AT&T has filed a lawsuit against 3 former call center employees, accusing them of installing malware on their servers with the purpose of aiding a phone unlocking service in obtaining AT&T unlock codes.
Almost all mobile carriers around the globe sell phones together with their mobile plans. These phones are usually locked, so customers won’t be able to jump ship to another carrier without fully paying for the phone or by finishing their contract.
In the US, forced by the FCC, AT&T has to provide unlock codes for all users who have finished out their contract or have paid a fee to leave the service.
This code is usually obtained from AT&T call centers using a special service called Torch.
AT&T sabotaged by its own employees
According to legal documents filed in a District Court in Seattle, AT&T has accused Kyra Evans, Nguyen Lam and Marc Sapatin, 3 former call center employees, of purposely installing malware on the company’s computers, which granted a Californian company access to their Torch system.
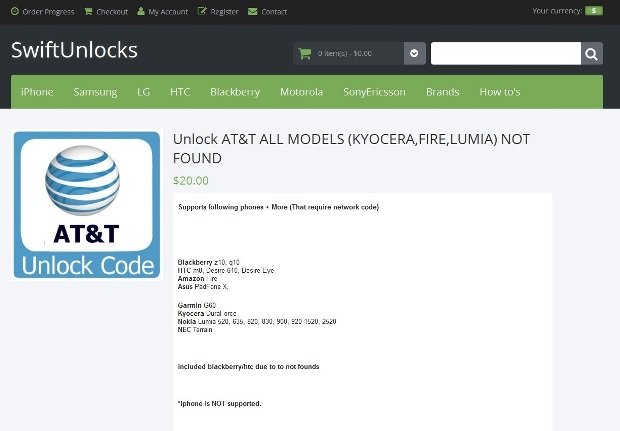
The company in question is Swift Unlocks, a Web portal that provides phone unlocking services.
According to court documents, the three former employees were being paid $1,000 / €900 per week to run the malware on their computer.
AT&T claims it lost hundreds of thousands of unlock codes, and eventually, the high number of generated unlock codes alerted Torch’s admins.
Other mobile carriers may be affected as well
As GeekWire reports, Sapatin, one of the three employees involved in the scheme, also tried to recruit a fourth, bragging that this scheme included many people across the country, and among them other carriers outside AT&T.
Checking Swift Unlocks’ website, we can see that similar services are also offered for T-Mobile and Verizon. The same website is offering to unlock any AT&T phone model for $20 / €18.
Source:https://news.softpedia.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.