Attackers can bypass authentication and access patient data. CERT/CC sounded the alarm on users of the Cardio Server ECG Management System, a broad-scope healthcare data management system used in many medical units, from small clinics to large city hospitals.
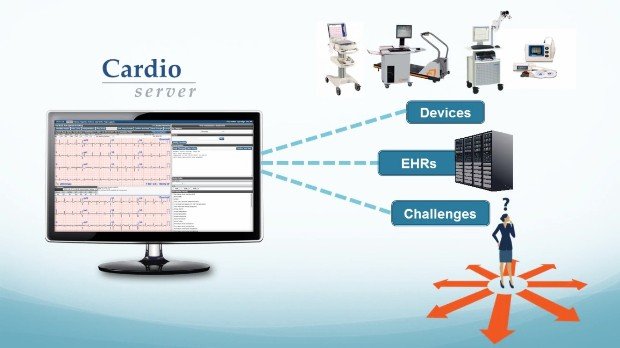
The Epiphany Cardio Server is a self-hosted Web application that provides a centralized data management system for hospitals and other medical units.
Cardio Server doesn’t only provide management features but is also a complete data acquisition system, being hardware-agnostic and capable of interfacing with over 100 devices from 40 vendors in 15 diagnostic modalities.
The application comes with a Web-based administration panel, where doctors and other administrative staff can review data, access patient history, and create reports.
According to Alex Lauerman of TrustFoundry, the older 3.3 branch of this tool is vulnerable to SQL and LDAP injection attacks (CVE-2015-6537, CVE-2015-6538). Other versions may also be affected but were not tested yet.
Vulnerabilities lead to attackers gaining admin-level access
Attackers can enter SQL commands in the Cardio Server’s login page, and due to improper input filtering, use this flaw to grant them access to the administrative account.
The same page is also vulnerable to LDAP injection attacks, allowing attackers to force the Cardio Server to perform an LDAP query to the IP address of the attacker’s choice. Just like the SQL injection, attackers can leverage the improperly sanitized login fields to launch this attack.
The most recent version of the Epiphany Cardio Server is 5.x, and the affected version 3.3 is considered out of date by its maker. Version 3.3 also requires Microsoft Windows Server 2003, another EOL product.
While this would be a non-factor in many industries, the healthcare sector is known to have extremely inconsistent and downright negligent security practices, as many reports have shown in the past. It would be no surprise to anybody if more than a few hospitals or clinics were still running Windows Server 2003 with an older version of the Cardio Server.
Source:https://news.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.