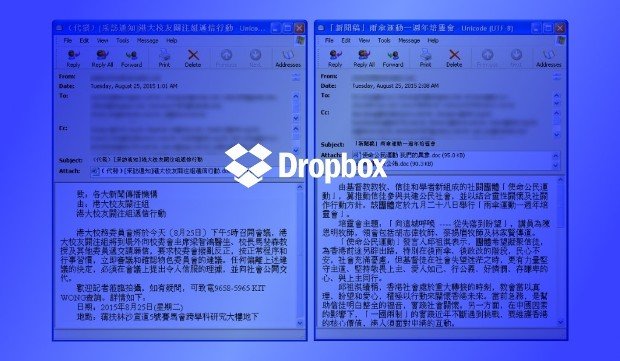
Dropbox abused by Chinese state-sponsored actors.A malware targeting mass media agencies in Hong Kong was discovered by FireEye’s security researchers. This malware, a backdoor, is unique because it hides its C&C (command and control) server inside Dropbox accounts.
According to FireEye’s threat analysis, the campaign seems to be part of a Chinese state-sponsored attack, carried out by a group previously known as admin@338.
In the past, this very same group targeted international organizations from the financial, economic and trade policy sectors, using spear phishing campaigns and current news events to infect users with Remote Access Trojans (RATs) such as Poison Ivy.
In the group’s most recent campaign, they used the same spear phishing techniques, but only targeted a small number of media agencies from Hong Kong. Initial targets included newspapers, radio and television stations.
The reason behind these attacks, first detected in August of this year, seems to be tied to last year’s Hong Kong protests against the Chinese administration, along with China’s recent economic crisis.
Spear phishing and weaponized Word documents
The state-sponsored group uses emails that contain booby-trapped Word documents that leverage current anti-Chinese and pro-democracy topics into tricking victims in opening the email attachment.
The Word file is weaponized with the CVE-2012-0158 Microsoft Office vulnerability, allowing attackers to install malware named LOWBALL on the victim’s PC.
LOWBALL is a powerful backdoor, capable of stealing local data and uploading it to a remote server, but also capable of downloading new files and executing shell commands.
LOWBALL backdoor uses Dropbox as C&C server
What made this malware stand out is the fact that the C&C server is not hosted on a Web server somewhere online but resides inside a Dropbox account.
The backdoor sends local data via the encrypted HTTPS requests on port 443, to a designated Dropbox account, utilizing Dropbox’s official API.
On the server, for each infected computer, a corresponding BAT file is created, which the attackers can update with various shell commands. LOWBALL executes this BAT file on infected machines, and all stolen data is uploaded to a Dropbox folder, corresponding to each infected computer.
Besides LOWBALL, FireEye also observed admin@338 also employ the BUBBLEWRAP malware, another backdoor, but with far less features and no Dropbox integration.
“The LOWBALL first stage malware allows the group to collect information from victims and then deliver the BUBBLEWRAP second stage malware to their victims after verifying that they are indeed interesting targets,” FireEye researchers explain.
First campaign stopped, new campaign detected
FireEye worked with Dropbox to stop the initial campaign that took place in August, but recently the two companies observed new attacks, currently ongoing.
As of now, FireEye could not verify if this campaign was the work of the admin@338 APT, nor the targets of these attacks.
The security vendor said that over 50 machines are currently being targeted, but FireEye and Dropbox’s staff could not identify their location or sector of activity.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.