Hide your Windows 10 & Edge browser, Dyreza is coming!. A new variant of the Dyreza banking trojan comes with support for Microsoft’s latest products, the Windows 10 operating system and the Edge Web browser.
This new version of the trojan was spotted and analyzed by Heimdal Security, an EU-based cyber-security vendor, which also claims that, besides support for Microsoft’s newest tools, Dyreza will now also seek and find security products, terminating their underlying OS processes.
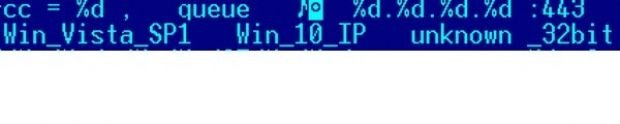
This new feature works regardless of the PC’s underlying architecture, 32-bit or 64-bit, and affects all operating systems, not just Windows 10.
By going after security products, the trojan’s creators seek to prolong their presence on an infected computer as long as possible, allowing them to steal as much information from the user’s browser.
Just as many times before, the banking trojan is delivered via the Upatre malware downloader, and just like in previous cases, all infected machines are also added to a worldwide botnet.
Previous research on this topic revealed that over 80,000 Dyreza-infected machines could be found online.
Just in time for the holiday season
What makes this new Dyreza version more dangerous is the fact that it was perfectly timed to come out right around the holiday season (Thanksgiving-Christmas-New Year), when everyone’s online and shopping activity is at its peak.
The infection pattern is the same as before. Users typically get infected with the Upatre malware downloader via spam campaigns, or when being forcibly redirected to exploit kit landing pages.
When Upatre runs, if it deems the target suitable, it will download Dyreza. From here on out, the banking trojan looks for any financial details it can find, in banking apps or by hooking into your browser.
Once data is found, it is packed neatly into an HTTP request, and sent to a remote C&C server in the control of the attacker.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.