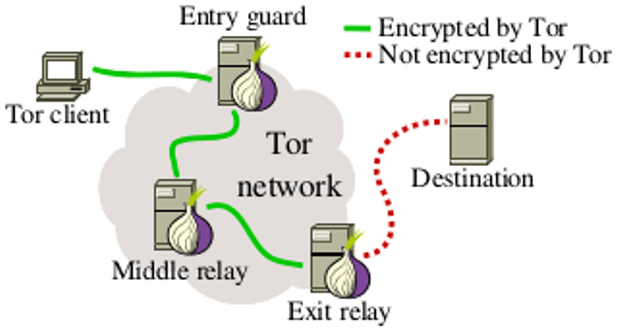
When it comes to accessing public websites, Tor has an intrinsic security problem: though the nodes between your computer and the public internet are unable to see where the traffic is coming from or going to, the final hop in the network (known as an exit node) gets to know what webserver you are connecting to.
If that final hop isn’t protected by an HTTPS connection — if it takes place without encryption — then all the traffic between you and the webserver are an open book to the exit node. It can see what you send and what you receive, and it can tamper with the connection (for example, it can inject malicious code that exploits bugs in your browser to take it over). If your session includes identifying information — your Google cookie, say, or a login and password — then someone running a spying exit node can figure out who you are without having to poison your session. This was much more of a problem when HTTPS connections were more rare, but now, thanks to the Snowden revelations and projects like Let’s Encrypt, much of the web is encrypted by default. That means that a spying exit node will only be able to see which server is being accessed, but not which page, and will not be able to inject code into the session, and will not be able to see the data going to and from the server.
There aren’t many exit nodes out there. Many people fear that running an exit node will put them in police crosshairs if it gets used in the commission of a crime. For the record, Boing Boing runs a very high-capacity exit node, and though we’ve received multiple contacts from US law enforcement, we’ve just explained that this is a Tor node that runs with logging switched off, and thus we have no information that’ll be relevant to any investigations, and the officers involved have thanked us and gone away without further trouble.
The lack of exit nodes means that if you run an exit node and want to spy on people, you can see an appreciable fraction of all the Tor traffic that goes to and from the public internet. Many governments, including the Chinese government, are understood to be running high-availability exit nodes that snoop on and log all the traffic they can see.
One answer to this problem is Tor “hidden services.” These are servers that have no public internet address; rather, they are accessed directly through the Tor network, without traffic ever being routed through an exit node. Because all this traffic takes place in the Tor network, without the intermediate nodes ever getting access to decrypted information, the sessions are considered very secure. Notorious darknet sites like The Silk Road ran as hidden services, and many sites maintain hidden service versions of their public offerings: for example, Facebook can be accessed on the Tor network via https://www.facebookcorewwwi.onion/, which resolves to a machine in one of Facebook’s data centers in Oregon, which is then bridged into the rest of Facebook’s system. By accessing Facebook over a .onion hidden service, you can disguise the fact that you’re visiting Facebook at all, and bypass censoring firewalls, like those used by schools, employers and governments.
However, hidden services are not without their own security issues. A pair of security researchers from Northeastern University have announced a paper(to be delivered at this summer’s Def Con hacker convention in Las Vegas) that reveals over 100 spying Tor nodes that were shown to be targeting hidden services.
These nodes — ordinary nodes, not exit nodes — sorted through all the traffic that passed through them, looking for anything bound for a hidden service, which allowed them to discover hidden services that had not been advertised. These nodes then attacked the hidden services by making connections to them and trying common exploits against the server-software running on them, seeking to compromise and take them over.
The researchers used “honeypot” .onion servers to find the spying computers: these honeypots were .onion sites that the researchers set up in their own lab and then connected to repeatedly over the Tor network, thus seeding many Tor nodes with the information of the honions’ existence. They didn’t advertise the honions’ existence in any other way and there was nothing of interest at these sites, and so when the sites logged new connections, the researchers could infer that they were being contacted by a system that had spied on one of their Tor network circuits.
This attack was already understood as a theoretical problem for the Tor project, which had recently undertaken a rearchitecting of the hidden service system that would prevent it from taking place.
No one knows who is running the spying nodes: they could be run by criminals, governments, private suppliers of “infowar” weapons to governments, independent researchers, or other scholars (though scholarly research would not normally include attempts to hack the servers once they were discovered).
“We create what we call ‘honey onions’ or ‘honions.’ These are onion addresses that we don’t share with anyone,” Noubir said. If someone visits the sites, it’s a good indication that their service has been picked up by a malicious HSDir.
At any one time, the pair ran 4,500 honey onions over 72 days, and found at least 110 HSDirs spying on hidden services. Some of the actors behind these weren’t just passive observers; many came back and then aggressively probed the hidden services.
“They’re looking for vulnerabilities in the web server,” Sanatinia said. Those attackers might look for cross-site scripting attacks, SQL-injection vulnerabilities, or just try to find the server’s status page, which can reveal lots of interesting, and potentially identifying, information about the site.
Most of the dodgy HSDirs the researchers found were hosted in the US, followed by Germany, France, and then other European countries. Of course, that doesn’t necessarily mean their operators are based in the same country; anyone can whip up a remote server from pretty much anywhere in the world. And because over half of the 110 nodes were hosted on cloud infrastructure, it’s not easy to immediately pin down who’s behind them.
Source:https://boingboing.net

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.