The poorly thought-out and crude surveillance technique could have a devastating effect on the country’s internet security.
In less than a month, Kazakhstan will begin enforcing a new law that requires every internet user in the country to install a backdoor, allowing the government to conduct surveillance.
In a brief statement (translated), KazakhTelecom, the country’s largest telecom, said citizens are “obliged” to install a “national security certificate” on every device, including desktops and mobile devices.
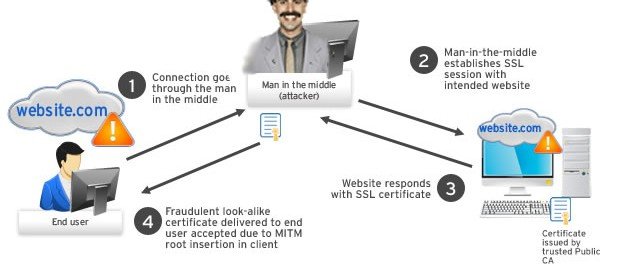
This allows the government to conduct a so-called “man-in-the-middle” attack, which allows the government to intercept every secure connection in the country and snoop on web browsing history, usernames and passwords, and even secure and HTTPS-encrypted traffic.
Telecom companies must monitor which internet users on its networks have not installed the certificate, according to a translation of the statement.
The law will go into effect on January 1.
“STUPID”
Although few specifics have been made available, the proposal has been met with extreme criticism from security experts and privacy advocates.
Security researcher Kenneth White told ZDNet that the technique would be like a “country-level Superfish,” reminiscent of its namesake controversy in which computer maker Lenovo installed adware containing a root self-signing certificate that could intercept encrypted connections.
Certificates are usually issued by trusted authorities to ensure that connections can’t be snooped on. But if a malicious authority forces or tricks a user into installing a certificate, it can be used to intercept traffic on secure connections.
“There are obvious, myriad ethical issues with this sort of mandated state surveillance,” said White. “But I suspect that the political forces pushing these measures have grossly underestimated the technical hurdles and moral backlash that lay before them.”.
“The best case scenario is that the regime will seriously weaken the security of only a subset of their citizens,” said White.
Khalil Sehnaoui, founder of Krypton Security and member of the Chaos Computer Club, called the move “stupid,” adding that the privacy issues could far outweigh the surveillance concerns.
Sehnaoui also noted that while Windows and OS X machines — as well as iOS and Android devices — are included, Linux is not.
TROUBLING, BUT ALL TOO FAMILIAR
In the wake of the Edward Snowden revelations, more and more websites are encrypting their site traffic in an effort to counter surveillance, but also to improve security and prevent impersonation.
But countries like Kazakhstan, a former Soviet state which scores as one of the worst performing nations for internet freedom and content censorship, have faced obstacles in their efforts to surveil their country’s internet. Many states cite terrorism or national security as a reason to ramp up internet surveillance.
Richard Tynan, a technologist with London-based Privacy International, said the move was a “troubling development,” but was an “all too familiar one.”
“The actions here closely mirror the proposed UK law requiring service providers to provide a back door to their users’ communications and banning end-to-end encryption,” said Tynan. “The UK government can also compel providers such as Apple, Facebook, and Google to install malware on their users’ devices.”
If the certificate falls into the hands of a hacker, malicious actor, or other nation state, it could be used to decrypt anyone’s communications.
“Undermining the security of the internet across an entire country is unnecessary and disproportionate. Our devices, networks and services, and the standards they are built on, should not betray the users; and governments need to encourage security not insecurity,” said Tynan.
Questions remain about exactly how this law will be implemented, or if software giants like Microsoft — which have the power to revokeuntrustworthy certificates — will intervene.
Source:https://www.zdnet.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.