The hacker responsible for leaking 400GB of data from Italian spyware firm Hacking Team has published a tutorial video showing those seeking to follow in his footsteps how to hack a police website.
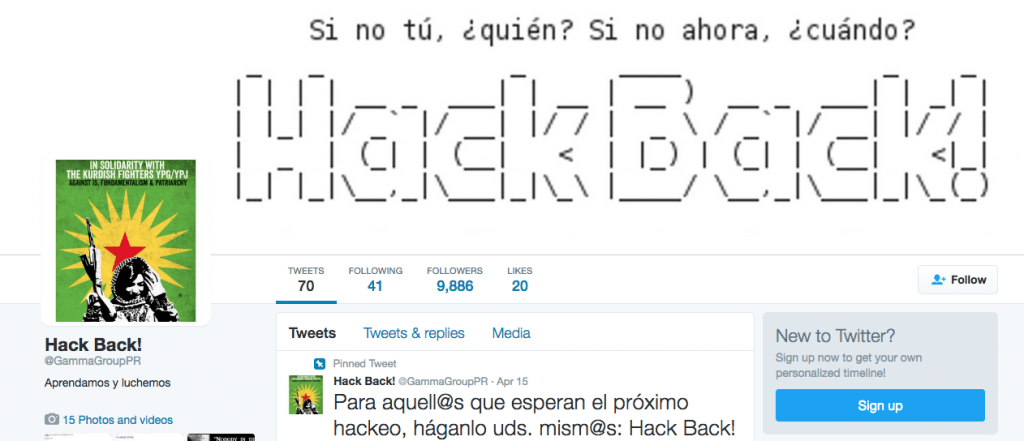
Known variously as Phineas Fisher, GammaGroupPR and Hack Back, the anonymous hacker published the video on YouTube showing how he hacked the website of the Catalan Police Union or Sindicat De Mossos d’Esquadra (SME). The hacker is seen obtaining data, including police officers’ names, bank details and badge numbers — all of which he has since dumped online.
YouTube removed the video as it violated the company’s policies but the hacker has published several mirrors of the video elsewhere online and while some have been taken offline, at least one remains live at the time of publication.
Phineas Fisher rose to prominence in July 2015 when he published a huge trove of data, including company emails and documents as well as the source code of the company’s intrusive spying tools on the internet, revealing details of which governments and law enforcement agencies the company was working with, including the FBI, Drug Enforcement Agency and Department of Defense.
In April the hacker revealed how he was able to remain inside Hacking Team’s system for weeks without being noticed while giving potential hackers a guide on using common hacking techniques.
Earlier this week it was revealed that the same hacker claimed responsibility for giving $11,200 worth of bitcoin to Rojava, an autonomous region in northern Syria, describing it as “one of the most inspiring revolutionary projects in the world today.” The hacker subsequently confirmed the money had been stolen from a bank. “Bank robbing is more viable than ever, it’s just done differently these days,” he said in a comment on Reddit.
In his 39-minute video, which is accompanied by songs including NWA’s “F**k the Police,” the hacker is seen using Kali Linux, a version of the operating system designed for penetration testing but commonly used by hackers, to probe the SME website to see if it is vulnerable to a particular type of attack, known as SQL injection.
The reason the hacker is targeting the SME is over alleged abuses the officers in the force have committed, including incidents that are alleged to have occurred on Feb. 4, 2006, when the eviction of a building being used as a squat resulted in a policeman being left a quadriplegic — resulting in the alleged torture of suspects by other members of the force.
The identity of the hacker remains unknown, but according to Hacking Team CEO David Vincenzetti, “multiple law enforcement investigations are underway in several countries. We hope that the vigilante’s barging about his work will lead to his swift arrest and prosecution.”
Phineas Fisher targeted Hacking Team as it is one of a number of companies that specialize in finding — or buying — hardware and software vulnerabilities to utilize in their own surveillance tools that they sell to governments and law enforcement agencies. Hacking Team claims it sells only to organizations in countries approved by the United Nations. However, the leak revealed the company had been doing business with countries such as Sudan, which are on the U.N. blacklist, despite telling U.N. investigators it had no business relationship with the African country.
Source: ibtimes.com

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











