There is a common misconception that all things Linux are bulletproof. The fact is, no software is infallible. When news of a Linux vulnerability hits, some Windows and Mac fans like to taunt users of the open source kernel. Sure, it might be in good fun, but it can negatively impact the Linux community’s reputation — a blemish, if you will.
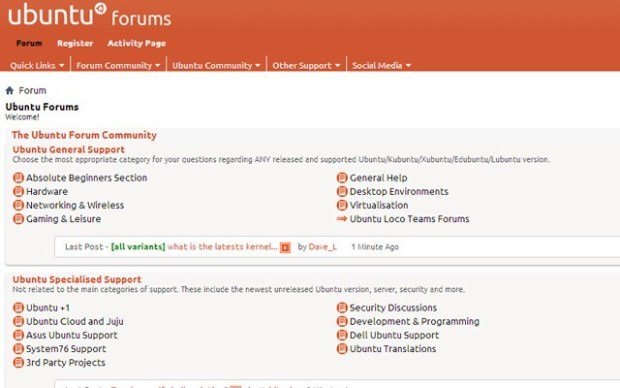
Today, Canonical announces that the Ubuntu forums have been hacked. Keep in mind, this does not mean that the operating system has experienced a vulnerability or weakness. The only thing affected are the online forums that people use to discuss the OS. Still, such a hack is embarrassing, as it was caused by Canonical’s failure to install a patch.
“There has been a security breach on the Ubuntu Forums site. We take information security and user privacy very seriously, follow a strict set of security practices and this incident has triggered a thorough investigation. Corrective action has been taken, and full service of the Forums has been restored. In the interest of transparency, we’d like to share the details of the breach and what steps have been taken. We apologize for the breach and ensuing inconvenience”,says Jane Silber, Chief Executive Officer, Canonical Ltd.
Silber further explains, “after some initial investigation, we were able to confirm there had been an exposure of data and shut down the Forums as a precautionary measure. Deeper investigation revealed that there was a known SQL injection vulnerability in the Forumrunner add-on in the Forums which had not yet been patched”.
Damn. All of this could have been avoided had a simple patch been implemented. It seems human error caused this calamity — people are often the weak link in security! But what was the hacker, or hackers, able to access? Silber shares that below.
What the attacker could access
- The attacker had the ability to inject certain formatted SQL to the Forums database on the Forums database servers. This gave them the ability to read from any table but we believe they only ever read from the ‘user’ table.
- They used this access to download portions of the ‘user’ table which contained usernames, email addresses and IPs for 2 million users. No active passwords were accessed; the passwords stored in this table were random strings as the Ubuntu Forums rely on Ubuntu Single Sign On for logins. The attacker did download these random strings (which were hashed and salted).
What the attacker could not access
- We know the attacker was NOT able to gain access to any Ubuntu code repository or update mechanism.
- We know the attacker was NOT able to gain access to valid user passwords.
- We believe the attacker was NOT able to escalate past remote SQL read access to the Forums database on the Forums database servers.
- We believe the attacker was NOT able to gain remote SQL write access to the Forums database.
- We believe the attacker was NOT able to gain shell access on any of the Forums app or database servers.
- We believe the attacker did NOT gain any access at all to the Forums front end servers.
- We believe the attacker was NOT able to gain any access to any other Canonical or Ubuntu services.
OK Ubuntu forum users, you can take a deep breath and relax. While it sucks that someone has your email address and IP address, passwords were not taken, meaning there is not much to worry about.
Canonical deserves kudos for acting swiftly and being transparent. It has since patched the vulnerability and hardened the security. Still, it deserves criticism for failing to install the patch. While human error is always a possibility, the company would be wise to audit its internal procedures to lessen the possibility of it happening again.
Source:https://betanews.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.