Authorities in several European countries announced they have coordinated an operation to arrest criminals using the popular DroidJack RAT.
Android RATs are becoming very popular in the criminal underground, a recent research conducted by Recorded Future demonstrated that interest in the DroidJack and AndroRAT, especially in the Middle East and Africa.
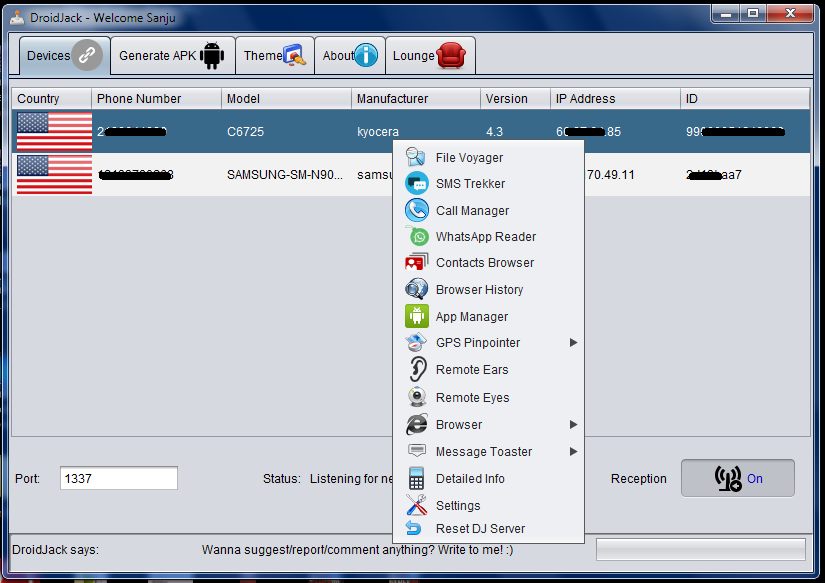
Mobile spyware is widely adopted also in Europe by cyber criminals, applications like DroidJack, allows them to intercept/send SMS messages, call logs, browser history, contacts, and sensitive data including the user credentials.
German Prosecutors have started a campaign to dismantle the organizations relying on the popular DroidJack Android spyware. The European Law enforcement of various countries has coordinated their efforts to dismantle the criminal crews behind DroidJack campaigns.
Police conducted several raids in Europe coordinated by Europol and Eurojust, operations were conducted in Britain, France, Belgium and Switzerland.
“On 27 October 2015, in an investigation initiated by Germany and supported by Europol and Eurojust, law enforcement officials from Germany, France, Britain, Belgium, Switzerland and the United States have carried out a number of house searches and arrests of suspected users of the mobile phone malware DroidJack, which allows cybercriminals to take over control of Android smartphones without their owners noticing.” states the official announcement issued by the Europol.
The European Police targeted individuals who had bought DroidJack and used the Android RAT in 2014 and 2015.
A spokesman for the Frankfurt prosecutor’s office confirmed to the AFP that arrested individuals had no links among them. A spokeswoman for Switzerland’s federal police confirmed that one search was carried out in the country, but none has been arrested since now.
French authorities arrested four people on suspicion of buying the DroidJack Android RAT, the police informed media that the same men have been already released by the police.
Source: securityaffairs.co/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











