During the course of our daily malware hunt, we came across a new mobile ransomware variant that leverages pornography to lure victims into downloading and installing it. We’d previously blogged about similar Android malware.
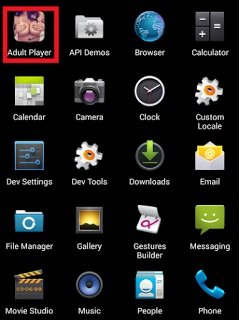
App Name: Adult Player
URL: hxxp://accanalasti247[.]topliberatone[.]pw/video_player.php?s=Zomhj9PlVZc=&name=Mp4TubePlayer_v5.562.apk&type=1&tpl=1&l=EN
MD5: 6ed2451d1300ff75e793744bb3563638
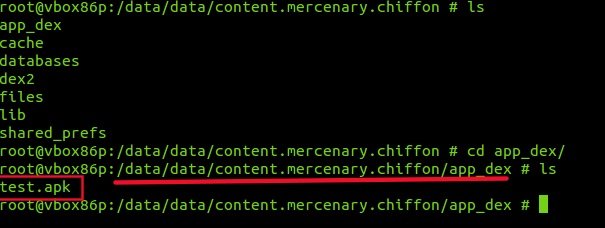
Package Name: content.mercenary.chiffon
Overview:
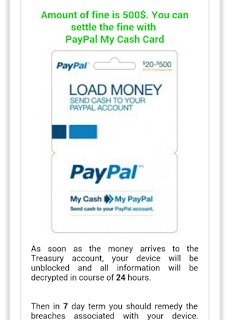
This ransomware acts as a porn app named “Adult Player” and lures victims who assume it is a pornographic video player. When the victim starts using it, the app silently takes a photo of the victim, which is then displayed on the ransomware screen, along with the ransom message. The app demands a ransom of 500 USD.
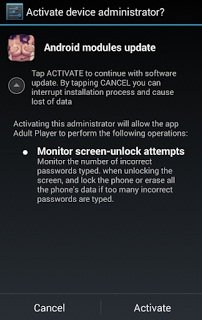
Admin Activation:
Upon opening the app, it asks for admin rights as shown below :
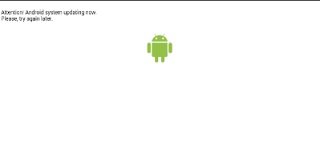
After clicking “Activate”, the app shows a fake update page but nothing really happens in terms of an update.
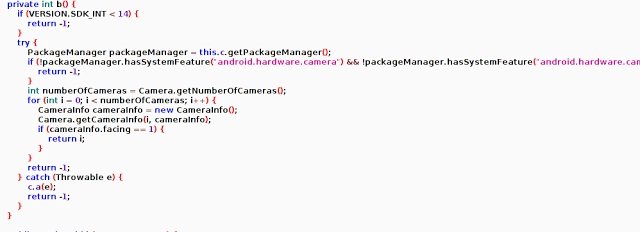
The ransomware checks whether front camera is available or not. If available, it clicks photo of the victim while he/she is using the app and displays the image on ransom page.
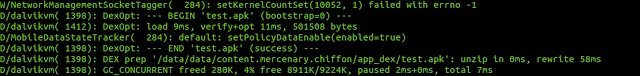
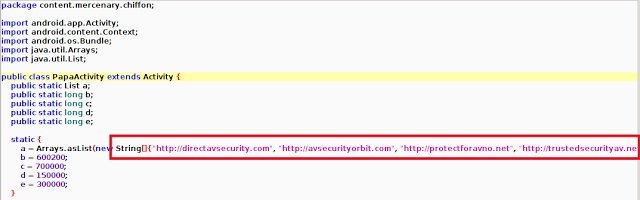
The majority of the malicious activities are then conducted by the newly loaded test.apk. The malware connects to the following hard-coded domains contained in the app:
- hxxp://directavsecurity[.]com
- hxxp://avsecurityorbit[.]com
- hxxp://protectforavno[.]net
- hxxp://trustedsecurityav[.]net
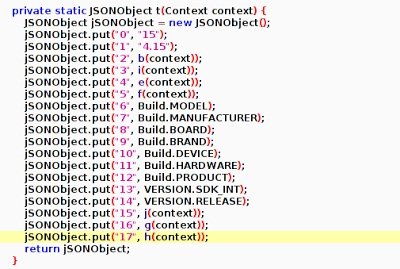
The malware then sends following details that includes victim’s mobile device and operating system information to the remote server:
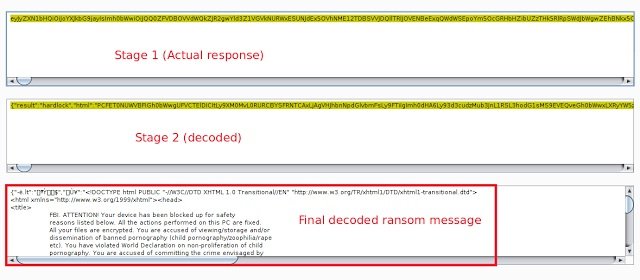
Ultimately, the malware receives a custom ransom page upon run time in a multi-encoded response from the aforementioned servers.
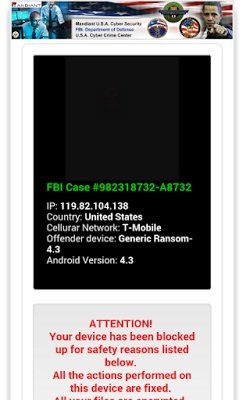
Once the response is received, the ransomware locks the phone and displays the following ransom screen.
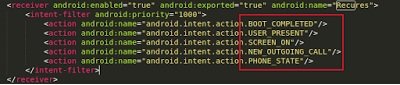
The ransom screen is designed to stay persistent even at reboot. It does not allow the user to operate the device and keeps the screen active with ransom message.
More variants:
We also encountered additional apps belonging to this ransomware family and exhibiting similar functionality.
Sample MD5s:
- ecd8c9eeae86c0d7d3c433e887fd5d3a
- b544785176ed8152671bac94a18ca9d0
- 9c731690985ce7c13ca9b25b9139d6a3
Mitigation:
The ransomware is designed to stay stagnant on screen and does not allow the the victim to uninstall it. Rebooting the device does not work in such cases as ransomware app becomes active immediately after reboot, which leaves no scope for the victim to get into device “settings” and uninstall the ransomware.
In such scenarios, it can be removed by using the following steps:
- Boot device into safe mode (Please note that entering “safe mode” varies depending on your device). Safe mode boots the device with default settings without running third party apps.
- Uninstalling ransomware from device requires you to first remove administrator privilege. To do the same, go to Settings –> Security –> Device Administrator and select ransomware app, then deactivate.
- Once this is done, you can go to Settings –> Apps –> Uninstall ransomware app.
Prevention:
To avoid being victim of such ransomware, it is always best to download apps only from trusted app stores, such as Google Play. This can be enforced by unchecking the option of “Unknown Sources” under the “Security” settings of your device.
Source:https://research.zscaler.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.