DATASPLOIT:- Datasploit is a tool used in footprinting a target or defending target. It allows you to collect relevant information about the domain, email, phone number, person, etc, as per ethical hacking courses. It collects the information about a target which can expand your attack, defense. This tool is used in kali linux penetration testing. As per past researches done by ethical hacking researcher of International Institute of Cyber Security this tool quite come handy which gathering the information of the target.
For installing Datasploit:
- Type git clone https://github.com/datasploit/datasploit
- Then type cd /root/Downloads/Datasploit.
- Then type pip install -r requirements.txt
- Type mv datasploit_config.py config.py
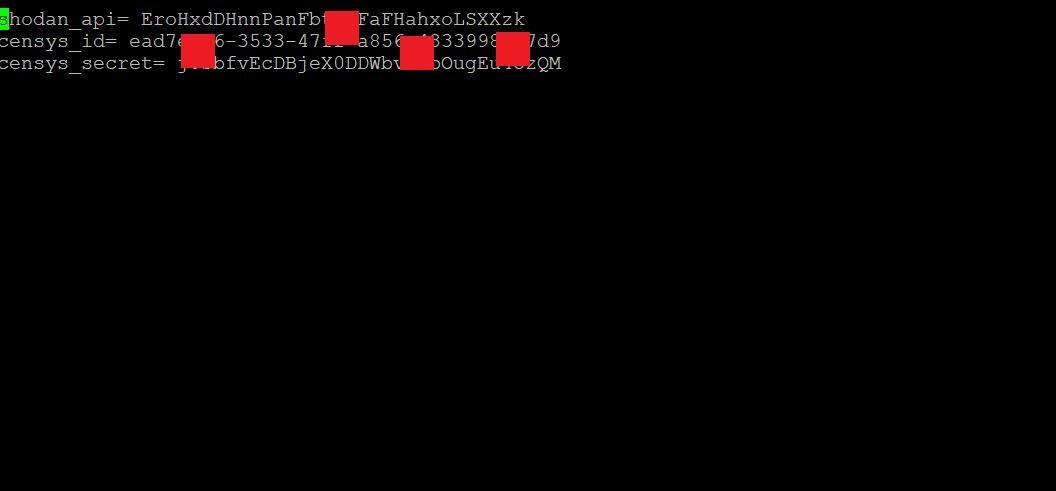
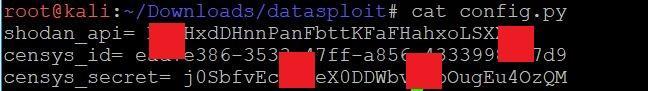
- In the config.py you have to enter API key/secrets for different components in datasploit.
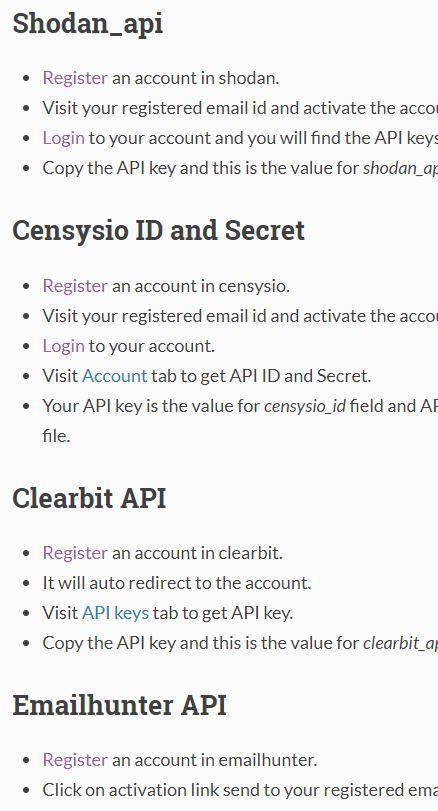
- For generating the API keys go to https://datasploit.readthedocs.io/en/latest/apiGeneration/
- For generating the API key you have to create account in each of the website like – shodan API, censyso API etc and follow the instruction as needed.
NOTE; the more you get API’s, more information can be enumerated.
- After generating API go to config.py and save generated API in config.py
- cd /root/Downloads/Datasploit
- vim config.py
- Save API in config.py as shown below:
- The above API keys will be used while executing the queries.
- Type ./datasploit.py
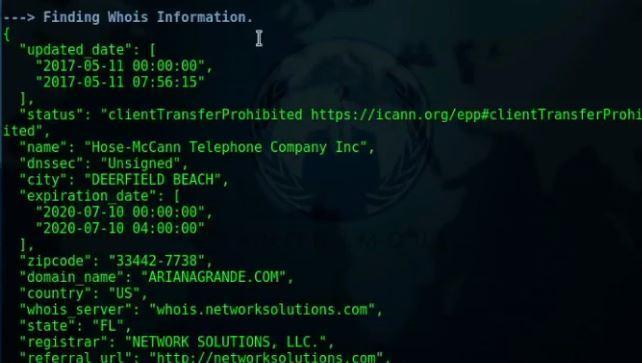
- Type python domainOsist.py arinagrande.com as shown below:
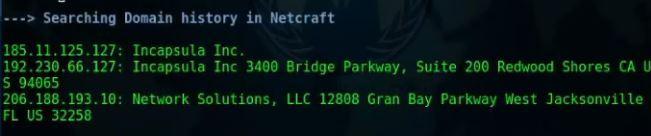
===========OUTPUT SNIP============
========OUTPUT SNIP===========
=========OUTPUT SNIP==========
- After executing the above query information like- domain history, whois information fetched from the target which can be used in further hacking activities.
- The target contain information like domain history, whois information, finding hosts. All these information can be used in information gathering.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.