Six weeks after hackers revealed vulnerabilities in a 2014 Jeep Cherokee that they could use to take over its transmission and brakes, Chrysler has pushed out its patch for that epic exploit. Now it’s getting another round of criticism for what some are calling a sloppy method of distributing that patch: On more than a million USB drives mailed to drivers via the US Postal Service.
Security pros have long warned computer users not to plug in USB sticks sent to them in the mail—just as they shouldn’t plug in thumb drives given to them by strangers or found in their company’s parking lot—for fear that they could be part of a mass malware mailing campaign. Now Chrysler is asking consumers to do exactly that, potentially paving the way for a future attacker to spoof the USB mailers and trick users into installing malware on their cars or trucks.
“An auto manufacturer is basically conditioning customers into plugging things into their vehicles,” says Mark Trumpbour, an organizer of the New York hacker conference Summercon whose sister-in-law’s husband received the USB patch in the mail Thursday. “This could have the potential to backfire at some point in the future.”
When WIRED reached out to Chrysler, a spokesperson responded that the USB drives are “read-only”—a fact that certainly wouldn’t protect users from a future spoofed USB mailing—and that the scenario of a mailed USB attack is only “speculation.”
“Consumer safety and security is our highest priority,” the spokesperson added. “We are committed to improving from this experience and working with the industry and with suppliers to develop best practices to address these risks.”
Chrysler, to be fair, did not have very much choice in its USB response. Within days of WIRED’s July story revealing the Jeep hack by security researchers Charlie Miller and Chris Valasek, the company came under pressure from the National Highway Transportation Safety Administration to perform a full recall for the 1.4 million vehicles with a vulnerable Uconnect dashboard computer. Though the company had released a security update for download on its website, it had no ability to push out an “over-the-air” patch via the Internet. A USB mailing was likely its best option to reach as many Chrysler owners as possible. And to the company’s credit, it also implemented a layer of protection on the Uconnects’ Sprint network designed to block Miller and Valasek’s wireless attack.
Summercon organizer Trumpbour says he’s not entirely sure whether the mailed USB patch was a security gaff. It effectively reaches the wide collection of vulnerable drivers, and anyone impersonating the mailing to effectively spread malware would have to know targets’ make and model of vehicle.
Even so, he says the safest bet would have been to tell Chrysler owners to simply bring their vehicles into a dealership to have their software updated. “The USB route is the cheap way to do it,” Trumpbour says. “But the dealership route probably would have been better, because you wouldn’t have this attack vector.”
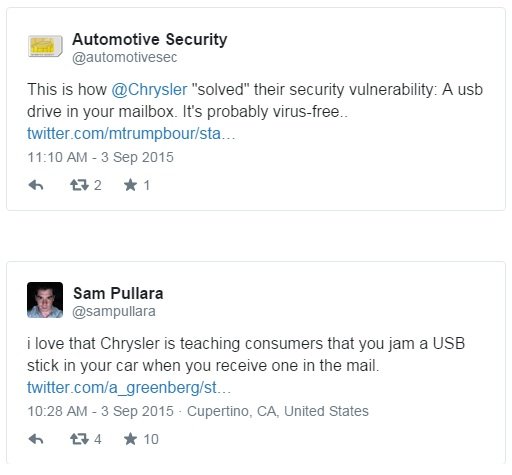
In the meantime, here are few of the IT and security Twitter comments criticizing Chrysler’s USB mailing:
Source:https://www.wired.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.