API used a simple authentication scheme, exposing users to CSRF attacks that allowed third-parties to hijack accounts.
Verizon fixed an issue in its My FiOS REST API that would have allowed an attacker to hijack user accounts by tricking users into accessing a malicious Web page.
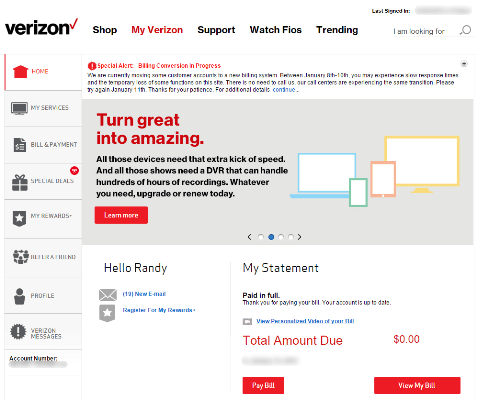
Verizon My FiOS is a mobile application that lets Verizon customers manage the details of their accounts, like bills, current services, rewards, voicemail, call logs, and various other Verizon-related options.
Independent security researcher Randy Westergren, who previously discovered another vulnerability that compromised the email accounts of all Verizon My FiOS users, found another one that was also exploitable via the app’s API.
Working on top of his previous discovery, that the REST API used cookies for authenticating users, Mr. Westergren discovered that, by logging into his Verizon account via the browser and then accessing the app’s REST API URL, he would have had access to all the data usually displayed in his app, but now shown inside his browser.
This type of authentication scheme is dangerous, being the source of so-called CSRF attacks or cross-site request forgery.
Insecure API authentication scheme leaves users open to account hijacking
By leveraging this loophole in the app’s API authentication scheme, Mr. Westergren was able to craft a malicious Web page that would send emails on another user’s behalf to his own account.
He later expanded on his finding by creating another PoC (proof-of-concept) malicious page that, when opened inside a victim’s browser, would trigger a password reset.
“Simultaneously, the PoC executes requests that change both the security questions and the zip code on the victim’s Verizon account,” Mr. Westergren explains. “Almost immediately, an attacker would have been able to move through the Forgot Password functionality (using the information he set in the PoC) and reset the victim’s password.”
He reported the issue to Verizon at the middle of October 2015, and the company’s security staff fixed the problem by November 3.


Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











