Decrypter works with older Jigsaw versions as well. Security researchers from Check Point announced over the weekend that they identified a way to decrypt files locked by the Jigsaw ransomware, both new and older versions.
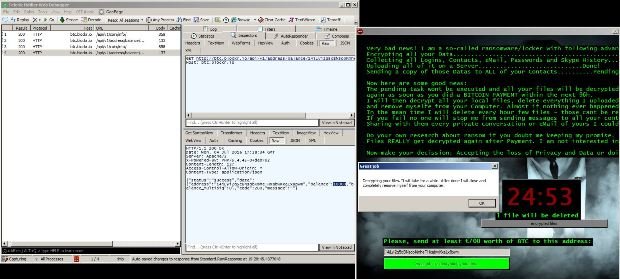
Jigsaw appeared this past April, and the ransomware made a name for itself because it was deleting files from the user’s computer as time went by without receiving a ransom payment. Additional computer restarts would also delete 1,000 more files.
Researchers created a free Jigsaw decrypter when the ransomware first came out, but it stopped working after subsequent updates, which the ransomware received on a regular basis, Jigsaw being one of the most updated ransomware variants at the moment, with new versions coming out almost on a weekly basis.
Jigsaw uses a non-standard ransom payment system
The Check Point team claims to have identified a weakness not in the encryption process, but in how Jigsaw handles the ransom payment.
While other ransomware families use a Tor-based website to handle payments, Jigsaw just prints a Bitcoin wallet address on the victim’s PC via a special ransom note and tells the users to press the “I made a payment, now give me back my files!” button after they made the payment.
Pressing this button starts a request from the user’s PC to an online API that checks if a payment was received to that specific Bitcoin wallet.
Researchers find a weakness in the payment process
There’s a reason why most ransomware families handle payments on their own websites, and that’s because users can tamper with the responses that come back from the API.
Check Point created a tool that intercepts and mimics a positive API response. The tool gives Jigsaw this fake API response and the ransomware thinks the payment was made, starting the decryption process that ends with Jigsaw unlocking all encrypted files and deleting itself from the infected system.
The tool, which works with both newer and older Jigsaw versions, can be downloaded from here, and below are Check Point’s instructions for using it:
This decryption trick seems to have been originally discovered by Peter Kleissner, who tweeted about it last week.
User manual:
1. Unpack the JPS.zip file.
2. In the Jigsaw Puzzle Solver folder, right click ‘JPS.exe’ and click ‘run as administrator’.
3. Follow the instructions displayed on the screen.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.