A new ransomware has been released that not only encrypts your files, but also deletes them if you take too long to make the ransom payment of $150 USD. The Jigsaw Ransomware, named after the iconic character that appears in the ransom note, will delete files every hour and each time the infection starts until you pay the ransom. At this time is currently unknown how this ransomware is distributed.
This is the first time that we have seen these types of threats actually being carried out by a ransomware infection. The good news is that a method has been discovered that allows victims to decrypt their files for free.
Jigsaw Ransomware is serious about its threats…
It is not the first time that we have seen ransomware threaten to delete files, but this is the first time that one has actually carried out its threats. The Jigsaw Ransomware deletes files every 60 minutes and when the program is restarted.
Every hour, the Jigsaw Ransomware will delete a file on your computer and increment a counter. Over time this counter will cause more than one file to be deleted every hour.
More destructive, though, is the amount of files that are deleted every time the ransomware starts. After the initial infection, when the ransomware it restarted, whether that be from a reboot or terminating the process, Jigsaw will delete a thousand, yes a thousand, files from the victim’s computer.
This process is very destructive and obviously being used to pressure the victim into paying the ransom.
How to decrypt and remove the Jigsaw Ransomware
Thankfully, through the analysis of MalwareHunterTeam, DemonSlay335, and myself it was discovered that it is possible to decrypt this ransomware for free. Using this information, Demonslay335 has released a decryptor that can decrypt files encrypted by the Jigsaw Ransomware. To decrypt your files, the first thing that you should do is terminate the firefox.exeand drpbx.exe processes in Task Manager to prevent any further files from being deleted. You should then run MSConfig and disable the startup entry called firefox.exe that points to the %UserProfile%\AppData\Roaming\Frfx\firefox.exe executable.
Once you have terminated the ransomware and disabled its startup, let’s proceed with decrypting the files. The first step is to download and extract the Jigsaw Decryptor from the following URL:
https://download.bleepingcomputer.com/demonslay335/JigSawDecrypter.zip
Then double-click on the JigSawDecrypter.exe file to launch the program. When the program launches you will be greeted with a screen similar to the one below.
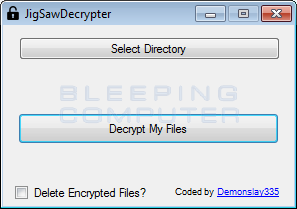
To decrypt your files simply select the directory and click on the Decrypt My Files button. If you wish to decrypt the whole drive, then you can select the C: drive itself. It is advised that you do not put a checkmark in the Delete Encrypted Files option until you have confirmed that the tool can properly decrypt your files.
When it has finished decrypting your files, the screen will appear as below.
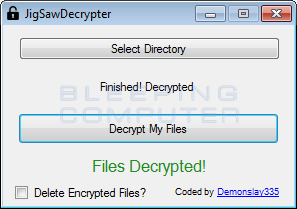
Now that your files are decrypted, I suggest that you run an antivirus or anti-malware program to scan your computer for infections.
Jigsaw Ransomware Technical Details
When the Jigsaw ransomware is launched it will scan your drives for certain file extension, encrypt them using AES encryption, and append the .FUN extension to the filename. The files targeted by the Jigsaw ransomware are:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp , .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .c, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .Qbw, .QBB, .QBM, .QBI, .QBR , .Cnt, .Des, .v30, .Qbo, .Ini, .Lgb, .Qwc, .Qbp, .Aif, .Qba, .Tlg, .Qbx, .Qby , .1pa, .Qpd, .Txt, .Set, .Iif , .Nd, .Rtp, .Tlg, .Wav, .Qsm, .Qss, .Qst, .Fx0, .Fx1, .Mx0, .FPx, .Fxr, .Fim, .ptb, .Ai, .Pfb, .Cgn, .Vsd, .Cdr, .Cmx, .Cpt, .Csl, .Cur, .Des, .Dsf, .Ds4, , .Drw, .Dwg.Eps, .Ps, .Prn, .Gif, .Pcd, .Pct, .Pcx, .Plt, .Rif, .Svg, .Swf, .Tga, .Tiff, .Psp, .Ttf, .Wpd, .Wpg, .Wi, .Raw, .Wmf, .Txt, .Cal, .Cpx, .Shw, .Clk, .Cdx, .Cdt, .Fpx, .Fmv, .Img, .Gem, .Xcf, .Pic, .Mac, .Met, .PP4, .Pp5, .Ppf, .Xls, .Xlsx, .Xlsm, .Ppt, .Nap, .Pat, .Ps, .Prn, .Sct, .Vsd, .wk3, .wk4, .XPM, .zip, .rar When encrypting a file it will add the filename to a list of encrypted files located at %UserProfile%\AppData\Roaming\System32Work\EncryptedFileList.txt. It will also assign a bitcoin address and save it in the%UserProfile%\AppData\Roaming\System32Work\Address.txt file.
