Yesterday’s update of the encryption software VeraCyrpt fixed two vulnerabilities that security researcher James Forshaw discovered in TrueCrypt’s source code.
TrueCrypt, which has been abandoned by its developers, is still widely used. This can be attributed largely to convenience and that the software’s security audit did not turn up major critical vulnerabilities in the program.
The audit did find some issues which the VeraCrypt developers fixed (mostly) in previous updates.
VeraCrypt, which is based on TrueCrypt code but still under active development, is one of several alternatives for TrueCrypt users who are looking for alternatives for the abandoned program.
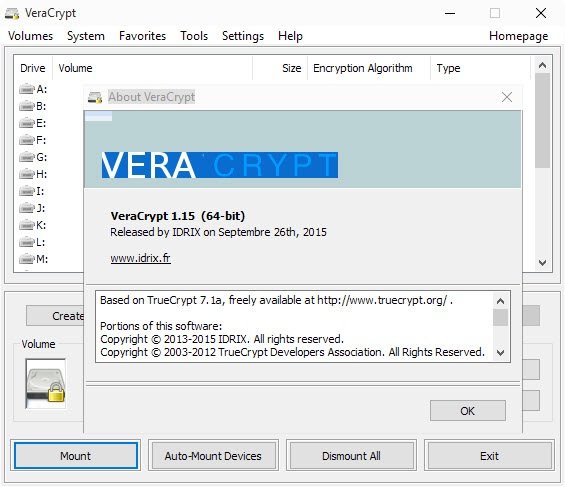
The two vulnerabilities fixed in VeraCrypt 1.15 are:
- CVE-2015-7358 (critical): Local Elevation of Privilege on Windows by abusing drive letter handling.
- CVE-2015-7359: Local Elevation of Privilege on Windows caused by incorrect Impersonation Token Handling.
Both appear to be local attacks meaning that attackers need to gain local access to the PC to exploit them. While that is the case, it is certain that TrueCrypt won’t be updated to fix these issues in the software which in turn means that TrueCrypt remains vulnerable to attacks exploiting them.
This in turn means that TrueCrypt users need to decide whether it is time to move to another encryption software or keep using the vulnerable TrueCrypt.
VeraCrypt is one candidate for making the switch, especially since it can convert TrueCrypt containers and non-system partitions to the format it supports. The software can mount TrueCrypt volumes furthermore so that it is possible to switch to it without making any changes to the system provided that the system partition has not been encrypted using TrueCrypt.
The easiest way to deal with it is to decrypt it using TrueCrypt before you encrypt it again from within VeraCrypt.
Other feature additions in VeraCrypt 1.15 and 1.14 include support for a volume expander in the Traveler Disk Setup, a regression fix in mounting of favorite volumes at user login, and options to verify a created rescue disk ISO image file.
It seems to be time to abandon TrueCrypt for good as it is likely that additional vulnerabilities will be found in the software in the future.
Source:https://www.ghacks.net/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.