The cyberattack that knocked hundreds of school networks offline in Japan last week had at least one novel feature: It was allegedly instigated by a student.
A 16-year-old high school student who said he was frustrated with his teachers unleashed an attack on the Osaka Board of Education server that took 444 elementary, junior high and high school networks offline, investigators said.
The student monitored the attack from his cellphone and later told authorities that he wanted to join hacktivist group Anonymous, according to the investigators.
Unusual until recently, student-launched attacks are becoming more common, said Radware security researcher Daniel Smith. The firm issued a threat advisory alert this week.
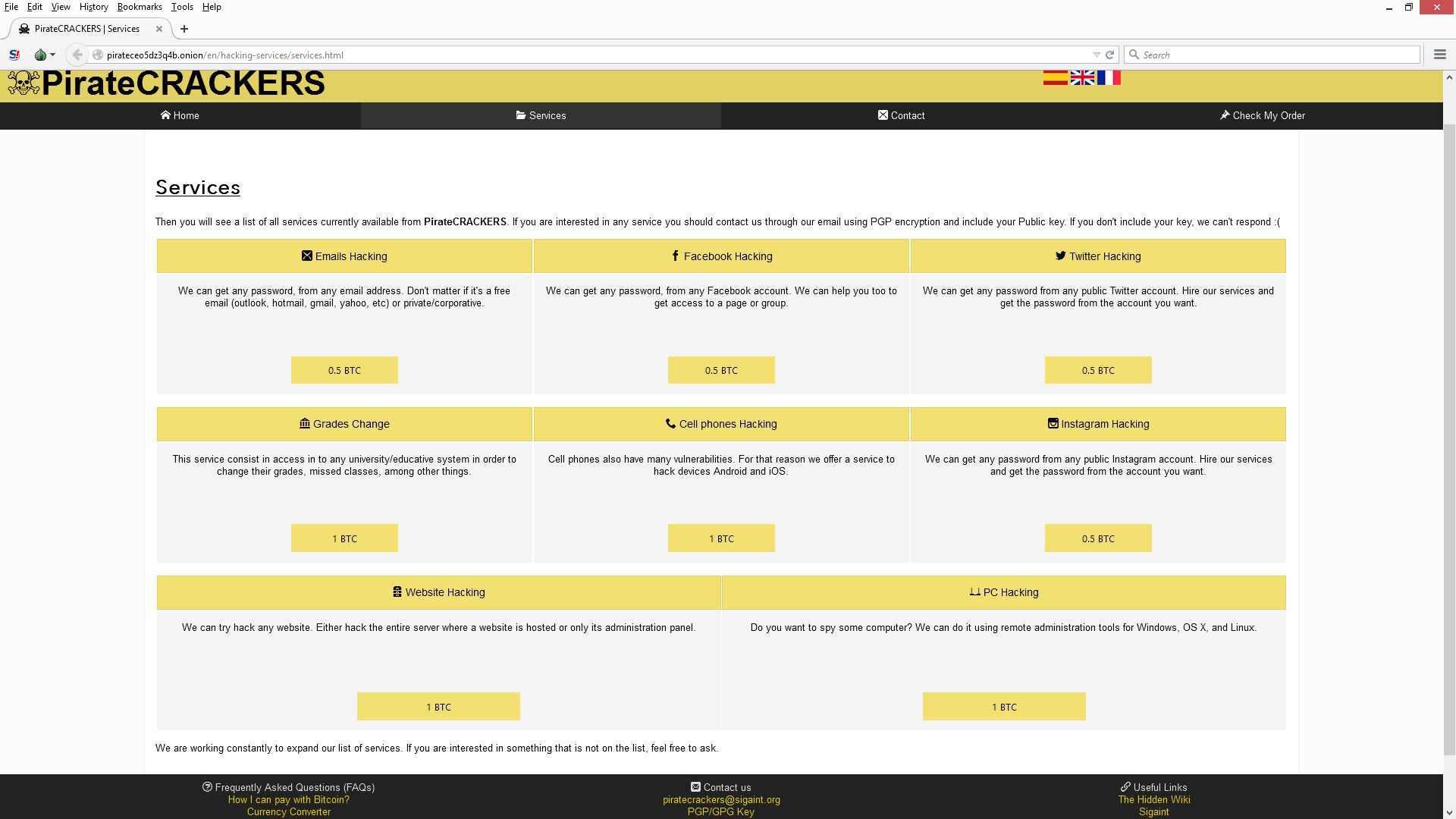
Like the rest of the world, schools and universities are increasingly reliant on cloud-based infrastructure to function, making them more vulnerable to attack. At the same time, the widespread availability of free or inexpensive hacking software and services means malicious students no longer need special skills to cause trouble.
“We have been getting approached by education institutions or regional IT firms who say they are starting to see some increased attack activity,” said Smith.
Aggression toward a school or staff member is one of several common motivations for the attacks. Others include delaying tests, changing grades and manipulating the registration process to gain an advantage over other students.
In the U.S., Rutgers, Arizona State University and the University of Georgia have had denial-of-service attacks in the past year. These attacks are often so effective that they completely overwhelm networks and prevent students, teachers and administrators from being able to log on. This wreaks havoc on large administrations and results in delays, for example, in class registration and final exams.
The Rutgers attacker, who has not been caught but is believed to be a student and reportedly goes by the name “Exfocus”, carried out six attacks over the course of a year, starting in November 2014.
“He wanted to show the vulnerabilities inside the college network,” said Smith. “It was very simple for him to topple the network, and it caused a lot of issues for students and staff members.”
Attackers are taking aim at student portals, admission processing sites, mail servers and sensitive databases holding personal information. They are also targeting educational platforms connecting students and institutions including Blackboard and Moodle. One such example took aim at Janet, a research and educational network connecting 19 regional universities in England, which has fallen victim to several DDoS attacks over the past year.
Of course, just because these attackers are often still in high school does not mean they will get off lightly. A 15-year-old in Adelaide, Australia, could face 10 years in prison for allegedly launching one for the largest DDoS attacks the country has ever witnessed. The attack was directed at several organizations, including Reynella East College, and was so widespread that it impacted around 10,000 customers of internet service provider NuScope.
Source: cnbc.com

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.