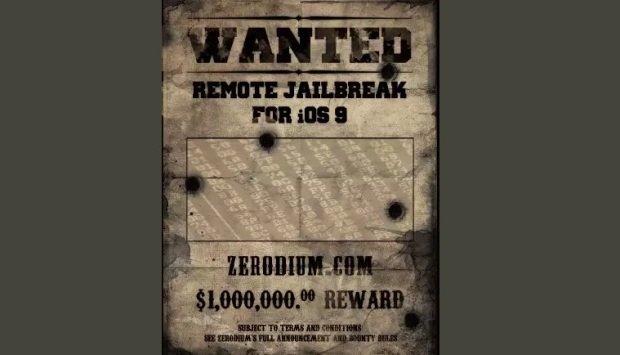
Here’s a treat for hackers and security researchers who don’t mind selling information about zero-day vulnerabilities to the highest bidder: Zerodium, the zero-day vulnerability and exploit acquisition firm recently launched by VUPEN founder Chaouki Bekrar, is offering a million dollars for “an exclusive, browser-based, and untethered jailbreak for the latest Apple iOS 9 operating system and devices.”
All the security improvements and exploit mitigations that Apple implemented in iOS made the popular mobile operating system secure, but not unbreakable, the company has noted. It means that much more effort and time (and therefore money) will be required to come up with a working exploit.
The company is offering a million dollars for a “full chain of unknown, unpublished, and unreported vulnerabilities/exploits (aka zero-days) which are combined to bypass all iOS 9 exploit mitigations including: ASLR, sandboxes, rootless, code signing, and bootchain.”
“The exploit/jailbreak must lead to and allow a remote, privileged, and persistent installation of an arbitrary app (e.g. Cydia) on a fully updated iOS 9 device,” they pointed out. “The whole exploitation/jailbreak process should be achievable remotely, reliably, silently, and without requiring any user interaction except visiting a web page or reading a SMS/MMS.”
The total bounty pool is $3 million, and the program is open only until October 31st, 2015. It may be closed earlier, if the company shells out the $3 million before that date.
Incomplete exploits, exploits requiring more user interaction, physical access to the device, or can be mounted over Bluetooth, NFC, or baseband, will not be eligible for those prizes. Still, the company might offer to buy them for a lesser amount.
The company generally focuses on acquiring high-risk vulnerabilities with reliable exploits affecting modern operating systems, software, and devices.
Source:https://www.net-security.org/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.