Security experts presented the DROWN attack that exploits a new critical security vulnerability affecting the OpenSSL.
Security experts have discovered a new critical security vulnerability affecting the OpenSSL, it has been estimated that more than 11 Million websites and e-mail services are open to cyber attacks.
The new attack, dubbed DROWN (stands for Decrypting RSA with Obsolete and Weakened eNcryption), allow attackers to access users’ sensitive data over secure HTTPS communications.
“If you’re running a web server configured to use SSLv2, and particularly one that’s running OpenSSL (even with all SSLv2 ciphers disabled!), you may be vulnerable to a fast attack that decrypts many recorded TLS connections made to that box. Most worryingly, the attack does not require the client to ever make an SSLv2 connection itself, and it isn’t a downgrade attack. Instead, it relies on the fact that SSLv2 — and particularly the legacy “export” ciphersuites it incorporates — are pure poison, and simply having these active on a server is enough to invalidate the security of all connections made to that device.” states the high-level description of the attack.
The attack could be successfully carried out in a few hours and in some cases the attackers is able to decrypt traffic in a few seconds.
“We’ve been able to execute the attack against OpenSSL versions that are vulnerable to CVE-2016-0703 in under a minute using a single PC. Even for servers that do not have these particular bugs, the general variant of the attack, which works against any SSLv2 server, can be conducted in under 8 hours at a total cost of $440.” explained the researchers.
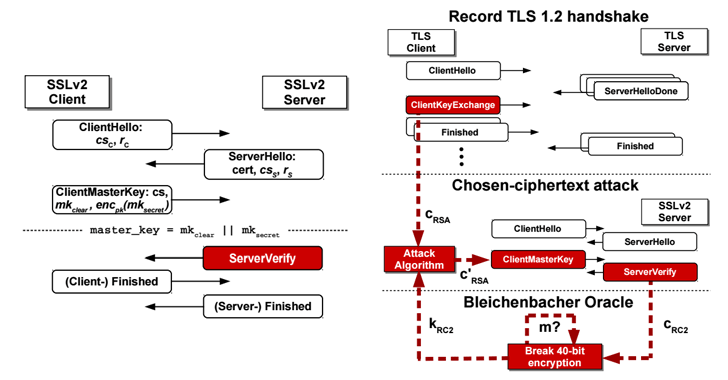
DROWN is a cross-protocol attack that exploits vulnerabilities in the SSLv2 implementation against transport layer security (TLS), the attacks doesn’t work against the SSLv2 connections.
DROWN exploits a bug in SSLv2 protocol implementation to attack the security of connections made under a different protocol, in this case, TLS.
By using the Bleichenbacher attack, threat actors can decrypt the private RSA keys and unlock “secure” servers that use the same private key.
The attacker just needs to send specially crafted malicious packets to a server to decrypt HTTPS connections.
“You’re just as much at risk if your site’s certificate or key is used anywhere else on a server that does support SSLv2,” security researchers noted. “Common examples include SMTP, IMAP, and POP mail servers, and secondary HTTPS servers used for specific web applications.”
A group of researchers from universities in Germany, the US and Israel alongside with two OpenSSL developers, have implemented the attack and demonstrated they can decrypt a TLS 1.2 handshake using 2048- bit RSA in under eight-hours using Amazon EC2, at a cost of $440.
The impact of the DROWN is serious, it has been estimated that more than 33 percent of all HTTPS servers is vulnerable to the attack, roughly 11.5 Million servers worldwide, including Alibaba, BuzzFeed, Flickr, Samsung, Sina, StumbleUpon, Weibo, Yahoo, and 4Shared.
The DROWN attack also works against Microsoft’s Internet Information Services versions 7 and earlier, as well as prior to 3.13 versions of the Network Security Services (NSS) Cryptographic library.
A patch for the vulnerability is already available in the last OpenSSL update.
Security experts have no doubts, now that the DROWN attack has been disclosed threat actors may actively exploit the flaw to attack servers.
Users need to update their OpenSSL to the newer versions 1.0.2g or 1.0.1s. In order to avoid the attack, it is possible to disable the SSLv2, as well as make sure that the private key isn’t shared across any other servers.
If you want to receive more details on the attacks give a look to the paper “DROWN: Breaking TLS using SSLv2” or give a look to the interesting post published by Matthew Green, a professor at Johns Hopkins University.
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











