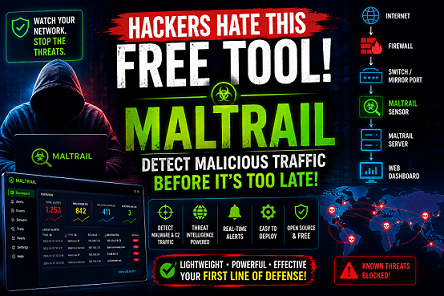
The Easiest Way to Detect Malware Traffic Without a SIEM
Organizations spend a lot of money on firewalls, antivirus software, EDR solutions, and SIEM platforms. However, attackers still find ways to communicate with compromised systems inside a network. What ifRead More →