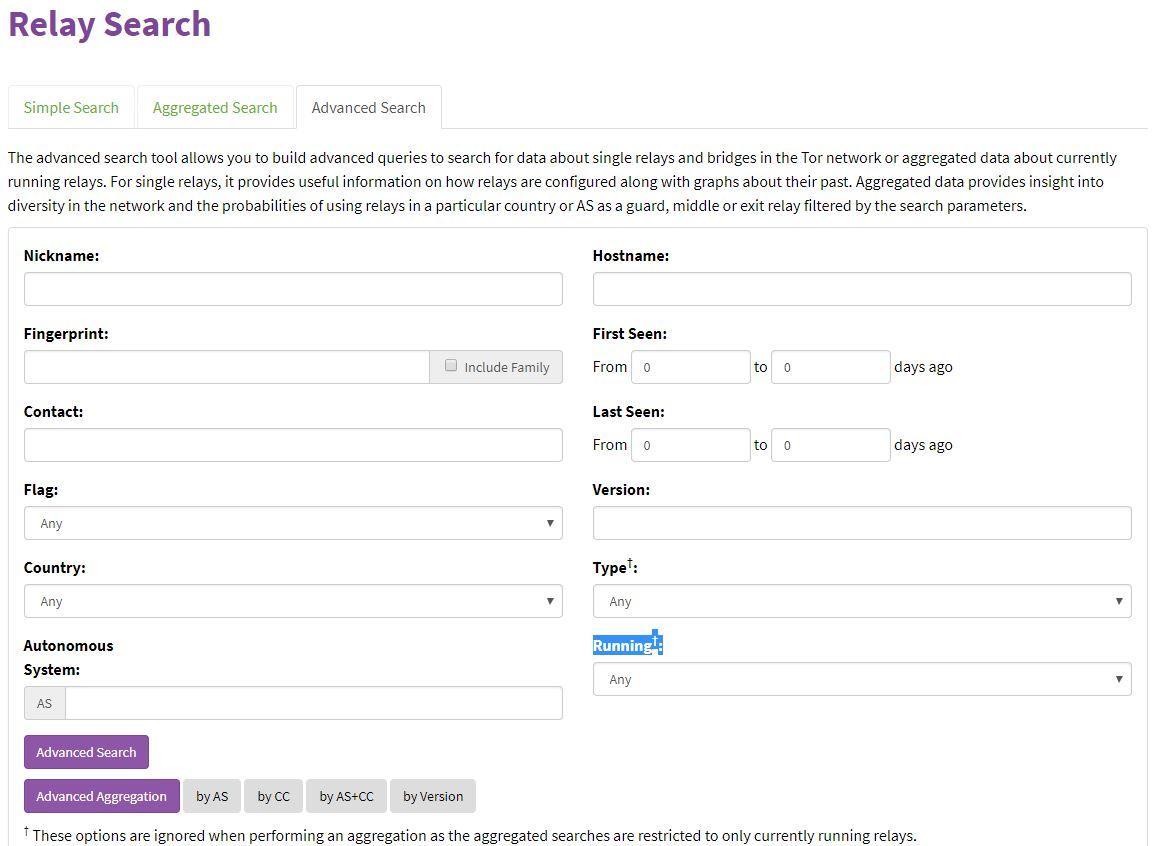
- For Getting the Tor node fingerprint go to : https://metrics.torproject.org/rs.html#advanced.
- Suppose we select a country from drop down menu, .i.e. DE for Germany country
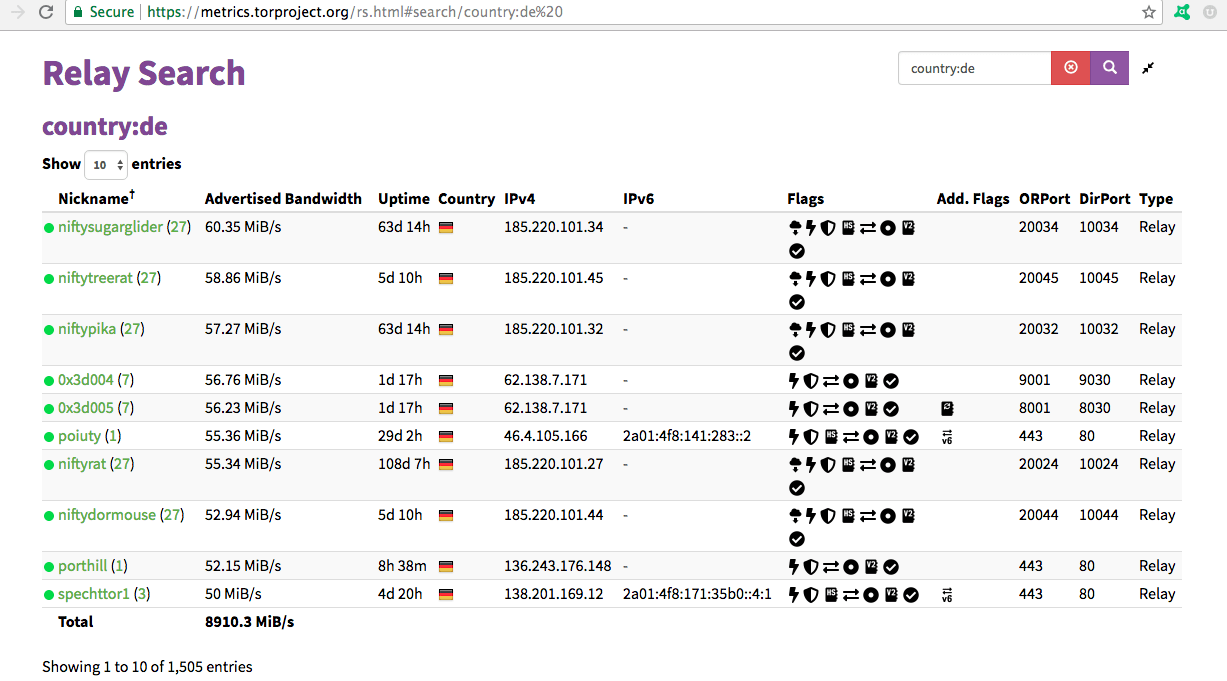
- Then click on search it will list tor node for Germany.
