Denis Andzakovic, a security researcher for Security Assessment, has created a tool that can fool the KeePass password manager into exporting its internal passwords database as a CSV file, showing user account credentials in cleartext.
The tool, which he ironically named KeeFarce, is available on GitHub, and despite its powerful attributes, it only works if the user has an instance of KeePass 2.x opened on their computer when KeeFarce is executed.
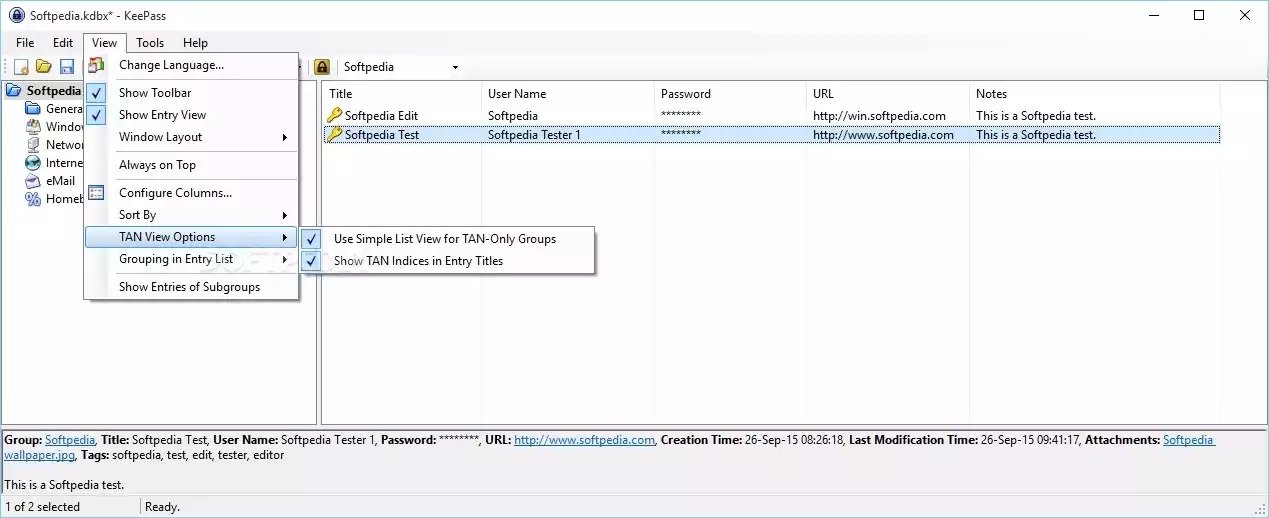
KeePass is a password manager that allows users to record account details for various websites and applications, and then automatically fills in these details when users open or access those applications/websites at later points.
KeePass and other applications of the sort allow users to improve their online password policies by setting complex passphrases for their accounts.
Tools like KeePass have become indispensable for many users, who utilize them on a daily basis so they won’t be forced to write passwords down on paper, keep them inside text files on Dropbox, or memorize complex and random character strings.
KeeFarce uses DLL injection to steal the KeePass database
Under the hood, KeeFarce works by leveraging a technique called DLL injection, which allows third-party applications to intervene in the processes of another app, by forcing it to load an external DLL file.
The technique is quite old but also requires administrative rights on the computer where it is used.
That’s why KeeFarce, despite its powerful capabilities, is quite useless unless the computer has already been compromised and attackers gained admin privileges. In case this ever happens, users will have bigger things to worry about, since most of their data was probably logged already, and KeeFarce only becomes just a small cog in a bigger machine.
As Andzakovic told ArsTechnica in an interview, his tool is compatible with the Metasploit hacking framework, meaning that crooks will probably have an instance of it running by the end of the week.
To KeePass’ defense, its authors never said their application was 100% full-proof. The company has numerous times in the past said that their tool can be compromised in large scale attacks on the system in runs on, and they can only protect users from basic tools like keyloggers, not fully equipped hacking frameworks like Metasploit.
“All security features in KeePass protect against generic threats,” says the KeyPass Security page. “The best security features will fail. This is law #1 of the 10 Immutable Laws of Security: ‘If a bad guy can persuade you to run his program on your computer, it’s not your computer anymore’.”
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.