Ricochet is the most secure encrypted anonymous messenger that sends no metadata.
The security experts have approved a new internet messaging tool that bypasses the federal government’s metadata collection system to help human rights activists and journalists protect whistleblowers.
Called the Ricochet, this software has been in development for around two years. However, following a formal security audit conducted in the United States, the team that is behind its creation says it is ready for use.
Security authorization of Ricochet was a main step forward for investigative reporting said Dr Suelette Dreyfus, a vocal privacy advocate and University of Melbourne information system researcher who has already been teaching journalism students how to use it.
“The release of Ricochet with its audit is a moment for celebration because, even if you’re not a journalist or a source, as a member of the public you should feel happier that it’s now a little safer for sources to reveal wrongdoing to journalists and for journalists to tell the truth about that wrongdoing. That’s definitely something worth celebrating,” Dr Dreyfus said.
An internationally recognised security podcaster and one of the leading figures behind the Ricochet project, Patrick Gray said that as a journalist his interest in the software was “selfish”.
He said that the important aspect of the software was to offer sources and whistleblowers with a secure, anonymous and simple means to reveal details to journalists without leaving a communication trace that could uncover them.
Mr Gray said “It’s that first contact problem that is a big issue in journalism and this software essentially solves that.”
He said that Ricochet would be able to provide a level of security and secrecy that is unthinkable with current messaging software, including Wickr — the self-destructing message platform preferred by Prime Minister Malcolm Turnbull.
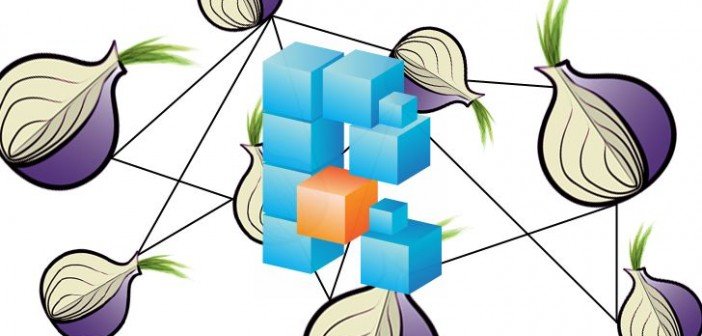
Talking about the infamous online black on which drug dealers prospered until the FBI closed it in November 2014, Mr Gray said, “The key difference between Ricochet and anything else that’s out there is that it does not use a server. It uses the same technology that ran Silk Road, it uses dark web technology.”
Hearteningly, Mr Gray said, the software seems to have already managed to get all the attention from Chinese nationals.
Ricochet is the outcome of hundreds of hours of volunteer work. Mr Gray has not only worked with other high profile personalities in the information security sector including HD Moore and another anonymous but also with widely known security expert nicknamed as “thegrugq”.
To begin with, the group branded its efforts under a project known as invisible.im — a short form for invisible instant messaging.
The group had made plans to create the system from scratch. However, a young software developer called John Brooks who around 18 months ago had developed Ricochet in his spare time approached invisible.im looking for support.
Invisible.im put all its efforts behind Ricochet, while Mr Gray managed to get a modest amount of financing that could let Mr Brooks to give more time to work on it.
In order to carry out a security audit on the software, Dr Dreyfus assisted the group get a grant from the US-based Open Technology Fund to pay US security consultancy NCC Group.
“Before this we had a disclaimer on it warning people not to use it for anything serious. It was ‘experimental software’ and we couldn’t encourage people to use it as they would other messenger software. Now we can say it’s been checked, it’s been audited and people can use it. We can’t say there are no bugs in it but we can say it’s not a hopelessly vulnerable, bug-riddled mess. It’s less experimental,” Mr Gray said.
Dr Dreyfus said that the advantage of making the software available would offset any hazards that it could be used for malicious purposes such as terrorist operations and cloaking criminal.
“You have to accept that there are tools, which on balance are a much greater good to society even though there’s a tiny possibility they could be used for something less good,” she said.
Ricochet meant for one-to-one communications would be less interesting for criminal and terrorist organisers that need many-to-many communications to perform attacks and operations, Mr Gray disputed.
Nevertheless, the criminals and terrorists had so many encryption and anonymising technologies at their disposal that directing fingers at any one of them was useless, said Mr Gray.
Source:https://www.techworm.net/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.