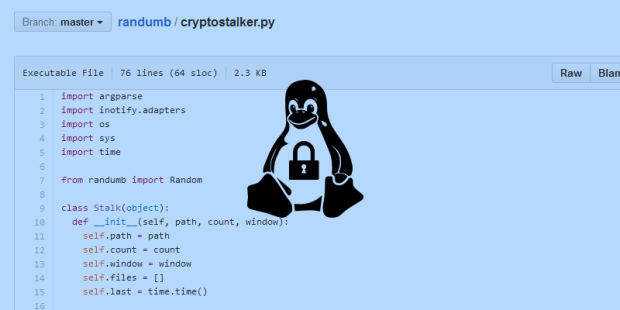
Softpedia talked with Sean Willians, author of Cryptostalker. A while back, we stumbled upon an interesting GitHub repo dubbed randumb, which included an example called Cryptostalker, advertised as a tool to detect crypto-ransomware on Linux.
Cryptostalker and the original project randumb are the work of Sean Williams, a developer from San Francisco. Mr. Williams wanted to create a tool that monitored the filesystem for newly written files, and if the files contained random data, the sign of encrypted content, and they were written at high speed, it would alert the system’s owner.
Right now, the project is only available for Linux, but as you can read below in our interview with Mr. Williams, there’s a plan to port the tool for Windows.
If tests go well enough, then Windows users may have a new method of getting warned against the deadly wave of crypto-ransomware that’s been recently hitting users around the globe.
How did you come up with the idea to develop the Cryptostalker library?
SW: I primarily run Linux and OS X machines, both personally and at work, so I wasn’t directly affected by ransomware. My father did get infected with an early version of CryptoLocker, so my father’s experience, coupled with the fact that this stuff is on the steep incline, caused me to focus some effort one evening.
Thankfully, my father had backups and ransomware wasn’t yet smart enough to search too hard for backup mechanisms and encrypt those too.
Oddly, a few months back I wrote a small piece of software that tries to detect entropy in data. So the invention of Cryptostalker was a mere coupling of this software with the mechanism to detect crypto-ransomware behavior.
Cryptostalker is simple, and stands to be refined, but it works as-is to detect common strains of ransomware.
Have any users or companies shown interest in the technology?
SW: I haven’t yet been contacted by any company using it or taking its logic to write something of their own. I’ve got to imagine there are folks out there doing something similar.
Cryptostalker is in a PoC state at the moment. I haven’t performance-tested it yet, and I’d love to see results from deployments in various environments to refine false positives.
Python is a cross-OS platform. Have you tried Cryptostalker on Mac or Windows? Do you plan on porting the library?
SW: Since most ransomware infections are on Windows, I’ll next port Cryptostalker there, and then OSX. Maybe some of your readers can help!
How do you see the project evolving? Any planned features?
SW: My primary focus with Cryptostalker is to make it cross-platform. Then ensure it’s as performant as possible. If necessary, I’ll write it in a faster language other than Python. At least as important as performance is the false-positive rate – this has to be low or it’s a worthless tool. The detection sensitivity can be tweaked with the tool in its current state, but I think there’s more work here.
The ransomware I’ve seen won’t encrypt files if the command and control server cannot be contacted to fetch an encryption key or report the one it generated on its own. So, one general approach to preventing this is the same as preventing other malware. That is, detecting anomalous behavior on the endpoint, such as suspicious communications. But this is hard stuff.
How do you see ransomware evolving?
SW: The primary reason I aim for Cryptostalker to be cross-platform is because the evolution of ransomware is wherever the users are. A few months back the first public Linux crypto-ransomware, commonly referred to as Linux.Encoder.1, was discovered. And more recently with the first public OS X strain. I all but guarantee there are more infections that don’t see the light of day. So first and foremost, a broadening of reach is underway.
Secondly, more sophisticated variants have turned up recently. We now see encryption of backups and network storage. We’ve seen entire networks targeted for ransom and not merely opportunistic infection.
Verizon’s DBIR of 2015 reported ransomware as 4.9% of infections. I think this will spike and has already. Services that give criminals essentially point-and-click ability to create their very own ransomware have been around for a year (Tox and probably others). So, ease of creation coupled with lack of widespread preventive tools that work—contrary to oft grandiose marketing claims—will likely propel ransomware to among the more lucrative forms of compromise in 2016.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.