Sounds like it’s going to be a busy few days for R&D and PR departments at least two security companies.
This weekend, vulnerability researchers have separately disclosed flaws in products from Kaspersky and FireEye that could be exploited by malicious hackers.
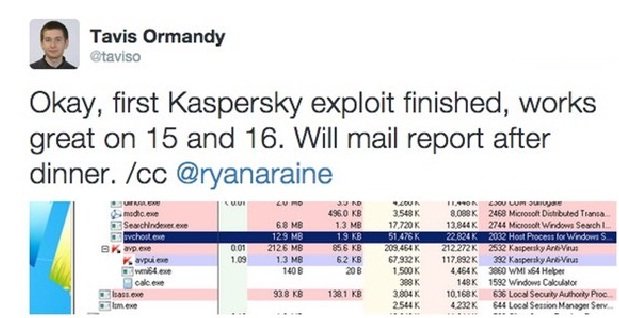
First up was Tavis Ormandy.
Ormandy, a security researcher at Google, has made a controversial name for himself over the years disclosing security vulnerabilities in products from other software vendors.
His critics, of which I’m one, fear that he has sometimes put innocent users at risk by not working on a co-ordinated disclosure with the manufacturer of the vulnerable software, ensuring that all users are protected with a patch before details of how to exploit the flaw are made public.
At the end of last week, Ormandy tweeted that he had successfully exploited Kaspersky’s anti-virus product in such a way that users could find their systems easily compromised by malicious hackers.
Ormandy has previously published details of how he has exploited anti-virus products from Sophos and ESET.
In a follow-up to his latest announcement, Ormandy tweeted that the flaw was “a remote, zero interaction SYSTEM exploit, in default config. So, about as bad as it gets.”
One has to question the timing of Ormandy’s announcement just before a long holiday weekend in the United States, which clearly makes it difficult as possible for a corporation to put together a response for concerned users. I supposed we should be grateful that he at least ensured that Ryan Naraine, a reporter at Kaspersky’s Threatpost blog, was cc’d on the announcement.
None of this, of course, is to say that the vulnerability doesn’t sound serious, and Kaspersky would be wise to investigate and fix it at the earliest opportunity. Ideally vulnerabilities should be found by a company’s internal team, or ironed out before software ever gets released. And it’s better that someone like Ormandy finds a flaw rather than a malicious hacking gang.
Nonetheless, one remains concerned that in the past malicious hackers have taken details of flaws published by Google’s Tavis Ormandy, and used them in attacks.
Meanwhile, another security researcher had an important announcement this US holiday weekend, revealing that he had found flaws in FireEye’s software.
As CSO reports, Kristian Erik Hermansen has disclosed details of a zero-day vulnerability, which – if exploited – can result in unauthorised file disclosure.
Regrettably, Hermansen published proof-of-concept code showing how the vulnerability could be triggered, and claimed that he had found three other vulnerabilities in FireEye’s product. All are said to be up for sale.
“FireEye appliance, unauthorized remote root file system access. Oh cool, web server runs as root! Now that’s excellent security from a _security_ vendor 🙂 Why would you trust these people to have this device on your network.”
“Just one of many handfuls of FireEye / Mandiant 0day. Been sitting on this for more than 18 months with no fix from those security “experts” at FireEye. Pretty sure Mandiant staff coded this and other bugs into the products. Even more sad, FireEye has no external security researcher reporting process.”
If you use products from Kaspersky or FireEye you may wish to contact their technical support departments to see if they can shed any more light on these issues. Be sure to be nice to them. Chances are they didn’t have a great holiday weekend.
Update:
According to Ormandy, Kaspersky is rolling out a fix globally. That sounds like a great response from the Russian anti-virus firm.
Source:https://grahamcluley.com

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.