- After the above search the fingerprint will be generated as shown below:
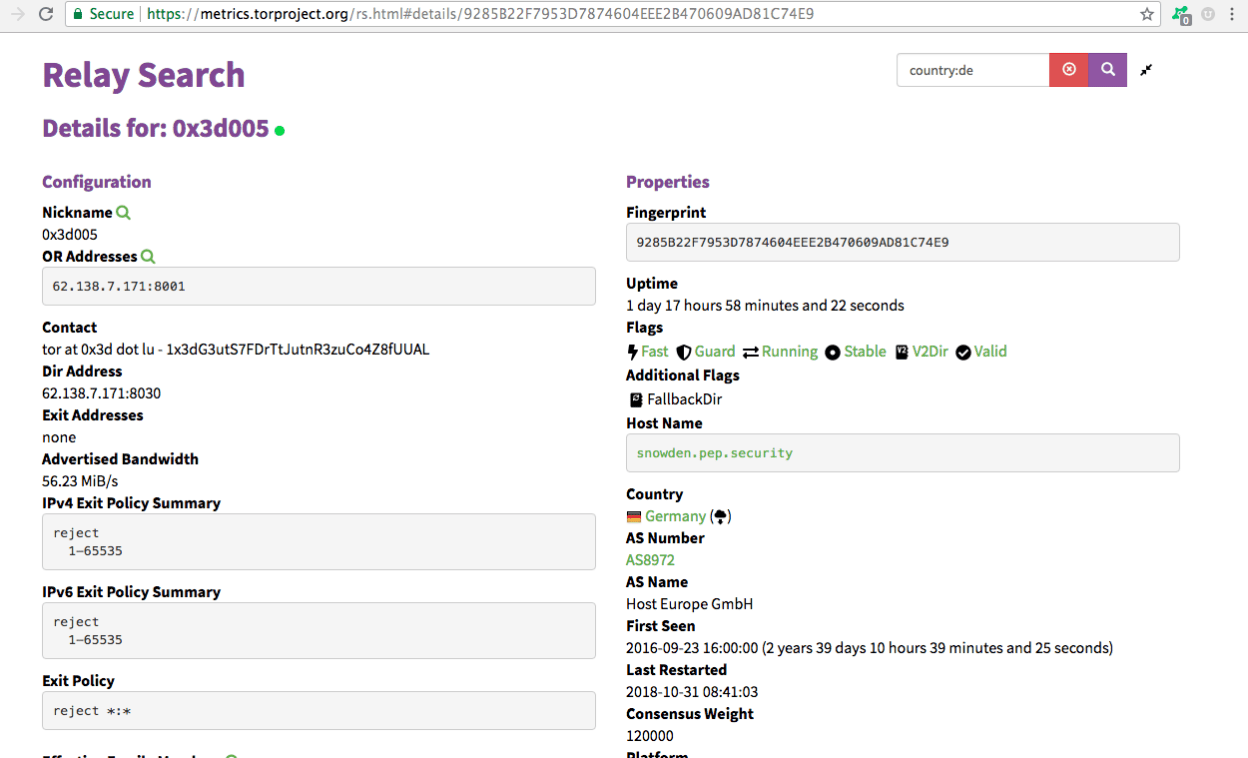
- Select and click any one Node, suppose we selected:
0x3d005 (7) 56.23 MiB/s 1d 18h Germany 62.138.7.171, we get as sown below:
- In the above screenshot you can see Tor node Fingerprint.
Using Desired Fingerprint:-
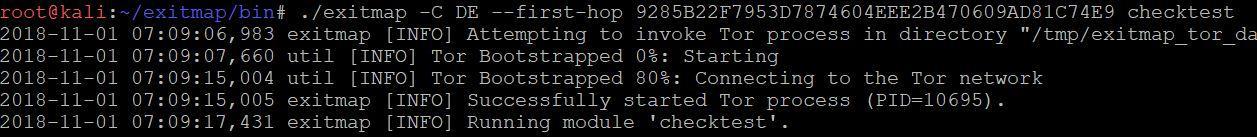
Type:
./exitmap -C DE –first-hop 9285B22F7953D7874604EEE2B470609AD81C74E9 checktest
as shown below.
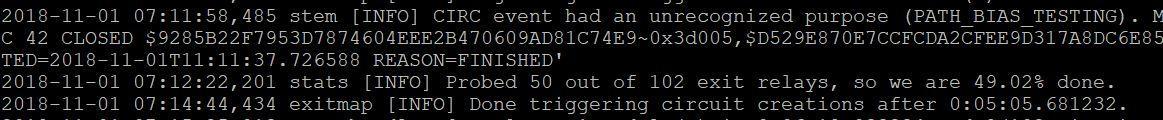
==========OUTPUT SNIP==========
- Output show how TOR bootstraps and the output of the checktest module, and a the scan summary from German exit relays only, mention ethical hacking investigators.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.