Proofpoint researchers prevent bank cyber-heists. Carbanak, the cybercriminal group that robbed more than $1 billion from 100 banks across 30 countries in 2013 and 2014, has been seen once again, and this time, security researchers say they’ve caught the group in their early attack stages.
In February 2015, the world was shocked to find that cybercriminals managed to steal over $1 billion from so many banks for almost two years without being detected.
Leveraging advanced infiltration and exfiltration techniques, Carbanak operated in the shadows, using the Anunak and Carberp malware to infect and then steal money from banks across the world, with the majority located in Russia.
The group took a break after security researchers ousted them in February 2015, but last autumn, and later in February this year, the group returned with new attacks, but this time around against financial institutions and the financial departments of multinational companies.
Carbanak now targets banks in the US, Australia and Middle East
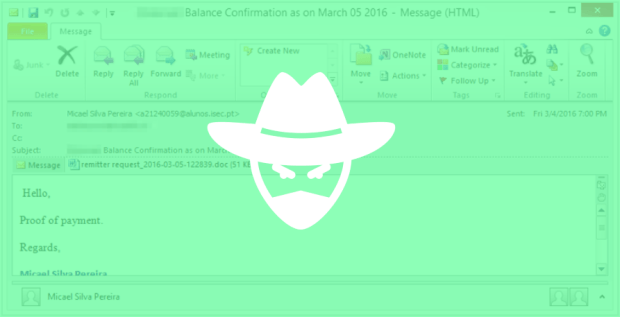
Now, security firm Proofpoint says that it detected a new wave of spear-phishing campaigns that are pushing some of Carbanak’s malware, along with a new threat.
These spear-phishing campaigns are directed at high-level executives in banks located in 18 countries, with most attacks hitting the US, Oman, Australia, Kuwait, and the United Arab Emirates.
“The group also expanded its targeting from financial institutions to seemingly unrelated targets in fire, safety, and HVAC,” Proofpoint experts noted. “However, as we learned from the Target data breach, among others, vendors and suppliers can give attackers a point of entry into their real target.”
Carbanak developed new malware called Spy.Sekur
The spear-phishing emails come boobytrapped with Word documents that when opened will leverage the CVE-2015-2545 Microsoft Office vulnerability to infect the target’s PC with malware.
As Proofpoint explains, the group has developed new malware. This new threat is identified as Spy.Sekur, a Remote Access Trojan (RAT), used to open backdoors on infected workstations.
Besides Spy.Sekur, security researchers also say Carbanak deployed other, more well-known RATs, such as DarkComet, jRAT, and MorphineRAT.
Because spear-phishing campaigns are usually the first stage of any cyber-crime campaign, it appears that Proofpoint caught Carbanak red-handed, right in the middle of a new wave of attacks.
Source:https://www.softpedia.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.