Finally, Jigsaw will set an autorun that starts ransomware each time you login to Windows. Unfortunately, each time the ransomware starts, it will also delete 1,000 of the encrypted files.
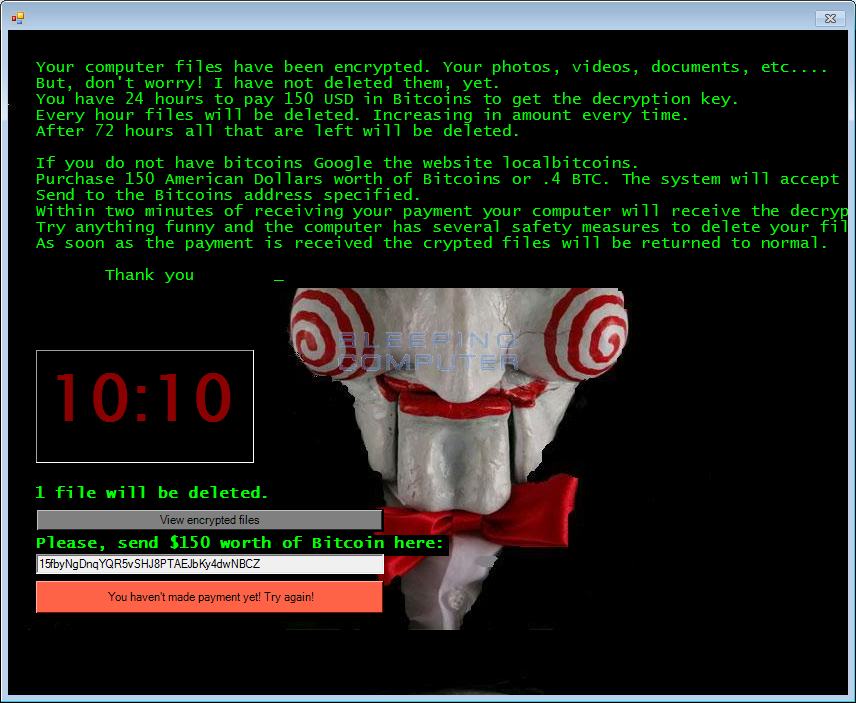
In the ransom note there is a 60 minute timer that counts down to 0. When it reaches 0 it will delete a certain amount of files depending on how many times the counter has reset. Each time it resets, a counter will increase, which will cause more files to be deleted on the next reset.
The text of this ransom note is: Your computer files have been encrypted. Your photos, videos, documents, etc….
But, don’t worry! I have not deleted them, yet.
You have 24 hours to pay 150 USD in Bitcoins to get the decryption key.
Every hour files will be deleted. Increasing in amount every time.
After 72 hours all that are left will be deleted.
If you do not have bitcoins Google the website localbitcoins.
Purchase 150 American Dollars worth of Bitcoins or .4 BTC. The system will accept either one.
Send to the Bitcoins address specified.
Within two minutes of receiving your payment your computer will receive the decryption key and return to normal.
Try anything funny and the computer has several safety measures to delete your files.
As soon as the payment is received the crypted files will be returned to normal.
Thank you
When a victim sends a ransom payment, they can click on the check payment button. When this button is clicked, the ransomware queries the https://btc.blockr.io/ site to see if a payment has been made to the assigned bitcoin address. If the amount of bitcoins in the assigned address is greater than the payment amount, then it will automatically decrypt the files.
Files associated with the Jigsaw Ransomware
%UserProfile%\AppData\Roaming\Frfx\
%UserProfile%\AppData\Roaming\Frfx\firefox.exe
%UserProfile%\AppData\Local\Drpbx\
%UserProfile%\AppData\Local\Drpbx\drpbx.exe
%UserProfile%\AppData\Roaming\System32Work\
%UserProfile%\AppData\Roaming\System32Work\Address.txt
%UserProfile%\AppData\Roaming\System32Work\dr
%UserProfile%\AppData\Roaming\System32Work\EncryptedFileList.txt
Registry entries associated with the Jigsaw Ransomware
HKCU\Software\Microsoft\Windows\CurrentVersion\Run\firefox.exe %UserProfile%\AppData\Roaming\Frfx\firefox.exe
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











