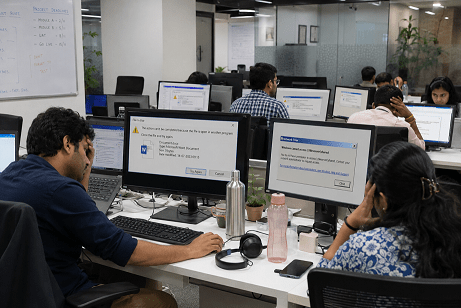
Get ADMIN access on Windows by exploiting the old FAX service – Step by step
Now you can get ADMIN access on Windows by exploiting old Windows Fax Service to gain full SYSTEM level access on a machine. By combining a UAC bypass technique withRead More →