Malware operators are taking aim at Web developers. A newly discovered ransomware is attacking Linux Web servers, taking aim at Web development environments used to host websites or code repositories.
Russian antivirus maker Dr.Web came across this malware and said that the ransomware needs root privileges to work. Additionally, the company also says it does not yet know how the ransomware infects computers, but taking into account previous Linux-based malware infections, the main culprit may be an open SSH port with weak credentials (not confirmed).
The ransomware uses AES encryption to lock down files
As for its modus operandi, when the ransomware launches, it starts to download the ransom message, and then a file containing the public RSA key. The latter key is then used to store AES keys used to encrypt the local files.
When this happens, the ransomware adds the .encrypt extension to each file and places a ransom text message in each folder where it encrypts data.
The ransomware has a taste for Web pages and their associated file extension
The malware specifically targets files in folders that are generally found in Linux Web server setups, or in coding and development environments.
This includes directories like /home, /root, /var/lib/mysql, /var/www, /etc/nginx, /etc/apache2, /var/log, and any directory that includes terms like git, svn, webapp, www, public_html, or backup.
The ransomware also looks for files that have extensions specific to Web development environments like .js, .css, .properties, .xml, .ruby, .php, .html, .gz, .asp, and such. Other file extensions known to host data are also covered (.rar, .7z, .xls, .pdf, .doc, .avi, .mov, .png, .jpg, etc.).
Dr.Web detects the ransomware as Linux.Encoder.1. After careful analysis, the company said that Linux.Encoder.1 is coded in C and also uses the PolarSSL library.
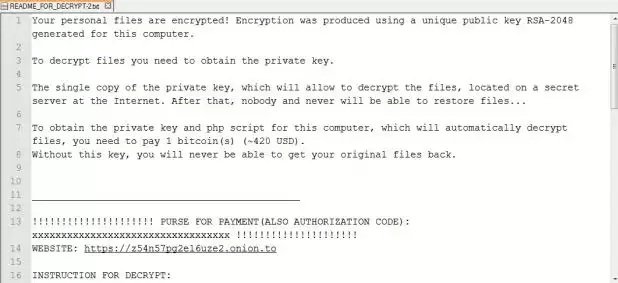
Below is an image of the ransom note presented to victims. The ransom is for 1 Bitcoin ($300-$400) only, which is below the average of 2-4 Bitcoin that most ransomware operators ask.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.