The malware spreads with the help of an adult movie player. Security researchers at Palo Alto Networks have discovered and analyzed malware that infects iOS devices and then injects ads into other apps and when browsing the Web. Researchers say this is the first instance of iOS malware targeting and succeeding in infecting non-jailbroken devices.
YiSpecter, as the malware was named, is being spread mainly to Chinese users via four different methods.
A wide spectrum of infection methods
The malware can infect users with the help of the Lingdun worm. This worm can target a wide range of device types and works via the QQ social network and its file sharing interface. The worm uploads malicious HTML files with pornographic names and shares them with other users in the network. When a user accesses these files, the page detects that the user is utilizing an iOS device to access these pages and serve a version of the YiSpectre adware.
A second method of infection is by way of Internet traffic and DNS hijacking. This happens when local ISPs have their servers infected by attackers, which then use it to show popups for an iOS app that comes packed with YiSpectre. Downloading the app and installing it results in a successful infection. These popups only appeared when browsing the Web from a home WiFi network. Using a proxied browser did not show the popups. The only way to make the popup disappear is to make a complaint to the ISP.
The third method of infection is by offline app installation. As with the first method, attackers created a malicious app, which they promoted as the QVOD Player version 5. QVOD is a discontinued mobile video player for adult content, which was shut down by Chinese authorities. This infection method relies on users downloading the app from iOS app portals and installing it manually. Additionally, Palo Alto also claims that some phone retailers and maintenance suppliers will also install malicious malware for cash.
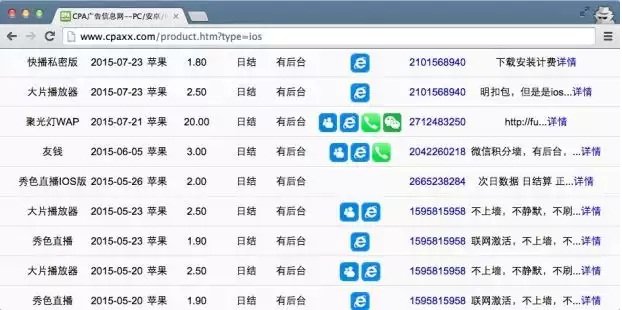
The last method of infection observed by researchers is by way of public promotion of the app (modified QVOD Player), usually done on underground and mobile forums. This method usually redirects users to unauthorized iOS app portals (third method) and is used to bring in more users that might not have been usually exposed to the app in the first place.
YiSpectre uses signed components to infect iOS devices
YiSpectre can affect both jailbroken and non-jailbroken devices with the help of four components, all signed with enterprise certificates. These components allow the malware to bypass various Apple’s built-in security protocols, by abusing private APIs, downloading each other, and passing as one or another legitimate component at various stages of the infection.
When the infection stage is complete, the malware will then remove three of the four icons added by these components, and hide the last icon as one of Apple’s system apps.
Once on the user’s phone, WiSpectre starts downloading, installing, and launching other arbitrary iOS apps, replacing legitimate apps, and even hijacking existing apps, showing ad interstitials every time they are started.
The malware can also change Safari’s default search engine, alter its bookmarks, modify currently opened pages, and report on the user’s activity and phone details to a C&C server.
Who developed YiSpectre?
According to Palo Alto researchers, the malware was first seen starting with November 2014, and is currently detected by one of VirusTotal’s AV engines, Chinese antivirus company Qihoo, which also reported on it back in February 2015.
The same Palo Alto researchers also point out that three of the four components used by YiSpectre to infect devices are signed by certificates issued to YingMob Interactive, a Chinese mobile advertising platform.
Some of the IP addresses used by the malware also point out to a few YingMob servers.
Additionally, the company also developed an app called HaoYi Apple Helper, which coincidentally or not, is the name of the user that’s been posting promotional messages for the infected QVOD Player on underground forums (see fourth method of infection).
This app was later renamed Fengniao Helper, and claims to help users install paid iOS apps from the Apple Store for free. Palo Alto says its functionality is similar to the iOS Trojan KeyRaider, a malware that steals Apple account credentials and then uses them to steal paid apps from the official store and install them on jailbroken devices for free.
Palo Alto has informed Apple of the threat and Apple will start revoking the certificates used to install YiSpectre’s four components. Palo Alto also has a four-step process on how to remove the malware from infected phones.

Source:https://news.softpedia.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











