Printed electronics makes the perfect fake fingerprint. Boffins from Michigan State University have loaded up an inkjet printer with cartridges designed for printing electronic circuits, and used the output to fool smartphone fingerprint sensors.
All that’s needed is a scan of the victim’s fingerprint (reversed so it presents the right way when printed), and a suitable inkjet printer loaded up with ink and paper from printed electronics specialist AGIC.
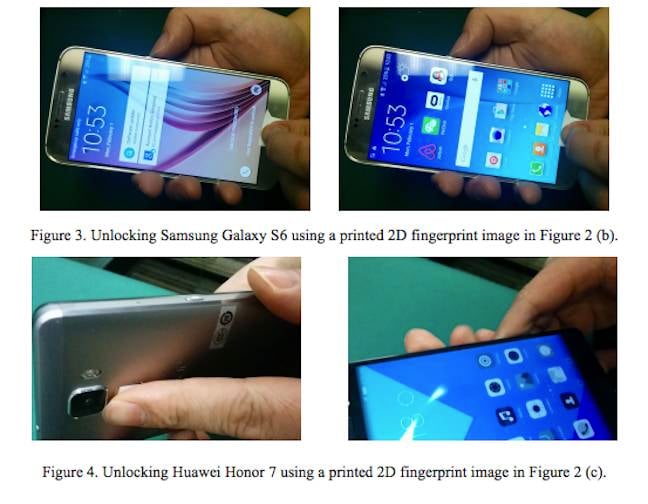
In their paper (PDF) the researchers, Kai Cao and Anil Jain from the university’s Department of Computer Science and Engineering cracked a Samsung Galaxy S6 and a Huawei Honor 7.
It’s a much simpler approach than the “gummy bear fake fingerprint”, which needs materials like latex milk or white wood glue.
As the researchers note, in that kind of attack you have to wait 30 minutes for the imprint to set, and there’s a fair amount of D-I-Y skill needed to turn a fingerprint into a spoof without spoiling it.
Scanning and reversing a fingerprint, loading a printer with electronics cartridges (and one black cartridge), and printing the result on the appropriate paper is much simpler.
While the Huawei phone was slightly harder to spoof than the Samsung, the paper says the researchers worked with several volunteers and they were ultimately successful on all attempts.
Although it won’t work for all smartphones, the researchers reckon there’s an “urgent need for antispoofing techniques for fingerprint recognition systems” since mobiles are being used for payment systems.
Source:https://www.theregister.co.uk/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











